SAP Data Intelligence 3 on CaaS Platform 4.2 #
Installation Guide
SAP
SAP Data Intelligence 3 is the tool set to govern big amount of data. SUSE CaaS Platform 4 is the Kubernetes base that makes deploying SAP Data Intelligence 3 easy. This document describes the installation and configuration of SUSE CaaS Platform 4 and SAP Data Intelligence 3.
Disclaimer: Documents published as part of the SUSE Best Practices series have been contributed voluntarily by SUSE employees and third parties. They are meant to serve as examples of how particular actions can be performed. They have been compiled with utmost attention to detail. However, this does not guarantee complete accuracy. SUSE cannot verify that actions described in these documents do what is claimed or whether actions described have unintended consequences. SUSE LLC, its affiliates, the authors, and the translators may not be held liable for possible errors or the consequences thereof.
1 Introduction #
This guide describes the on-premises installation of SAP Data Intelligence 3 on SUSE CaaS Platform 4.2.
2 Prerequisites #
2.1 Hardware #
For sizing information, see in addition the SAP documentation: Sizing Guide for SAP Data Intelligence
At least eight nodes are needed for a Kubernetes cluster for production use.
Minimal requirements:
three master nodes
four worker nodes
one or two loadbalancers (these can be virtual machines)
For the installation of SUSE CaaSP 4.2, additional hosts are needed:
Management host
Registry for storing container images
These can be virtual machines.
2.2 Software #
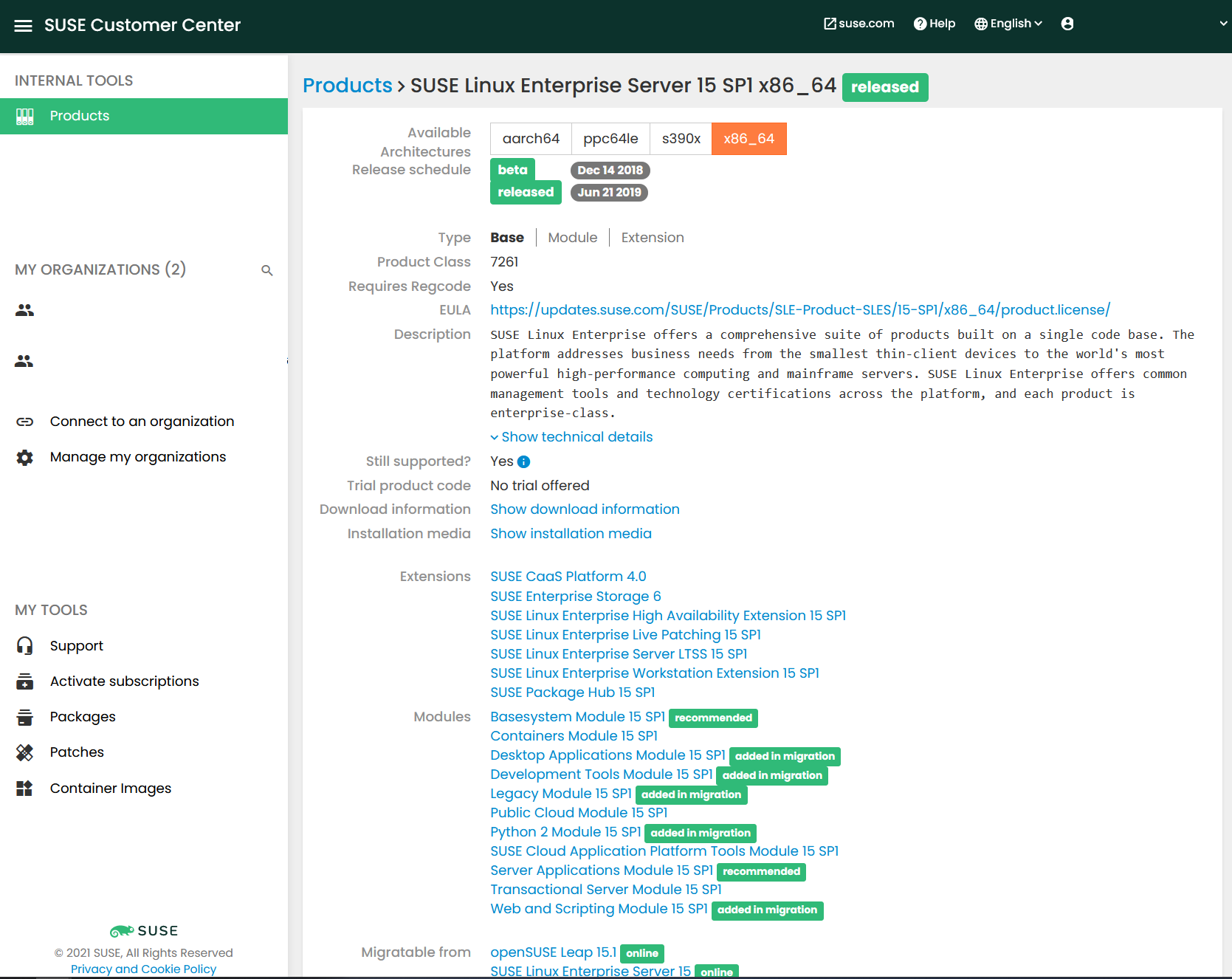
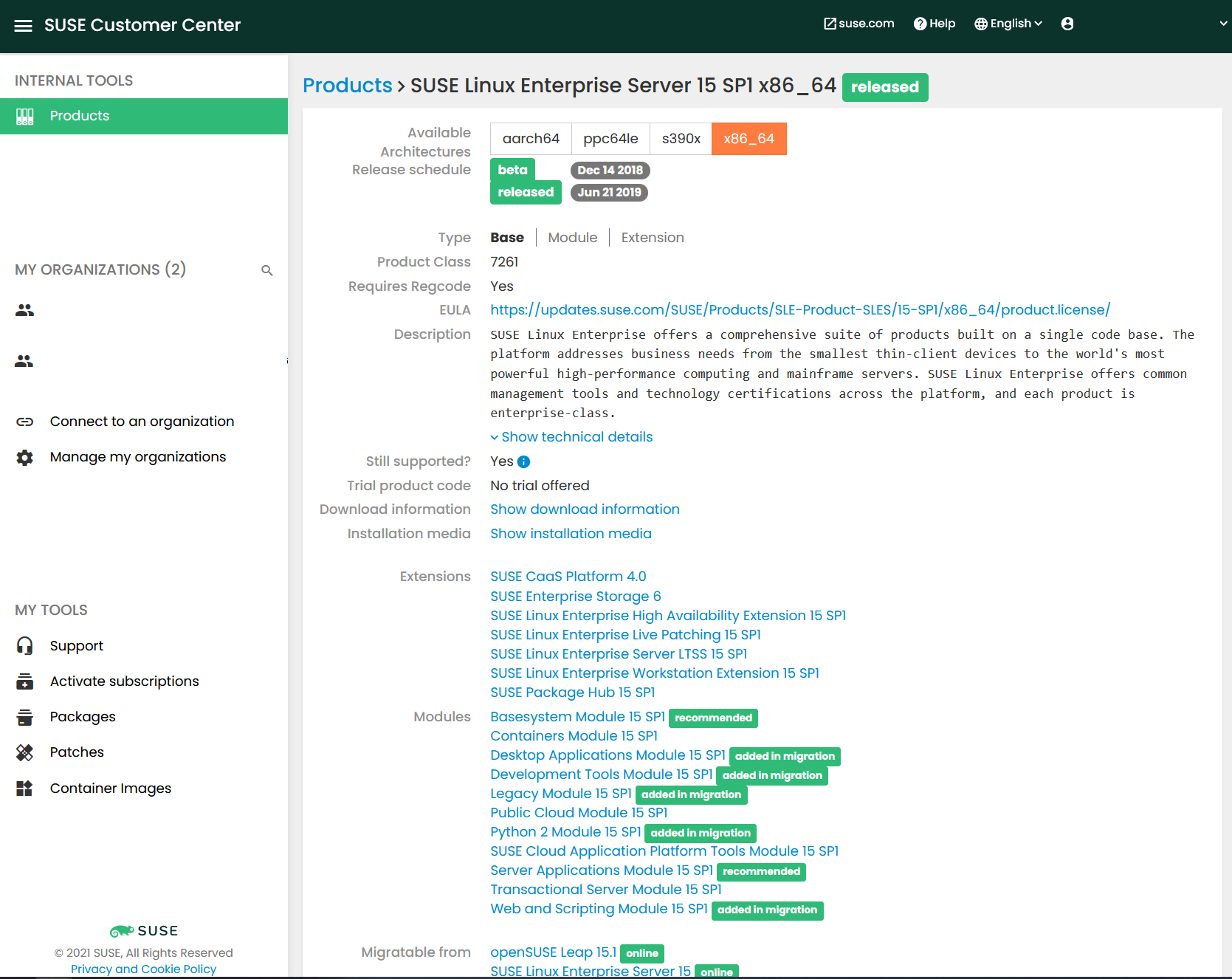
SUSE Linux Enterprise 15 SP1
SUSE CaaSP 4.2
3 Installing SUSE CaaSP 4.2 #
3.1 Documentation #
SUSE CaaS Platform 4.2 is documented here:
3.2 Preparations #
On all the nodes, install SUSE Linux Enterprise 15 SP1 or higher, as per the documentation for CaaS Platform 4.2.
On each respective node, the following modules or products are required.
Management host:
SUSE Linux Enterprise 15 SP1
SUSE Linux Enterprise 15 SP1 Containers Modules
SUSE Linux Enterprise 15 SP1 Public Cloud
SUSE CaaSP 4
Kubernetes master nodes:
SUSE Linux Enterprise 15 SP1
SUSE Linux Enterprise 15 SP1 Public Cloud
SUSE CaaSP 4
Kubernetes worker nodes:
SUSE Linux Enterprise 15 SP1
SUSE Linux Enterprise 15 SP1 Public Cloud
SUSE CaaSP 4
Loadbalancer host:
SUSE Linux Enterprise Server for SAP applications 15 SP1
or
SUSE Linux Enterprise 15 SP1 plus High Availability Extension
3.3 Installing the SUSE CaaSP 4 cluster nodes #
Install SUSE Linux Enterprise 15 SP1.
NoteUse the "Expert Partitioner" to disable and remove any automatically-configured swap partitions on the Kubernetes nodes.
See the relevant product documentation:
3.4 Installing the loadbalancer for the Kubernetes cluster #
Install SUSE Linux Enterprise 15 SP1
Install
ha-proxyornginxConfigure the loadbalancer
See the relevant product documentation:
3.5 Installing the management workstation #
Install SUSE Linux Enterprise 15 SP1
Add the necessary SUSE Linux Enterprise 15 SP1 modules: value
$ sudo SUSEConnect -r CAASP_REGISTRATION_CODE $ sudo SUSEConnect -p sle-module-containers/15.1/x86_64 $ sudo SUSEConnect -p caasp/4.0/x86_64 -r CAASP_REGISTRATION_CODE $ sudo SUSEConnect -p sle-module-python2/15.1/x86_64
3.6 Bootstrapping the SUSE CaaSP 4 cluster #
Run the
skubatool for initialization of the cluster.Make sure that
sshis working between all nodes without using passwords, and configuressh-agent.$ eval `ssh-agent` $ ssh-add <path to key>
$ skuba cluster init --control-plane <LB IP/FQDN> my-cluster
Bootstrap the cluster:
$ cd my-cluster $ skuba node bootstrap --target <IP/FQDN> <NODE NAME>
Add additional master nodes:
$ cd my-cluster $ skuba node join --role master --target <IP/FQDN> <NODE NAME>
Repeat this for all the master nodes.
Add the worker nodes:
$ cd my-cluster $ skuba node join --role worker --target <IP/FQDN> <NODE NAME>
Repeat this for all worker nodes.
Finally, check the cluster status.
$ cd my-cluster $ skuba cluster status $ cp -av ~/my-cluster/admin.conf ~/.kube/config $ kubectl get nodes -o wide
4 Adding secure private Docker Registry for container images #
This step is optional if you already have a private secure Docker Registry. If you skip this chapter, follow the instructions in Section 5, “SUSE Enterprise Storage”.
To satisfy the requirements for SAP Data Intelligence 3, you also need a Docker Registry. The easiest way to build and manage one is using the Harbor project.
To this end, you need to create a dedicated server for your Docker registry and the Harbor stack.
As Docker only allows characters within the range [a-z],[A-Z],[0-9] and '-' for domain names, make sure that your FQDN does not contain any other characters.
In our example, the server will be connected to a local bridge which provides
common services (DNS, SMT, Docker-registry) for the SAP Data Intelligence stack.
The FQDN of this server will be harbor-registry.example.com.
4.1 Prerequisites #
Find the prerequisites for Harbor here: Harbor Installation Prerequisites
Before you can set up Harbor, you need to install Docker and Docker Compose.
To install Docker, run:
# zypper in -y docker
To install Docker Compose, you must download the executable from its GitHub repository and save it into a directory within your $PATH.
For example, run:
# curl -L "https://github.com/docker/compose/releases/download/1.25.5/docker-compose-$(uname -s)-$(uname -m)" -o /usr/local/bin/docker-compose # chmod +x /usr/local/bin/docker-compose # ln -s /usr/local/bin/docker-compose /usr/bin/docker-compose
The next steps will generate the certificates used to make Harbor secure. These can also be found in the document Configure HTTPS Access to Harbor.
First, generate a CA certificate private key:
# openssl genrsa -out ca.key 4096
Then, generate a certificate with the given key for your domain.
NoteFor all further steps, replace <FQDN> with your fully qualified domain name. In our example, this would be
harbor-registry.example.com.# openssl req -x509 -new -nodes -sha512 -days 3650 \ -subj "/C=DE/ST=BW/O=SUSE/CN=<FQDN>" \ -key ca.key \ -out ca.crt
Your CA certificate is now ready for use.
Next, you must generate a server certificate as follows:
# openssl genrsa -out <FQDN>.key 4096
Generate a certificate signing request (CSR):
# openssl req -sha512 -new \ -subj "/C=DE/ST=BW/O=SUSE/CN=<FQDN>" \ -key <FQDN>.key \ -out <FQDN>.csr
Create an
x509 v3extension file with the following content:authorityKeyIdentifier=keyid,issuer basicConstraints=CA:FALSE keyUsage = digitalSignature, nonRepudiation, keyEncipherment, dataEncipherment extendedKeyUsage = serverAuth subjectAltName = @alt_names [alt_names] DNS.1=<FQDN> DNS.2=<hostname>
Use the extension file to generate a certificate:
# openssl x509 -req -sha512 -days 3650 \ -extfile v3.ext \ -CA ca.crt -CAkey ca.key -CAcreateserial \ -in $fqdn.csr \ -out $fqdn.crt
Copy the
.crtand.keyfiles to the system’s certificate directory:# cp <FQDN>.crt /etc/pki/trust/anchors/ # cp <FQDN>.key /etc/pki/trust/anchors/
As Docker interprets
.crtfiles as CA certificates and.certfiles as clients, you must convert your.crtfile as follows:# openssl x509 -inform PEM -in <FQDN>.crt -out $<FQDN>.cert
You can now copy the newly created certificates to your Docker certificate directory. If the directory
/etc/docker/certs.ddoes not exist, create it.# mkdir /etc/docker/certs.d/<FQDN> # cp <FQDN>.cert /etc/docker/certs.d/<FQDN>/ # cp <FQDN>.key /etc/docker/certs.d/<FQDN>/ # cp ca.crt /etc/docker/certs.d/<FQDN>/
NoteIf you want to expose your registry on a port other than 443, you must create a directory
/etc/docker/certs.d/<FQDN>:<Port>and copy the certificates to this directory instead.To introduce the certificates to Docker, restart the Docker daemon:
# systemctl restart docker
4.2 Setting up Harbor #
Fetch the Harbor installer and extract its contents:
# wget https://github.com/goharbor/harbor/releases/download/v2.1.1/harbor-online-installer-v2.1.1.tgz # tar xvf harbor-online-installer-v2.1.1.tgz
Enter the extracted directory:
# cd harbor
Within this directory, you should find a file called
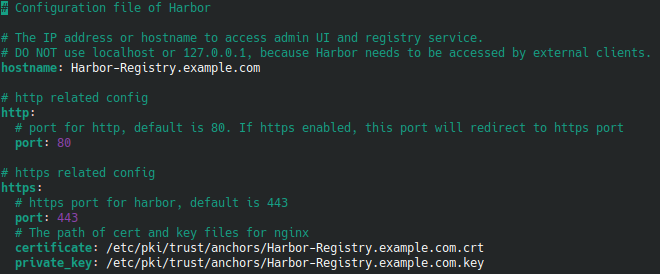
harbor.yml.tmpl. It contains the configuration for the Harbor Registry and must be adjusted.First, edit the
hostnamefield and enter your FQDN.Next, update the HTTPS configuration. The subentries
certificateandprivate_keymust be adjusted so they point to the.crtand.keyfiles you created in Section 4.1, “Prerequisites”.This should look like the following:
Figure 1: Harbor Configuration File #If you want to expose registry on a port other than 443, you can change the
portsub-entry to match your desired port.You should also change the
administratorpassword for Harbor, which by default is defined in the fieldharbor_admin_password: Harbor12345.The last field to mention is
data_volume: /data, which defines where all Harbor data will be stored. If you want Harbor to store the data somewhere else, enter the path to the desired directory here.
When done, save your changes, and rename the file by removing the
.tmplsuffix:# mv harbor.yml.tmpl harbor.yml
As Harbor uses
nginxas a reverse proxy for all services, you must run thepreparescript to configure it correctly:# ./prepare
You can now start the needed containers using Docker Compose:
# docker-compose up -d
Harbor should now be up and running.
Distribute the CA certificate to all Kubernetes nodes, so they can access the registry. Run the following commands on all the nodes:
# scp <FQDN>:/etc/docker/certs.d/<FQDN>/ca.crt /etc/docker/certs.d/<FQDN>/<FQDN>.crt # systemctl restart docker
For the example <FQDN> of
harbor-registry.example.com, this looks like the following:# scp harbor-registry.example.com:/etc/docker/certs.d/harbor-registry.example.com/ca.crt /etc/docker/certs.d/harbor-registry.example.com/harbor-registry.example.com.crt # systemctl restart docker
4.3 Verifying configuration and setting up Harbor projects #
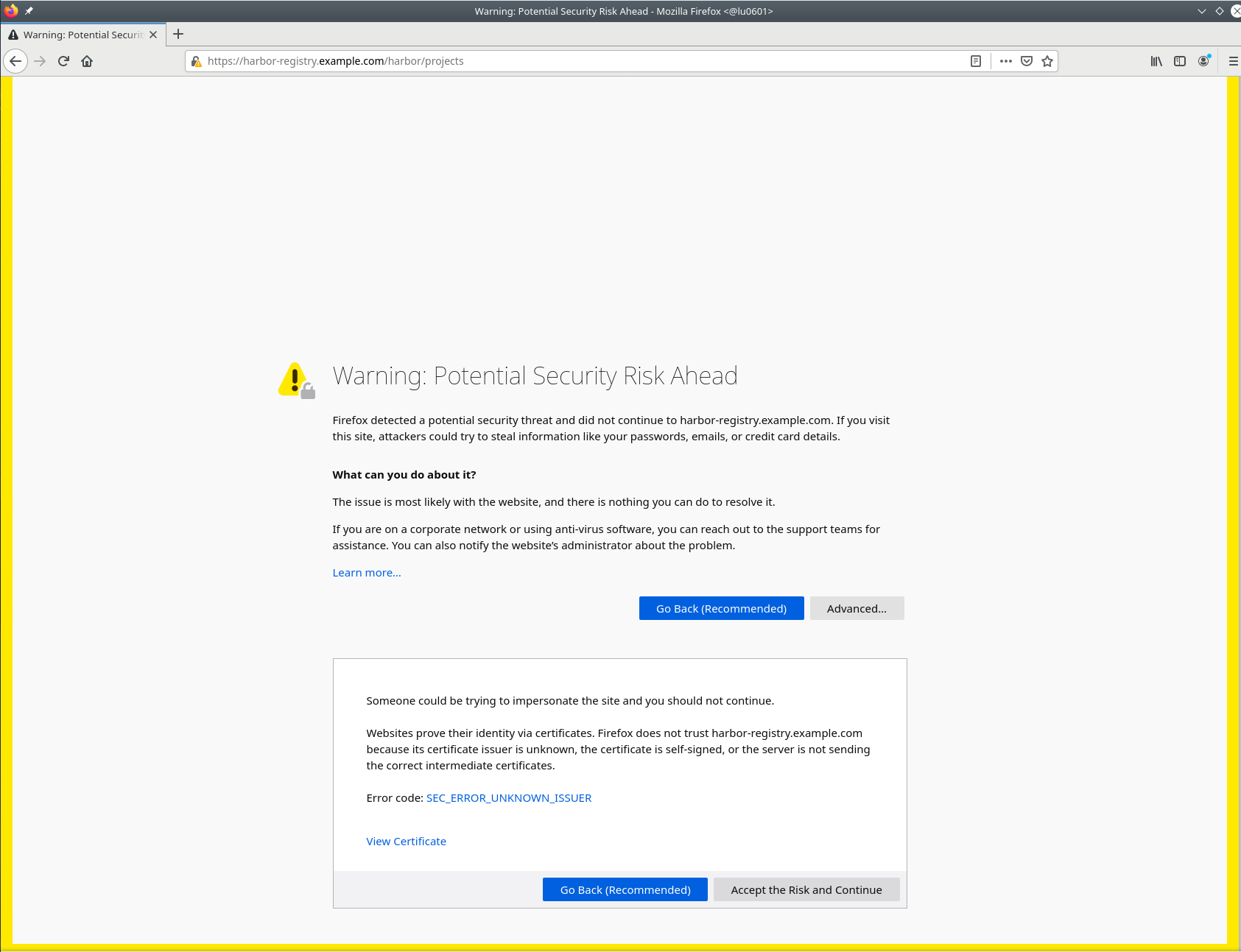
To verify Harbor is running, you may access its Web front-end by visiting https://<FQDN> from your browser.
You may get a warning about an insecure certificate, which looks similar to this:
You can toggle the lower box by clicking Advanced…
Then click Accept the Risk and Continue.
You will be redirected to the login page of your Harbor registry.
Enter admin as the user name and enter the password specified in the harbor.yml
file. By default, this is "Harbor12345".
By default, you will be redirected to the project page which holds the "libraries" project.
You should also check if the Docker clients on your Kubernetes nodes can access the registry. To do so, run:
# docker login <FQDN>
You will be prompted to enter a user name and password. Use admin for the
user name, and the password you set in harbor.yml (default: "Harbor12345").
If Docker can access the registry, you will see a message displayed that states "Login Succeeded" or similar.
If your machines cannot resolve the FQDN of your registry, edit your
/etc/hosts file and add a line with the following information:
<IP> <FQDN> <Hostname>
In our example, this will look as follows:
192.168.180.100 harbor-registry.example.com harbor-registry
Create the namespaces on your registry that are needed for SAP Data Intelligence 3:
com.sap.hana.containercom.sap.datahub.linuxx86_64com.sap.datahub.linuxx86_64.gcc6consulelasticsearchfabric8google_containersgrafanakibanapromvorakaniko-projectcom.sap.bds.docker
5 SUSE Enterprise Storage #
This step is optional if you already have a storage that provides RBD volumes and/or S3 buckets. If you skip this chapter, follow the instructions in Section 6.4, “Installing SAP Data Intelligence 3”.
An on-premises installation of SAP Data Intelligence 3 requires SUSE Enterprise Storage 5.5 or higher.
If you plan to use SUSE Enterprise Storage not only for your Kubernetes dynamic
storage class but also for your Kubernetes control plane (virtualized or
not), you should reserve enough resources to address the etcd
requirements specified in the etcd Hardware recommendations
The following steps will deploy a minimalist, virtualized, test-oriented instance of SUSE Enterprise Storage 6. In our example, we will build a four-nodes (1 Admin + 3 OSD) Ceph cluster.
5.1 Before starting #
Obtain registration codes for SUSE Linux Enterprise Server 15 SP1 and SUSE Enterprise Storage from https://scc.suse.com, or have SMT/RMT properly set up and already mirroring these products.
5.2 Setting up the machines #
Download the installation media for SUSE Linux Enterprise Server 15 SP1, for example from:
SUSE Linux Enterprise Server:
SUSE Enterprise Storage:
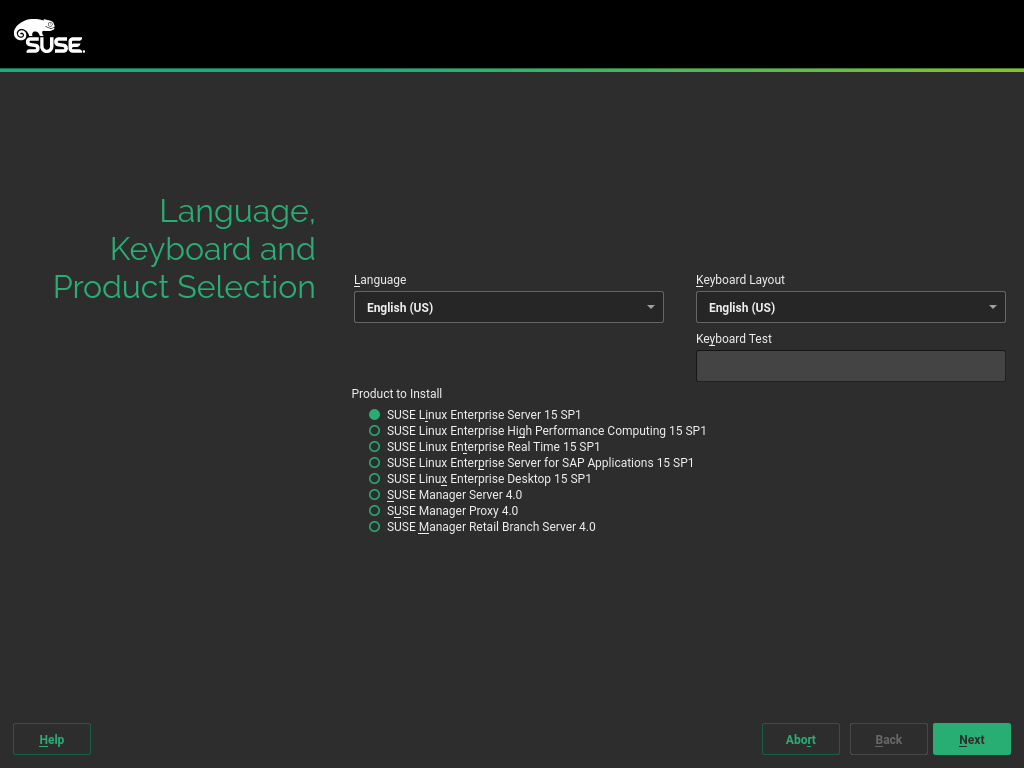
To install the software, boot the destination machine and insert the installation media. After boot, you should see a screen like this:
Figure 7: SLES Setup Initial Page #Select your preferred language and keyboard layout. Then select the option "SUSE Linux Enterprise Server 15 SP1" and click the "Next" button.
You need to agree to the license agreement. Click "Next" again.
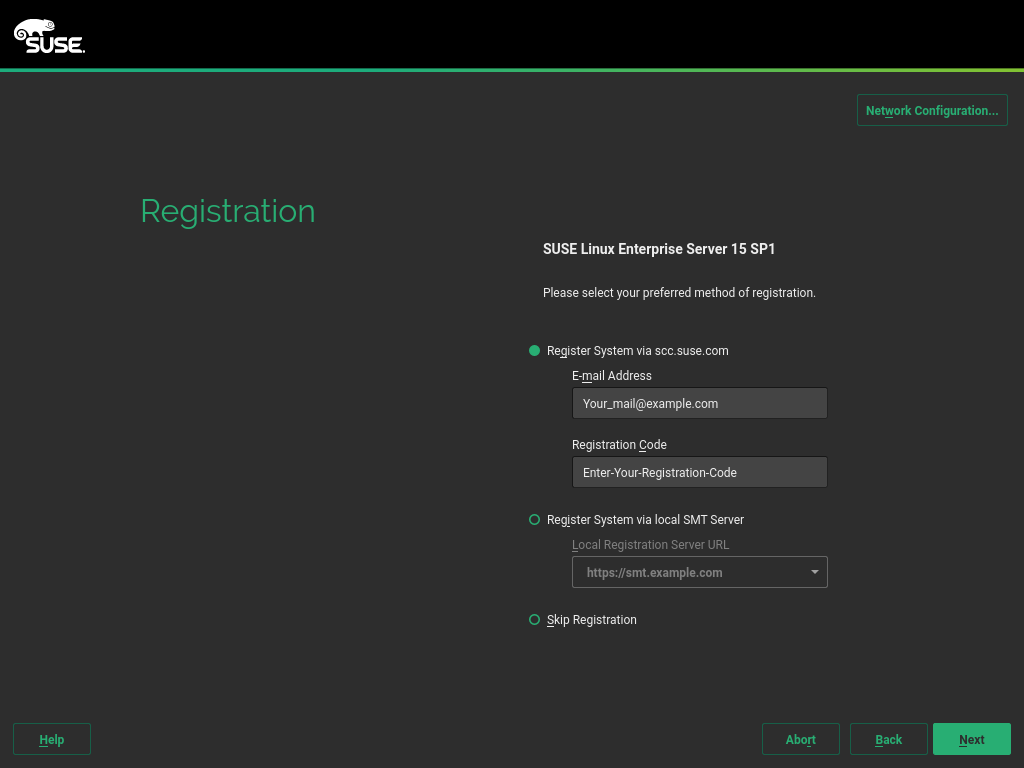
The registration screen should be displayed.
Figure 8: SLES Setup Registration Page #Now, either enter your e-mail and the registration code you collected from the SCC as described in the previous chapter, or select "Register System via local SMT Server" and enter the URL of your SMT server.
If required, you can use the Network Configuration button at the top right to configure your network settings.
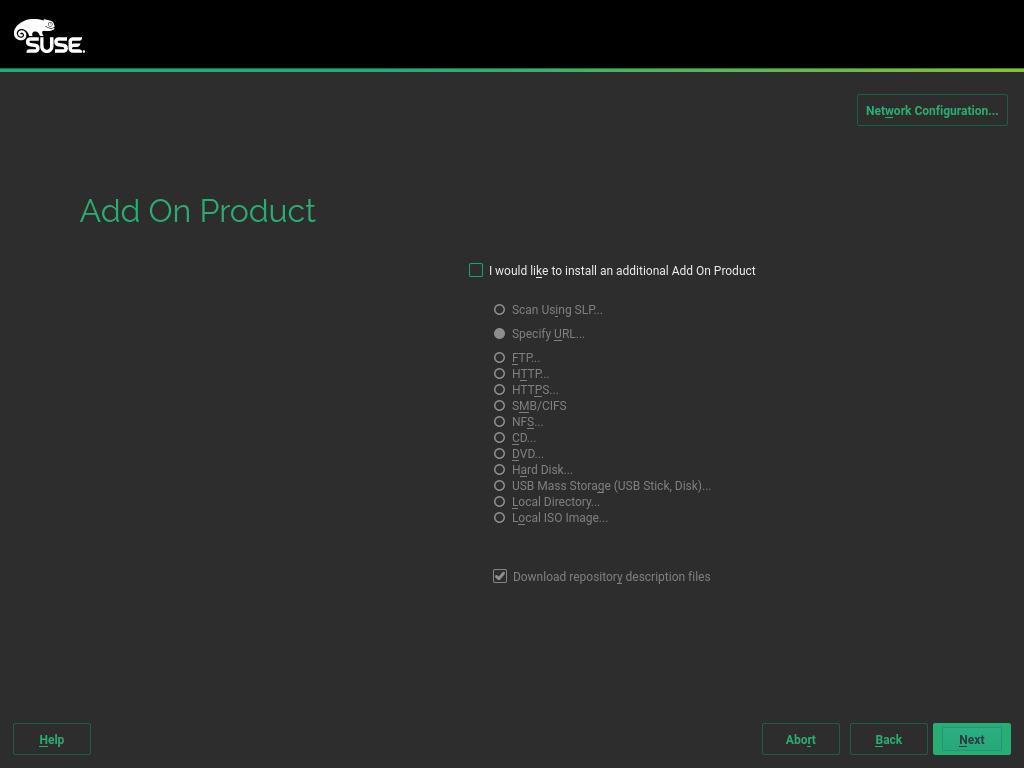
Figure 9: SLES Setup Add On Product Page #When the system is registered, you will see the "Add On Product" page. You can skip it by clicking the "Next" button again.
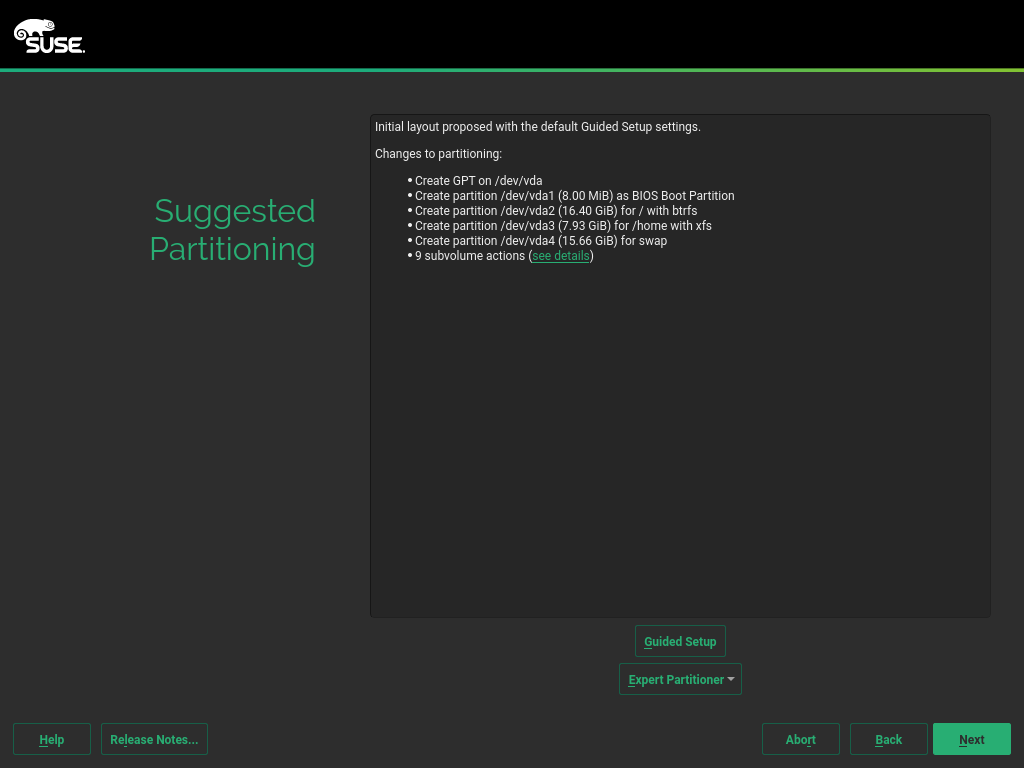
The "Suggested Partitioning" page will be displayed. You may edit the proposed partitioning if needed. For our example, we accept the proposal and continue by clicking the "Next" button.
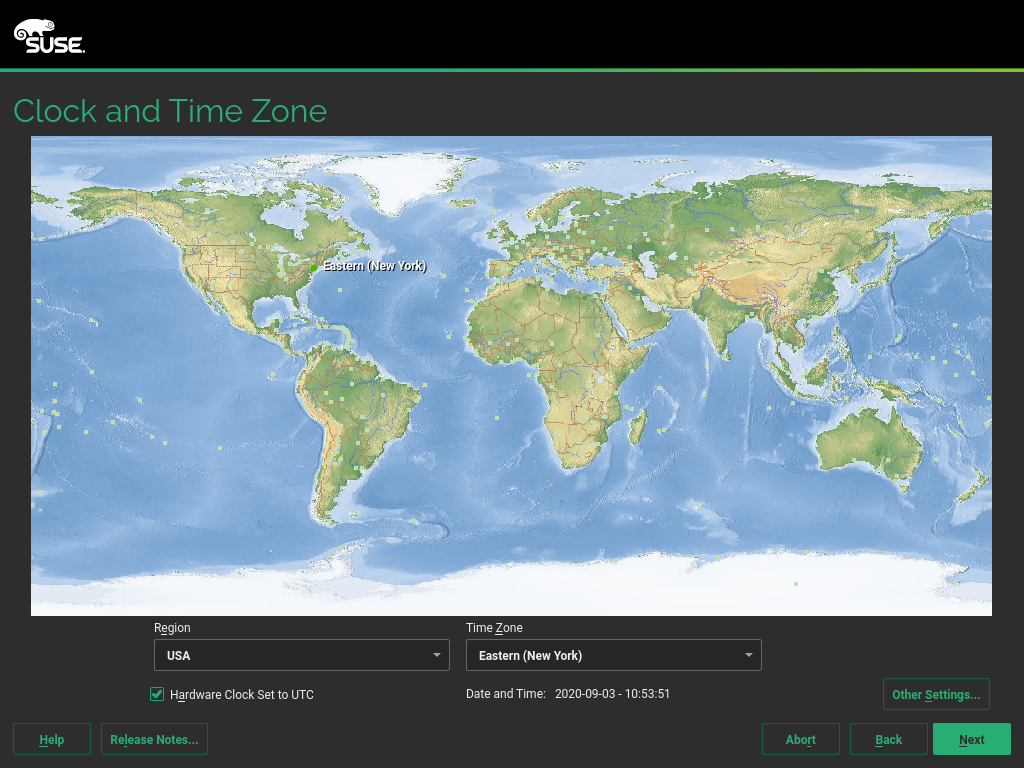
Figure 10: SLES Setup Partitioning Page #On the "Clock and Time Zone" page, you should select your preferred Region and Time Zone.
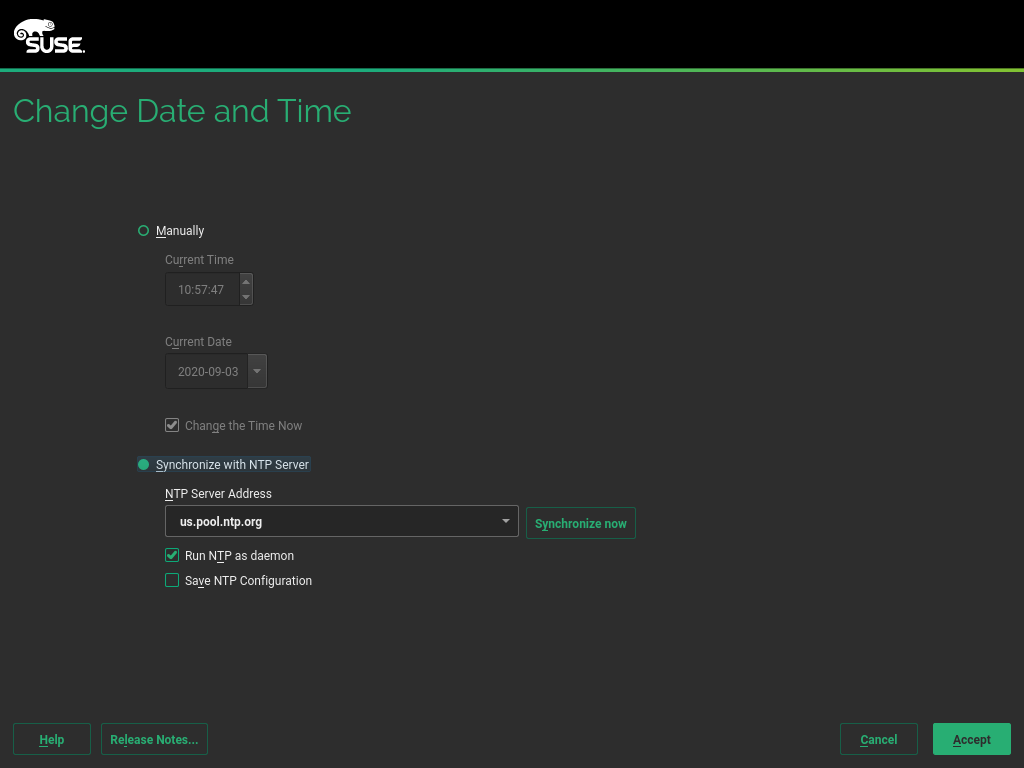
Figure 11: SLES Setup Clock and Time Zone Page #Click "Other Settings" to open the "Change Date and Time" page. Select the "Synchronize with NTP-Server" option. Then select an NTP server and click the "Accept" button.
Figure 12: SLES Setup Change Date and Time Page #ImportantAll machines in the cluster must synchronize with the same NTP Server!
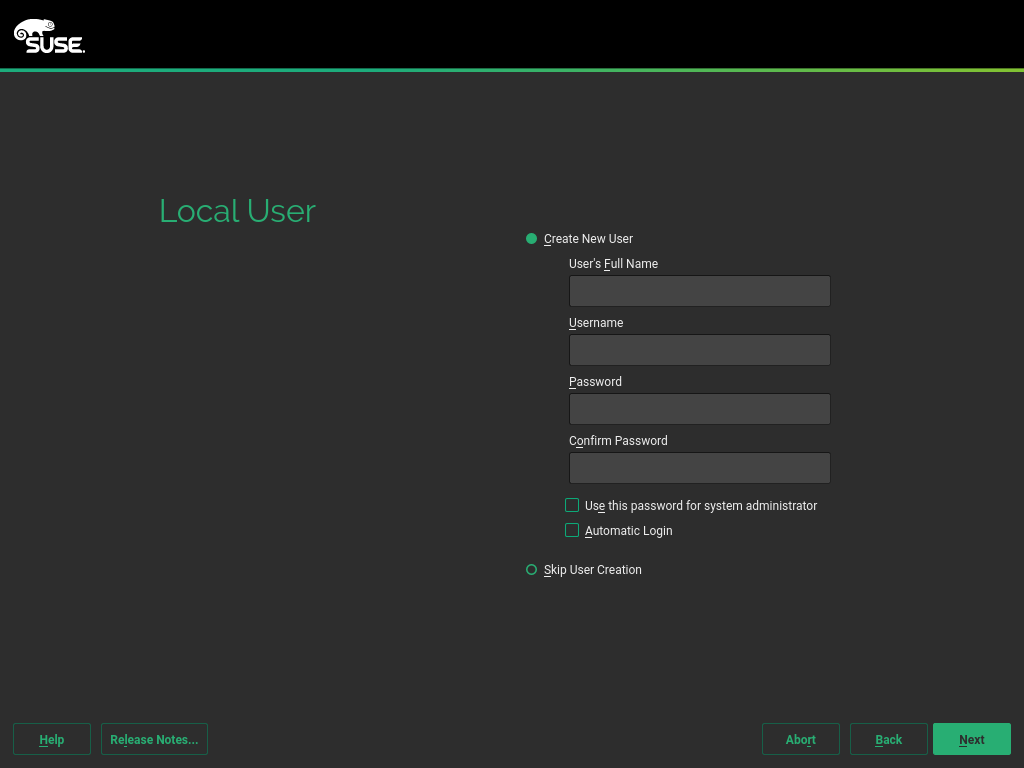
Next, you can create a user with name and password of your choice. When done, confirm and click "Next".
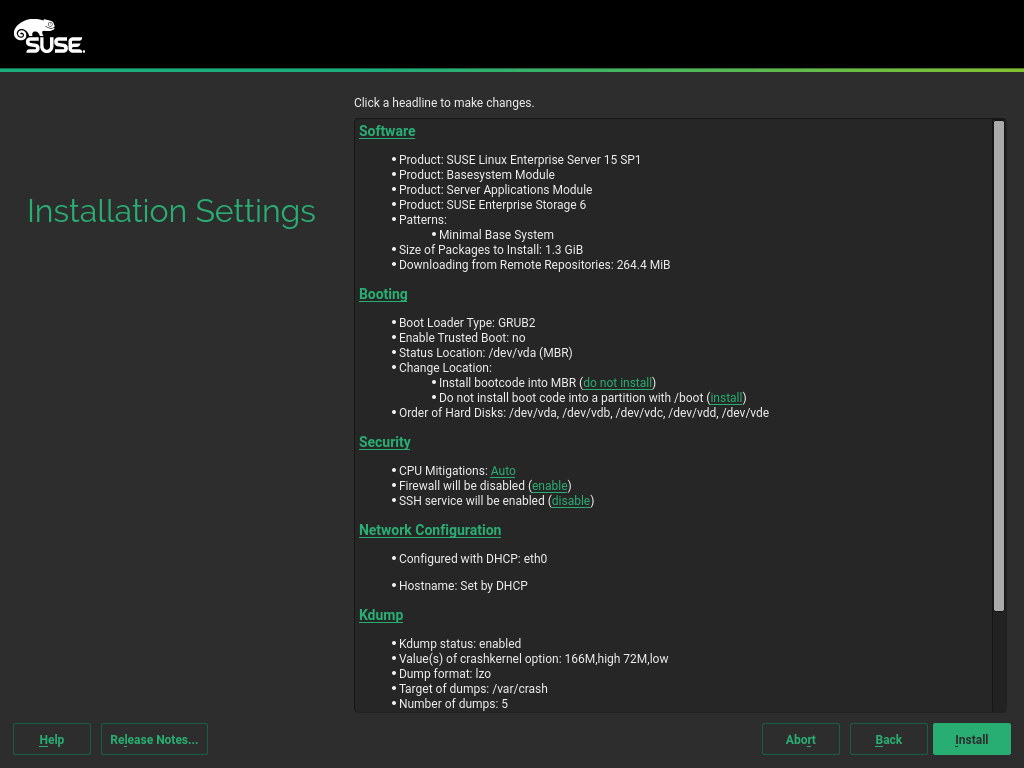
Figure 13: SLES Setup Create User Page #Now the "Installation Settings" page is displayed. Disable the firewall. To do so, click the "disable" button located behind "Firewall will be enabled".
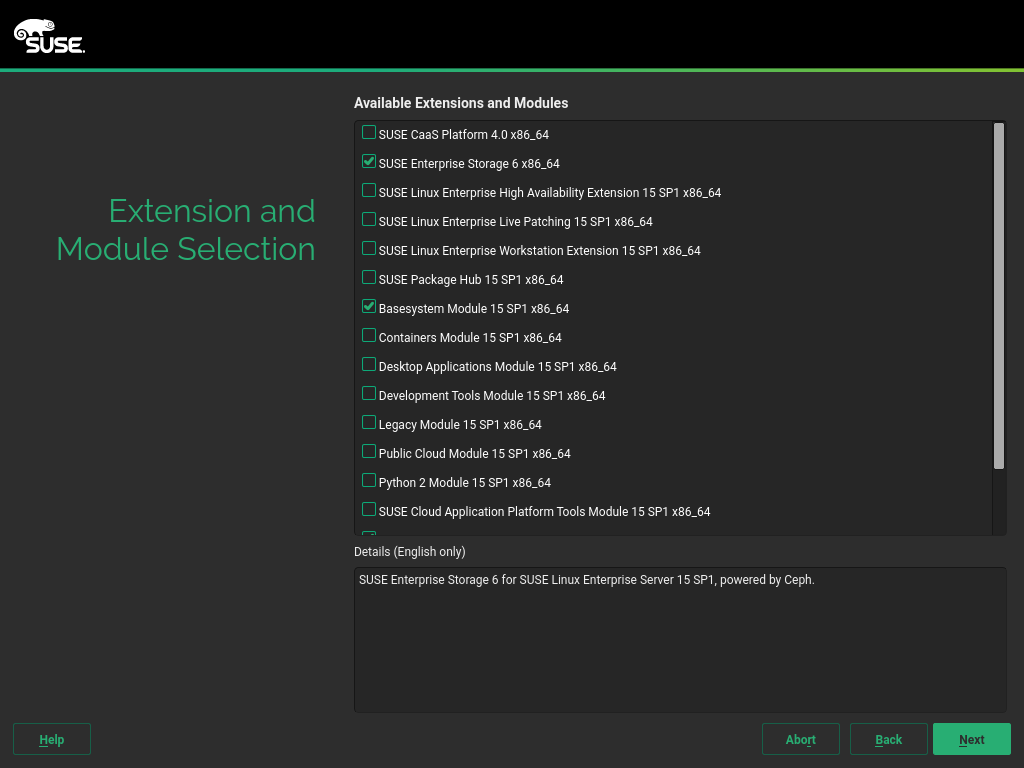
Figure 14: SLES Setup Installation Settings Page #To finalize the installation, go to "Extension and Module Selection" and select "SUSE Enterprise Storage 6 x86_64".
Figure 15: SLES Setup Extension Page #
Set up at least four machines the same way.
5.3 Setting up SUSE Enterprise Storage #
Check that your machines have the correct host names:
# hostname -f
This should output the FQDN of the machine. If this is not the case, you can use the following command to set the name:
# hostnamectl --set-hostname <FQDN>
For the document at hand, we use the following machine names:
admin.example.common1.example.common2.example.common3.example.com
To ensure that DNS resolution for these names works properly, you should edit
the /etc/hosts file on the nodes as follows:
127.0.0.1 localhost <Admin-IP> admin.example.com admin <Mon1-IP> mon1.example.com mon1 <Mon2-IP> mon2.example.com mon2 <Mon3-IP> mon3.example.com mon3
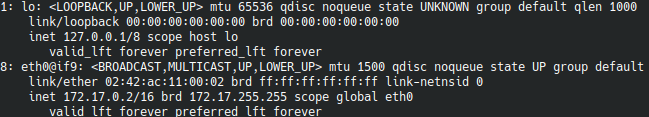
If you do not know the IP address of a machine, run:
$ ip a
This should output something similar to the following:
5.3.1 Preparing the nodes #
On the OSD Nodes, install
salt-minionanddeepsea:# zypper in -y salt-minion deepsea
On the Admin Node, install
salt-minion,salt-master, anddeepsea:# zypper in -y salt-minion salt-master deepsea
Set the Salt master on all machines by editing the associated line:
# echo "master: admin.example.com" > /etc/salt/minion
On the Admin node, enable the
salt-masterservice:# systemctl enable salt-master --now
Enable the
salt-minionservice on all nodes:# systemctl enable salt-minion --now
Now accept the Salt keys on the admin node:
# salt-key --accept-all -y
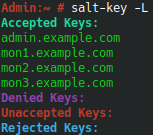
TipTo check the keys, use the command
salt-key -L. This should output something like:Figure 17: Salt Keys #Make all nodes DeepSea minions:
# echo "deepsea_minions: '*'" > /srv/pillar/ceph/deepsea_minions.sls
Synchronize your Salt minions:
# salt '*' saltutil.sync_all
Make sure your desired disks are all cleared. To this end, you can use:
# wipefs -a /dev/vdb
NoteBe aware that you might need to change the device (
vdb) here. Ensure you clear all disks on all nodes.Apply the cleared disks by using:
# salt '*' state.apply ceph.subvolume
5.3.2 Deploying the cluster #
You can watch the progress of the Ceph stages in a separate
terminal with the command deepsea monitor.
Now you can run the first stage of deploying the Ceph cluster.
First, prepare the cluster:
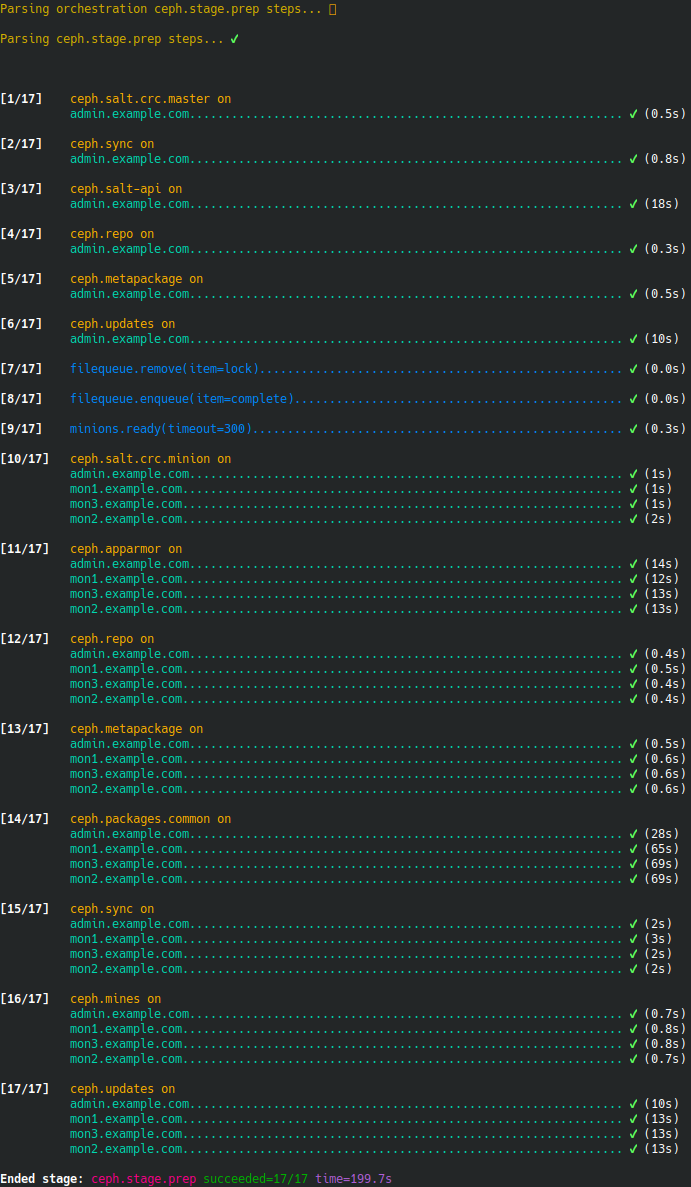
# salt-run state.orch ceph.stage.prep
The result for the preparation stage should look similar to this:
Figure 18: Cluster Deployment - Preparation #The next stage is collecting information about the nodes:
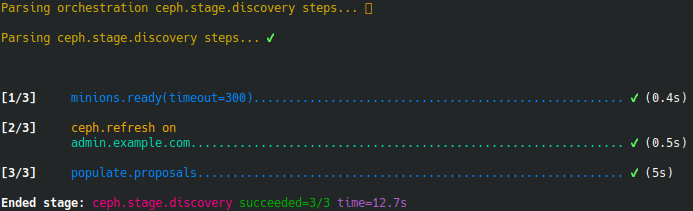
# salt-run state.orch ceph.stage.discovery
Figure 19: Cluster Deployment - Stage 1 #Before you can run the last three stages, you must provide a role configuration for the nodes. This will be stored in
/srv/pillar/ceph/proposals/policy.cfg. This example uses the following configuration:#General config config/stack/default/global.yml config/stack/default/ceph/cluster.yml #CEPH Cluster members cluster-ceph/cluster/admin.example.com.sls cluster-ceph/cluster/mon1.example.com.sls cluster-ceph/cluster/mon2.example.com.sls cluster-ceph/cluster/mon3.example.com.sls #CEPH Admin nodes role-admin/cluster/mon1.example.com.sls role-admin/cluster/mon2.example.com.sls role-admin/cluster/mon3.example.com.sls #CEPH Master node role-master/cluster/admin.example.com.sls #CEPH Manager nodes role-mgr/cluster/mon1.example.com.sls role-mgr/cluster/mon2.example.com.sls role-mgr/cluster/mon3.example.com.sls #CEPH Monitor nodes role-mon/cluster/mon1.example.com.sls role-mon/cluster/mon2.example.com.sls role-mon/cluster/mon3.example.com.sls #CEPH RGW nodes role-rgw/cluster/admin.example.com.sls role-rgw/cluster/mon1.example.com.sls role-rgw/cluster/mon2.example.com.sls role-rgw/cluster/mon3.example.com.sls #CEPH Storage nodes role-storage/cluster/admin.example.com.sls role-storage/cluster/mon1.example.com.sls role-storage/cluster/mon2.example.com.sls role-storage/cluster/mon3.example.com.sls
You can now safely deploy your configuration:
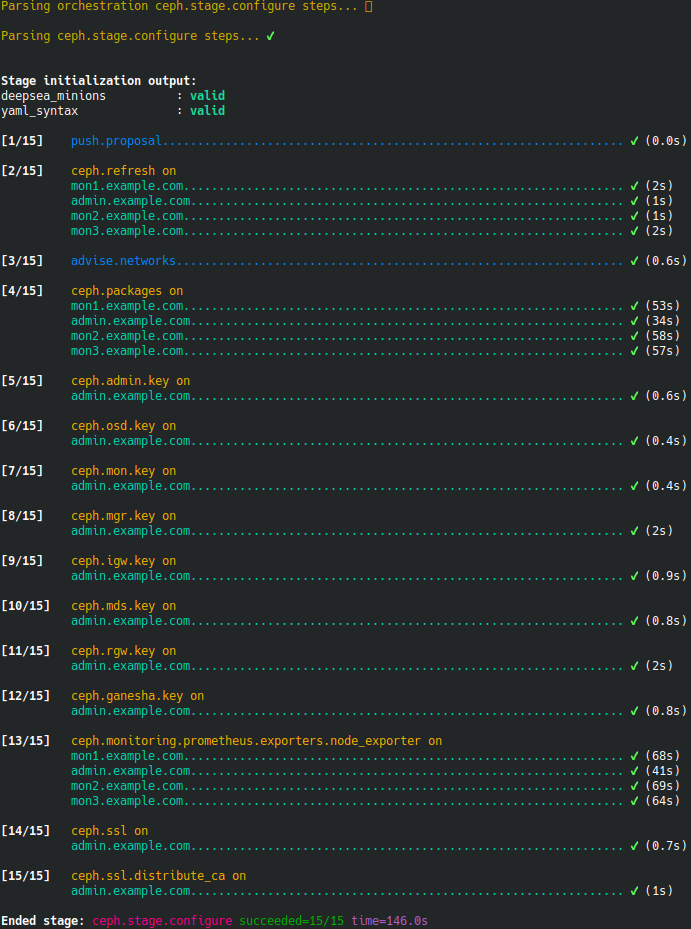
# salt-run state.orch ceph.stage.configure
Figure 20: Cluster Deployment - Stage 2 #Deploy your configuration to the cluster:
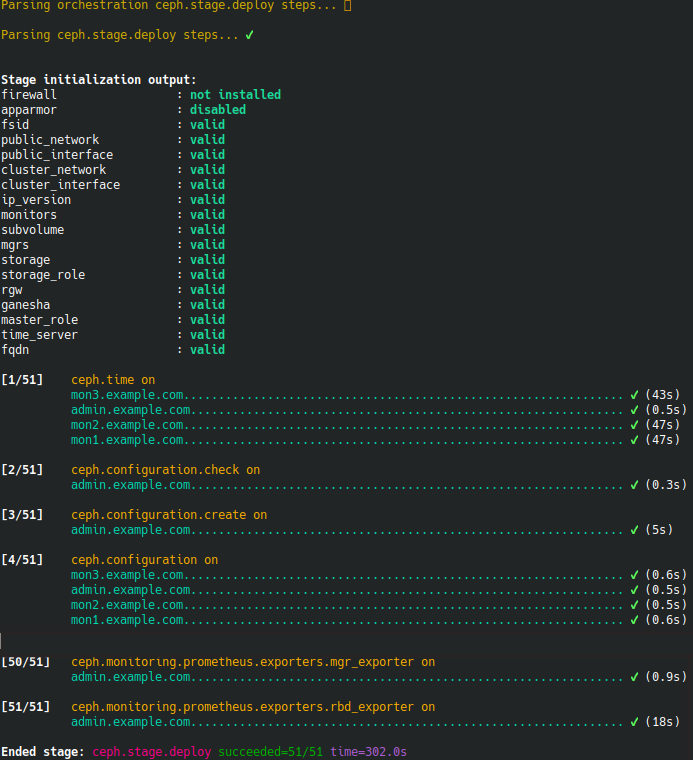
# salt-run state.orch ceph.stage.deploy
Figure 21: Cluster Deployment - Stage 3 #When the deployment stage has been successfully passed, check the cluster health to insure that all is running properly.
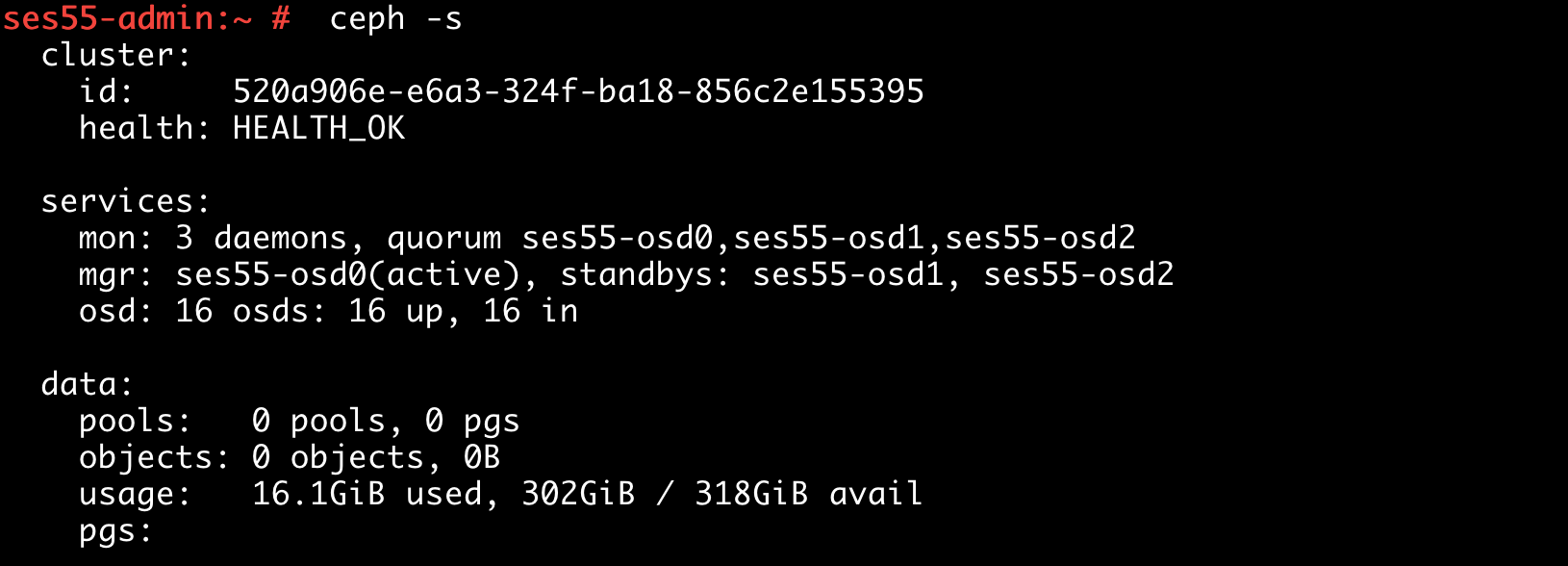
# ceph -s
Figure 22: Checking Cluster Health #The last stage to run is deploying the service roles, which were specified in the
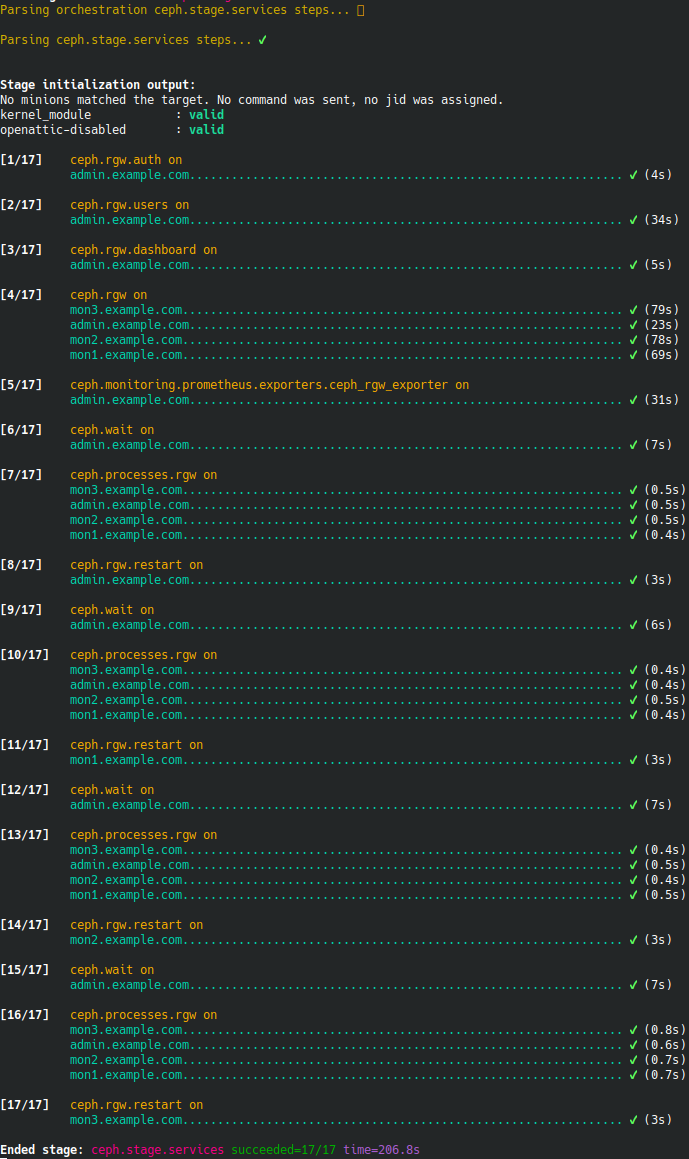
policy.cfgfile:# salt-run state.orch ceph.stage.services
Figure 23: Cluster Deployment - Stage 4 #
5.4 Access the dashboard and create a new pool #
After the Ceph cluster is up and running, you must create a pool for SAP Data Intelligence 3.
In our example, we will use the dashboard for this purpose.
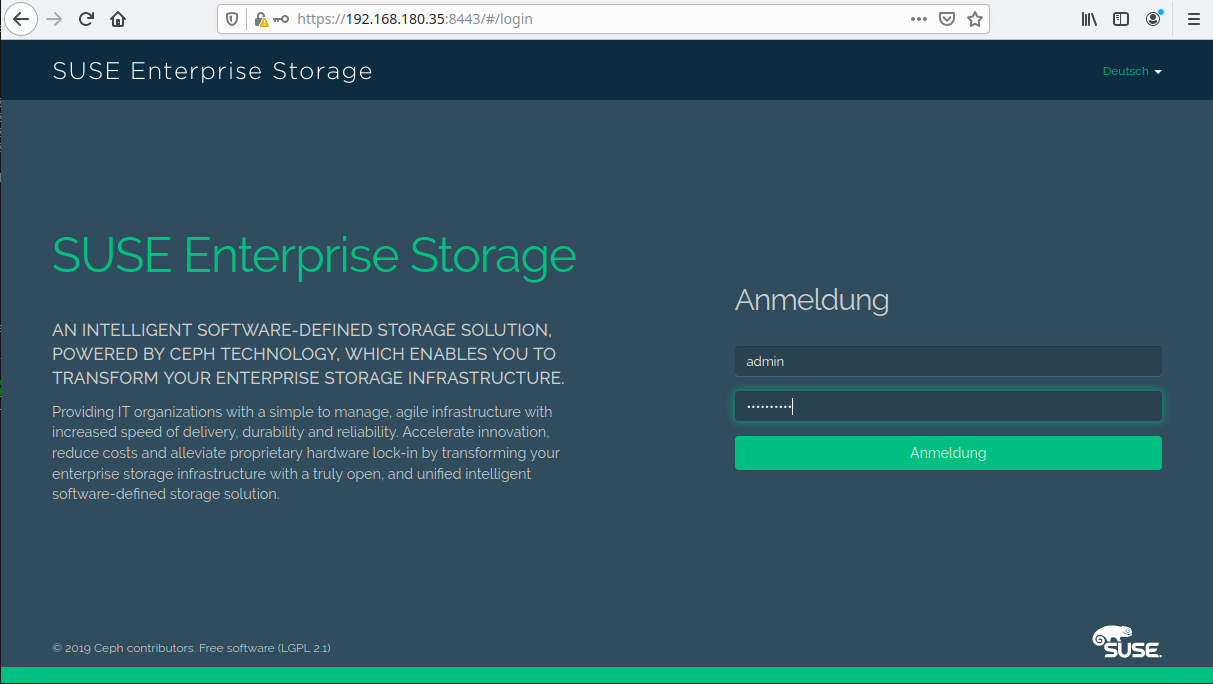
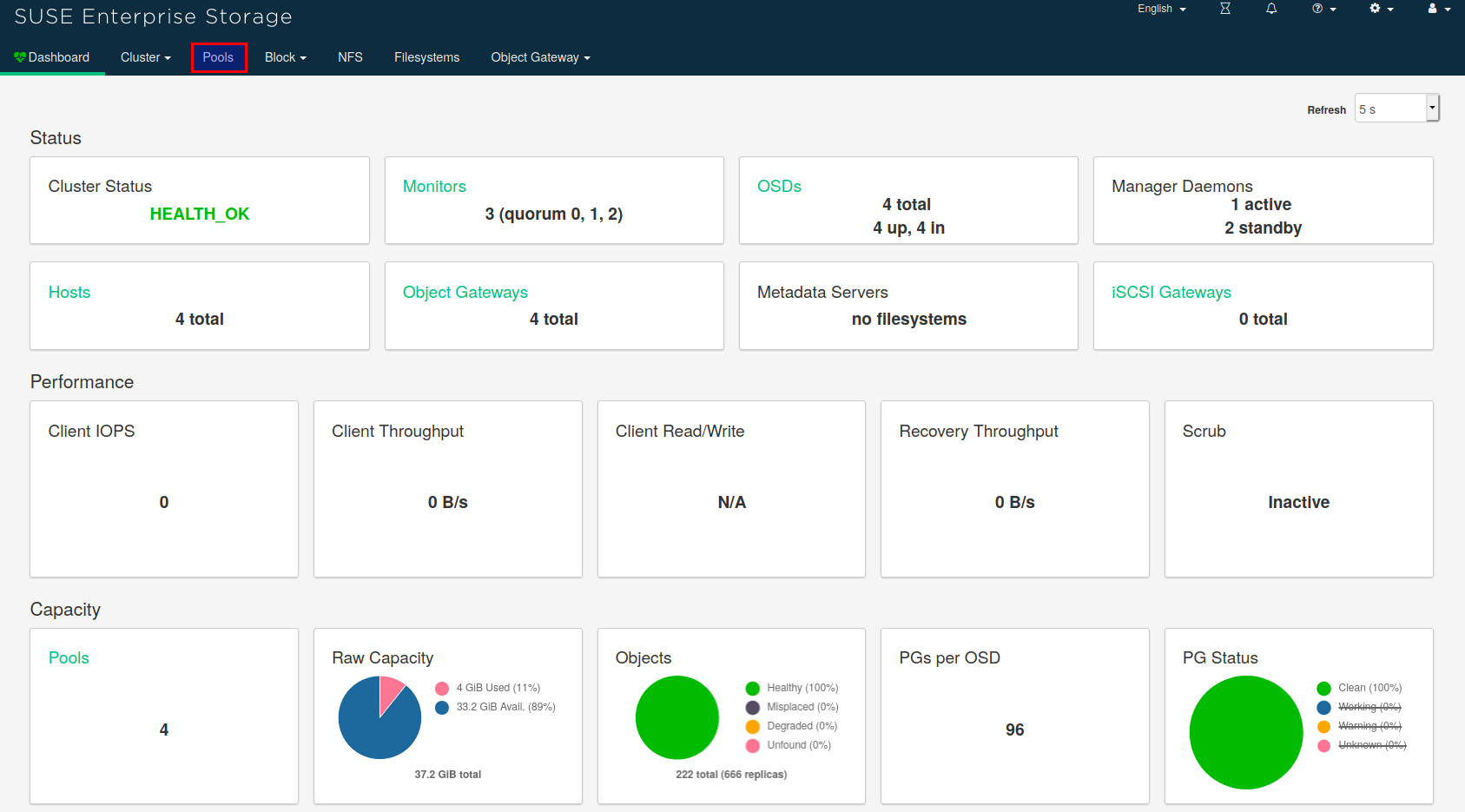
The dashboard is published by any of the monitor nodes. To access it, use a Web browser:
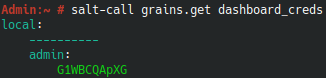
Figure 24: Cluster Dashboard #Get the credentials to log in by running the following command on the Admin Node:
# salt-call grains.get dashboard_creds
Figure 25: Cluster Dashboard Login #After logging in, the landing page should appear.
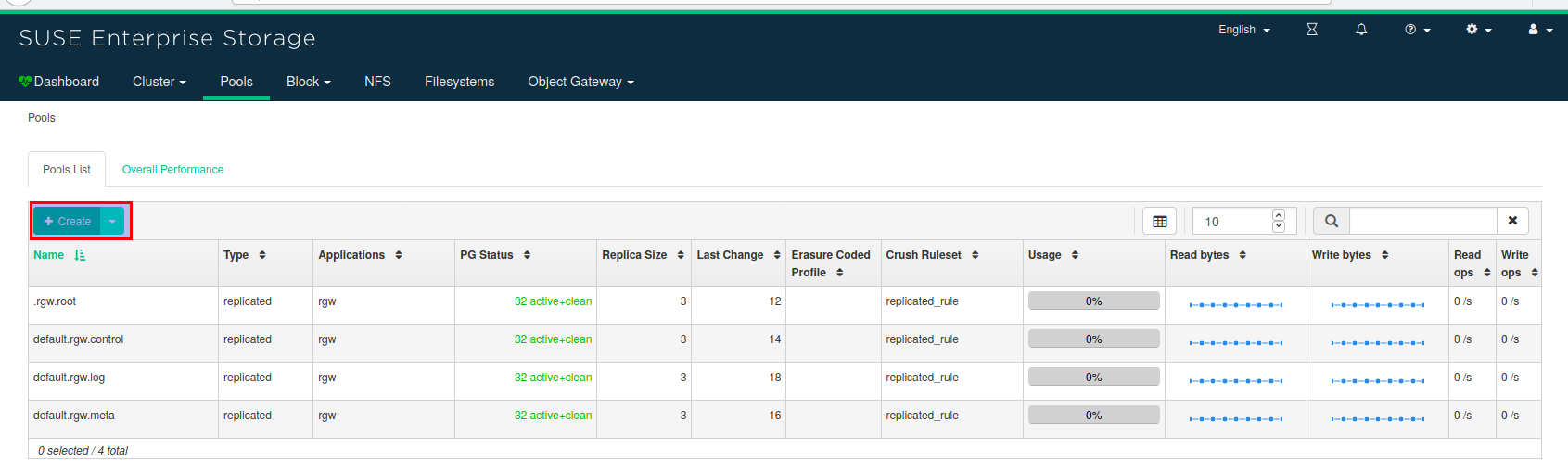
Select the "Pools" tab at the top of the page:
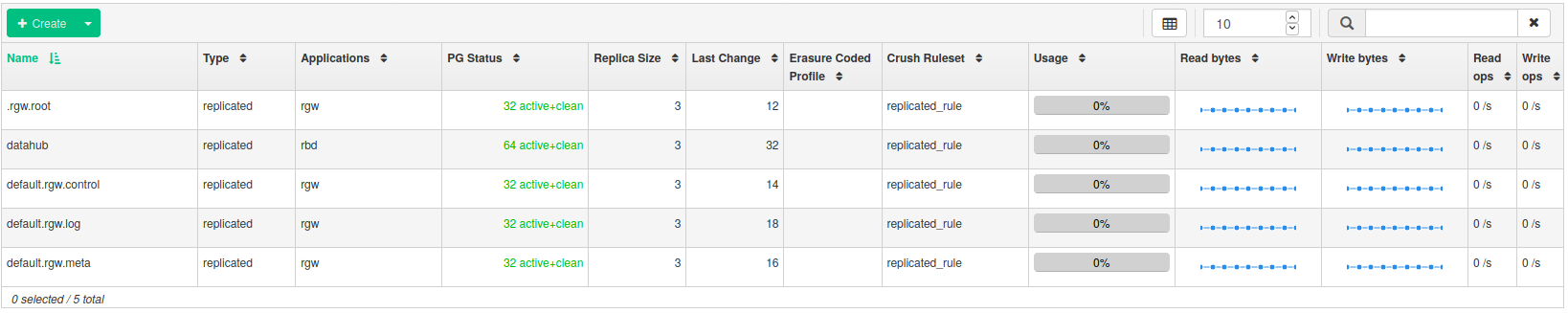
Figure 26: Cluster Dashboard Landing Page #The Pools page gives an overview of the currently defined pools.
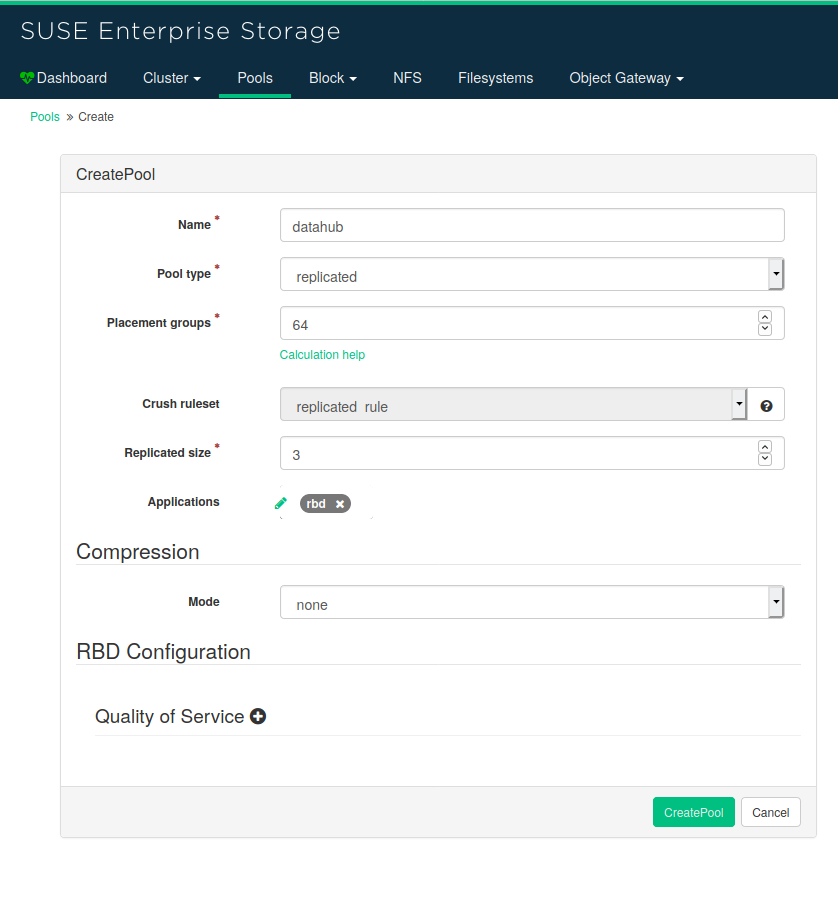
Click the "Create" button at the top of the table to create a new pool:
Figure 27: Cluster Dashboard Pools #Enter the name of the pool. As "Pool type", select
replicated.On the left side of "Applications", click the pencil symbol and select
rbd.Confirm the creation of the pool by clicking the "CreatePool" button at the bottom.
Figure 28: Cluster Dashboard Creating Pools #ImportantMake note of the name of the pool. It will be needed in Section 6.4.1.2, “Creating Storage Class”.
After this, the pools page is displayed again, and the newly created pool is shown in the table of pools.
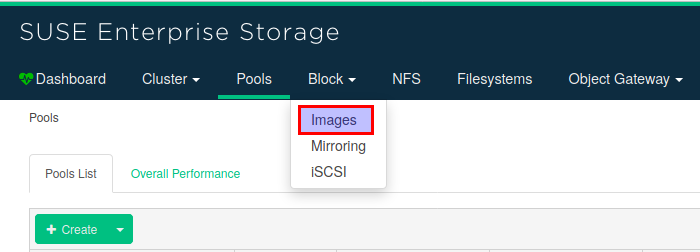
Figure 29: Cluster Dashboard New Pool #Now provide access to this pool through an RBD device. Go to the RDB overview page by selecting "Block→Images"
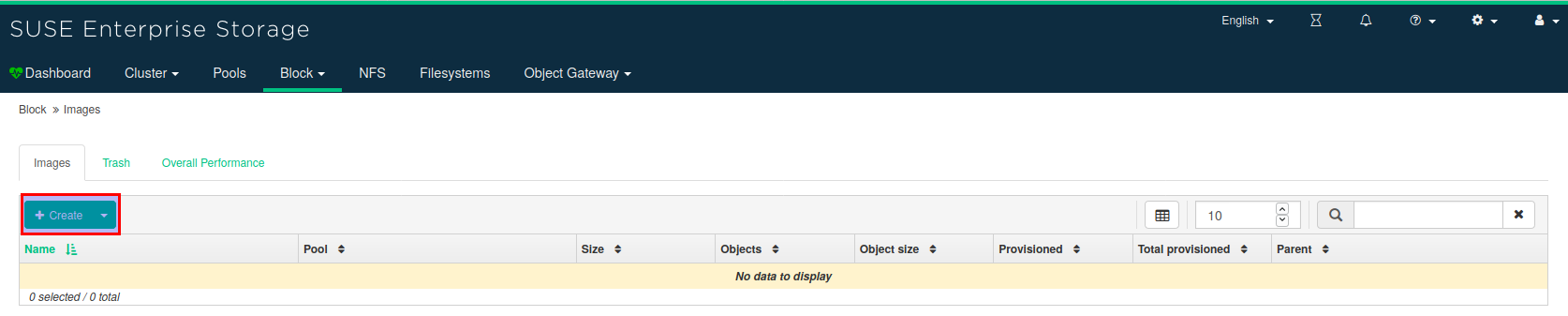
Figure 30: Cluster Dashboard Accessing Pool #An overview of the configured RDBs is displayed.
Click the Create button.
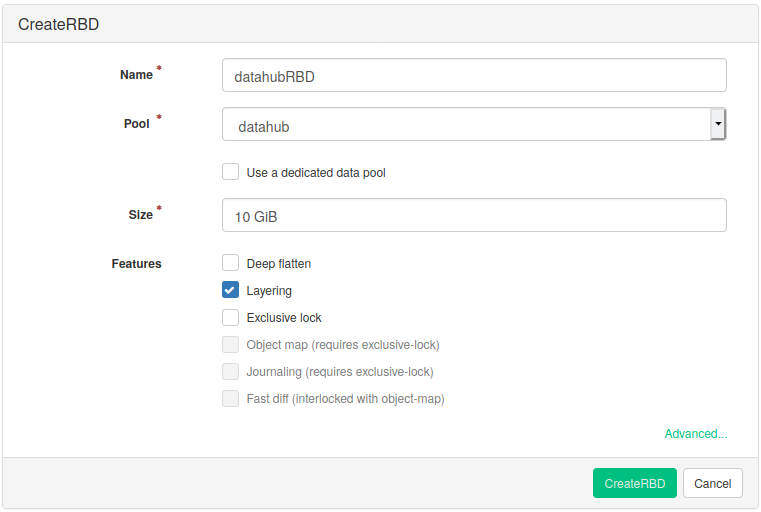
Figure 31: Cluster Dashboard RDB Overview #Enter the name, and if it is not already selected, select the previously created pool. Select the size of the RBD and confirm the creation by clicking the "CreateRBD" button.
Figure 32: Cluster Dashboard Creating New RDB #The overview page of the RBDs is shown again. It now contains your newly created RBD.
Figure 33: Cluster Dashboard RDB Updated Overview #
At this point, the SUSE Enterprise Storage cluster is ready for usage with SAP Data Intelligence.
6 Installing SAP Data Intelligence 3 on top of SUSE CaaSP 4.2 #
6.1 Documentation #
6.2 Planning the installation with the SAP Maintenance Planner #
For the installation of SAP Data Intelligence, you should start here: SAP Maintenance Planner
You need to have your SAP S-User available.
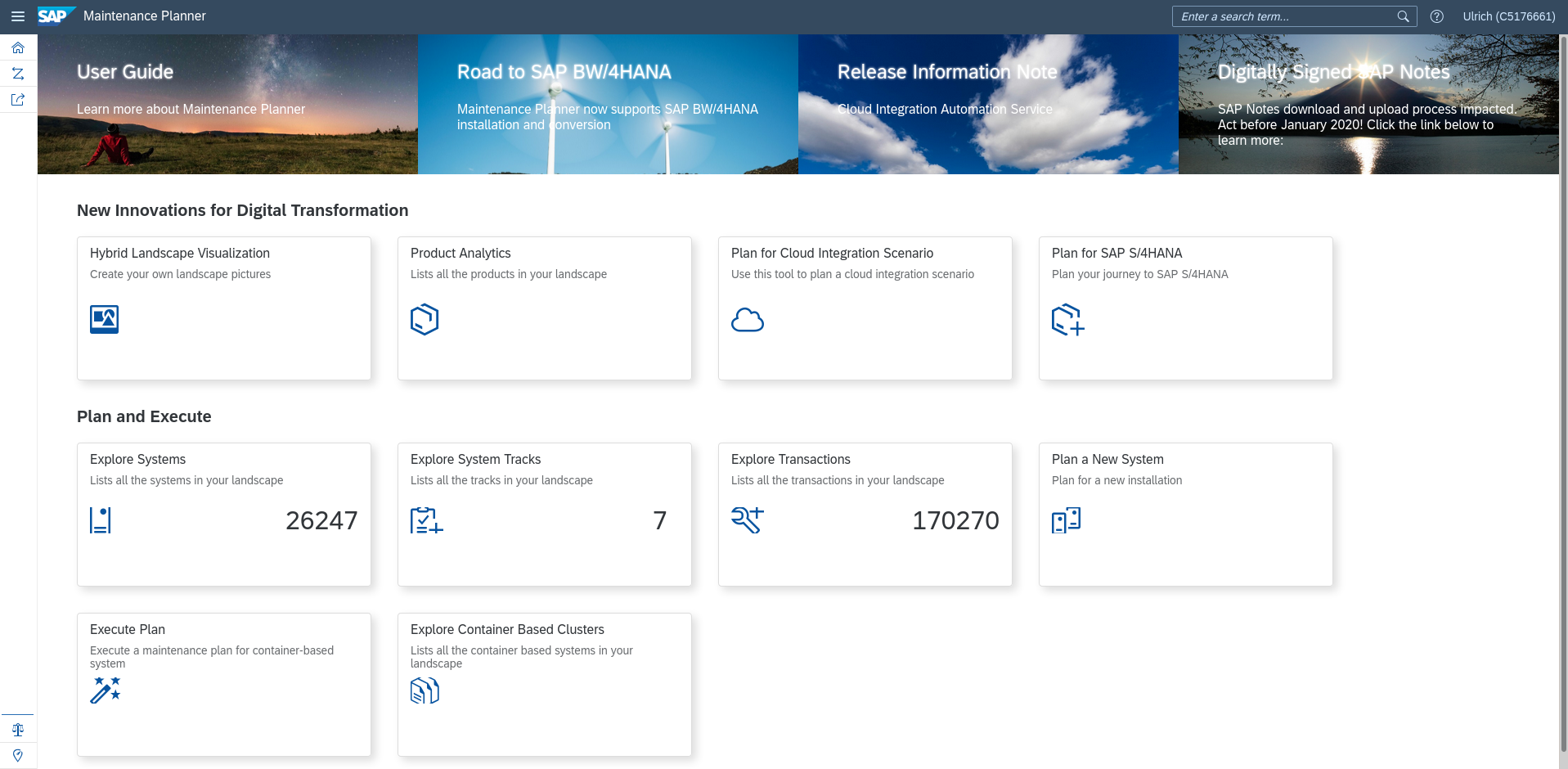
The landing page of the SAP Maintenance Planner looks as follows:
Figure 34: SAP Maintenance Planner Start page #Click "Plan a New System" on the right.
The next page displayed looks as follows:
Figure 35: SAP Maintenance Planner: Select Plan #You will see a circle where all options except the option "Plan" are greyed out. Click the "Plan" option.
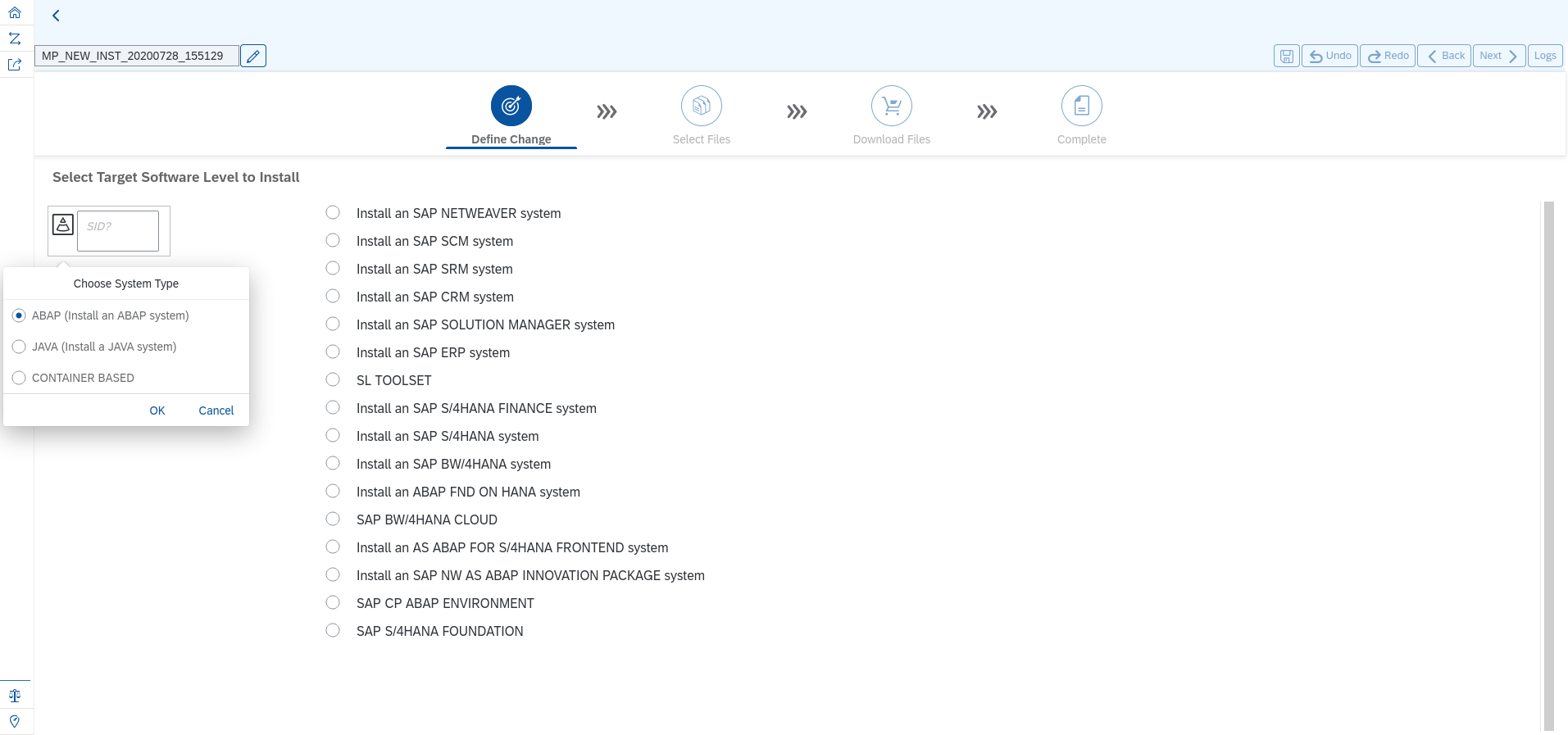
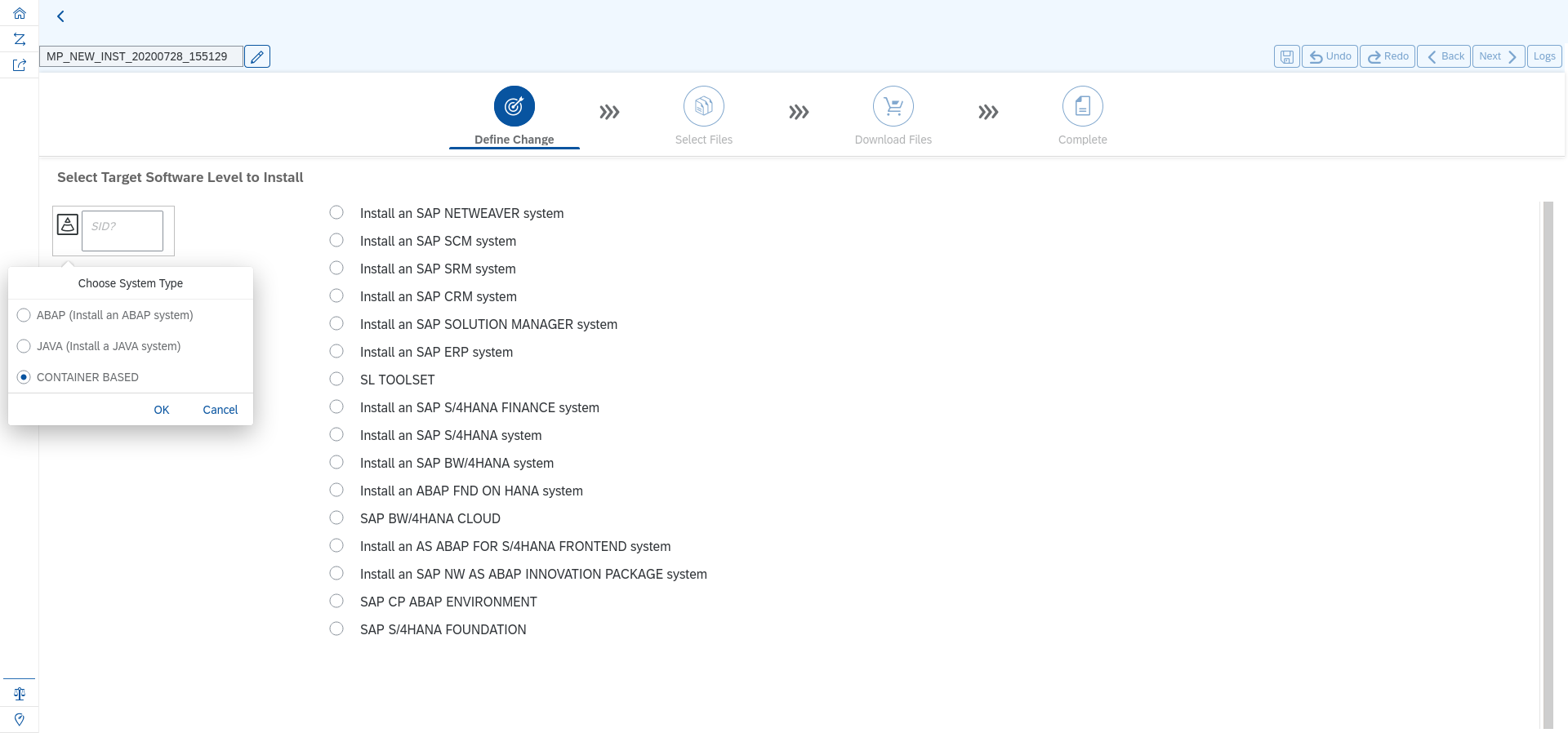
The next page shows the "Define Change" step of your planning:
Figure 36: SAP Maintenance Planner: Select Container Based Product #On the left, there is a window with three toggle buttons. Select "CONTAINER BASED" and click "OK":
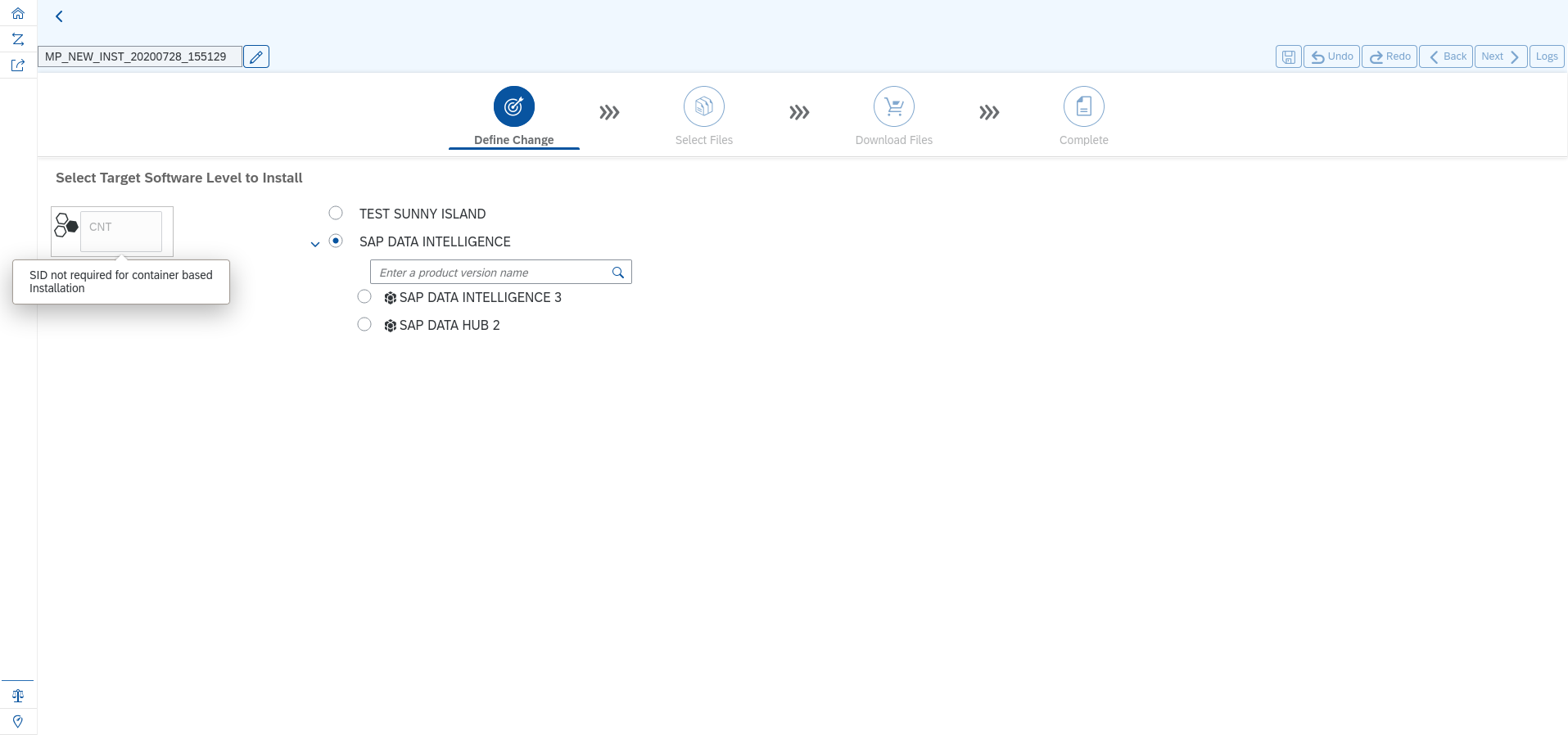
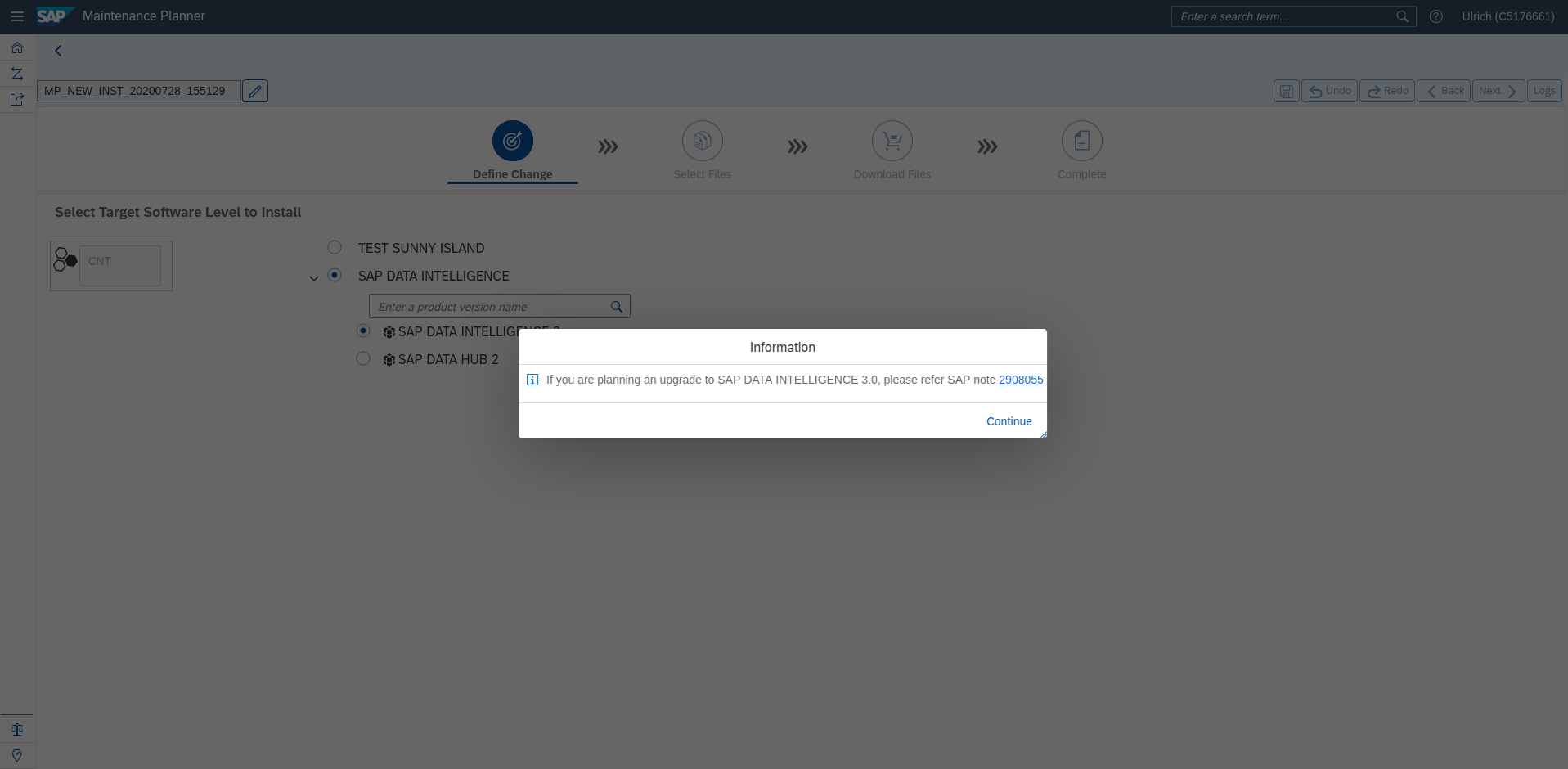
Figure 37: SAP Maintenance Planner: Select Container Based Product #2 #To the right, the option "SAP DATA INTELLIGENCE" should appear. When you select it, a sub-selection should open with choices for "SAP DATA INTELLIGENCE 3" and "SAP DATA HUB 2". Select "SAP DATA INTELLIGENCE 3":
Figure 38: SAP Maintenance Planner: Select Data Intelligence 3 #A pop-up window will appear to inform you about the related SAP note. Click "Continue" to proceed:
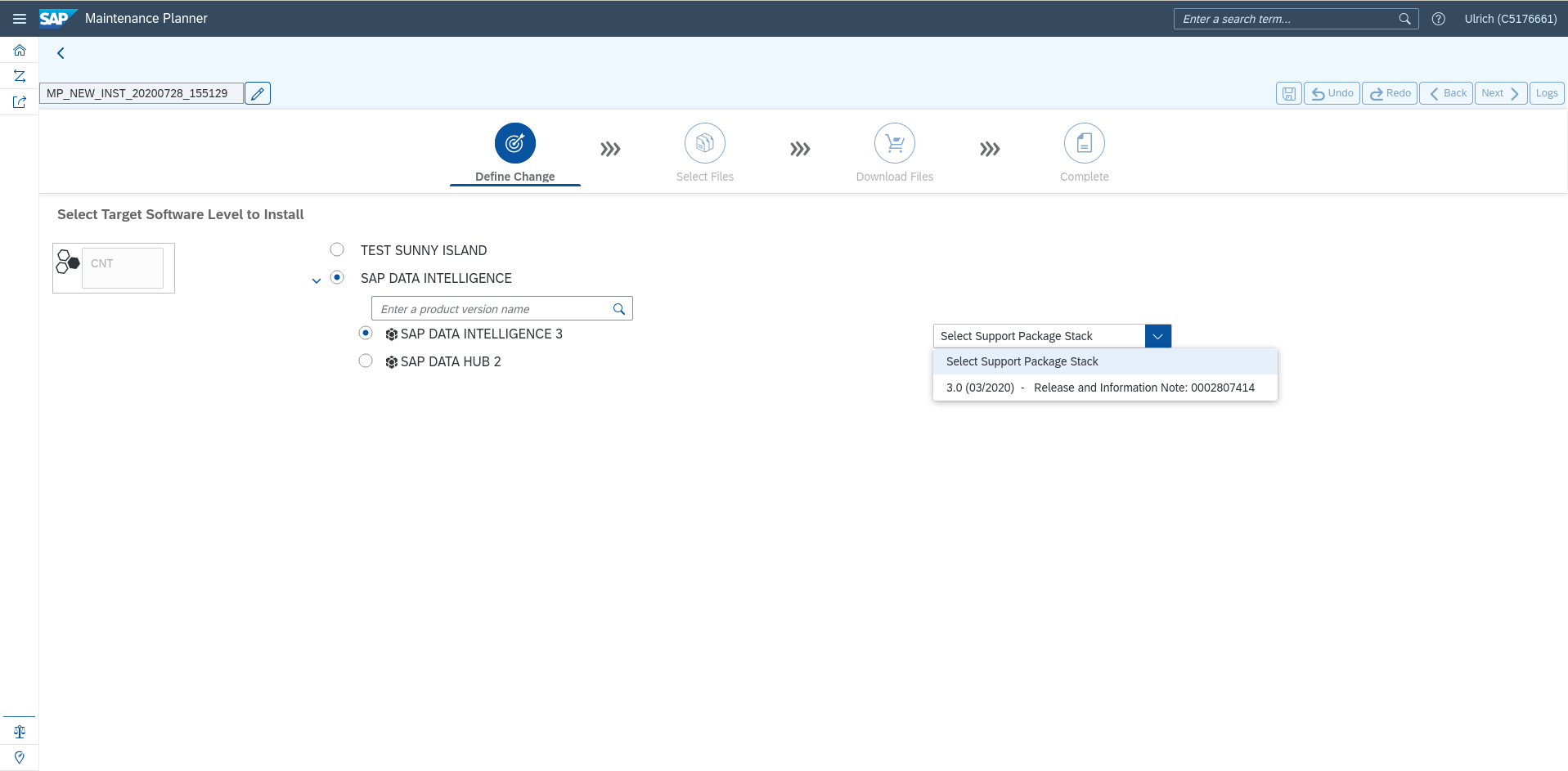
Figure 39: SAP Maintenance Planner: Select Continue #On the right hand side, a drop-down box is shown with "Select Support Package Stack". Click this, and select from the available patch levels as needed:
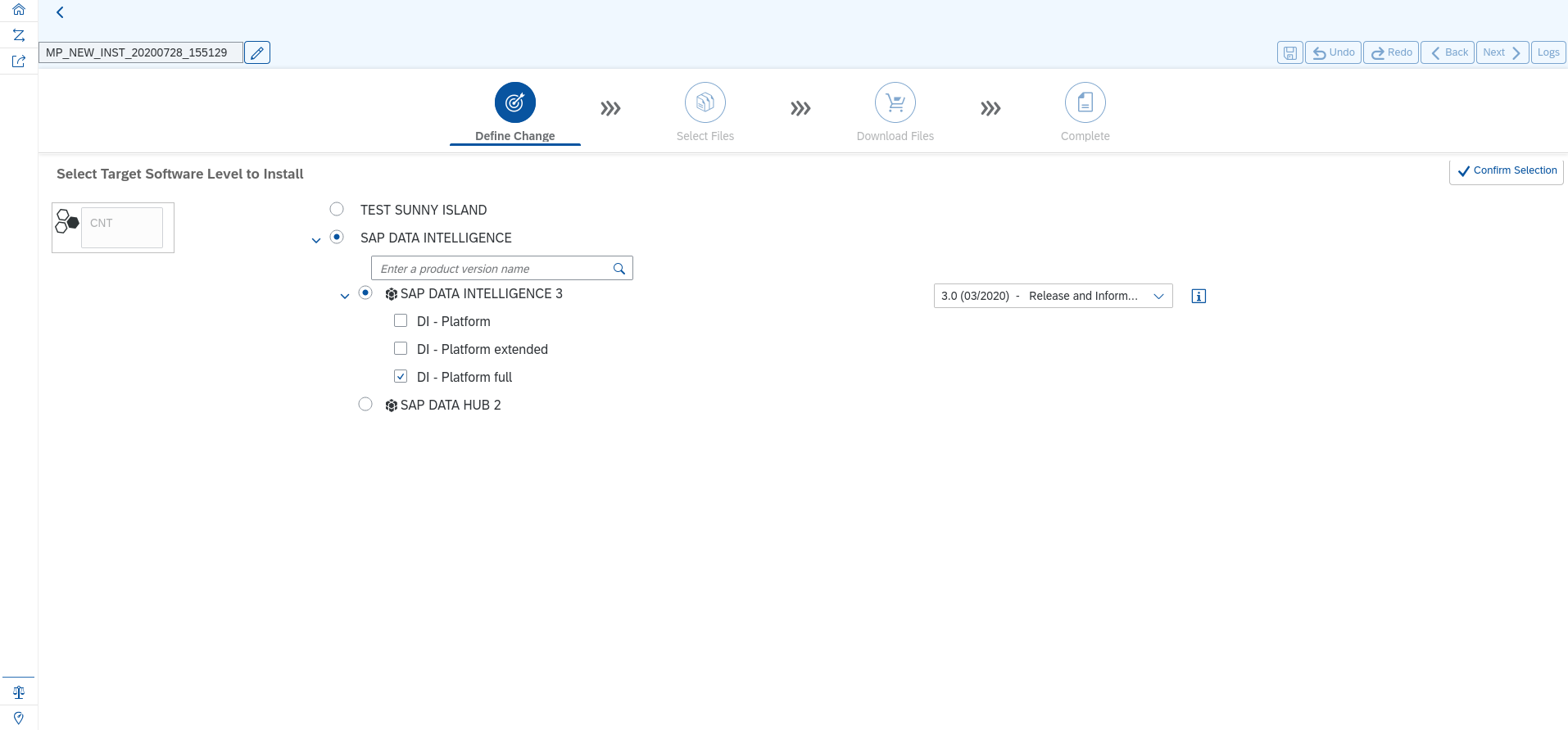
Figure 40: SAP Maintenance Planner: Select from available patch levels as you need. #To the left, the sub-selection for "SAP DATA INTELLIGENCE 3" will need changes. Select what you need and click the "Confirm Selection" at the very right:
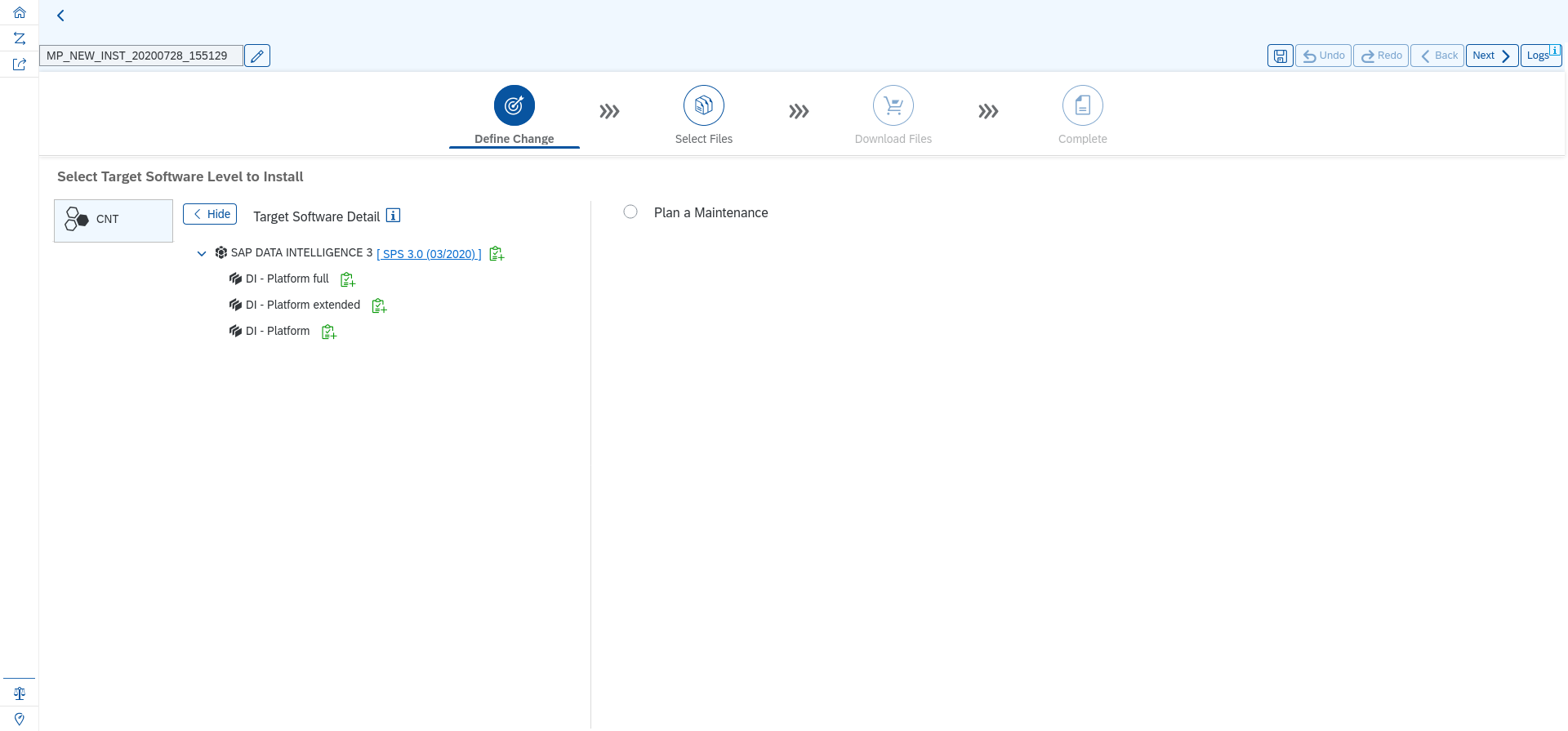
Figure 41: SAP Maintenance Planner: Select according your needs and confirm. #An overview of your selection is shown. If this fits your needs, click the "Next" button at the upper right corner:
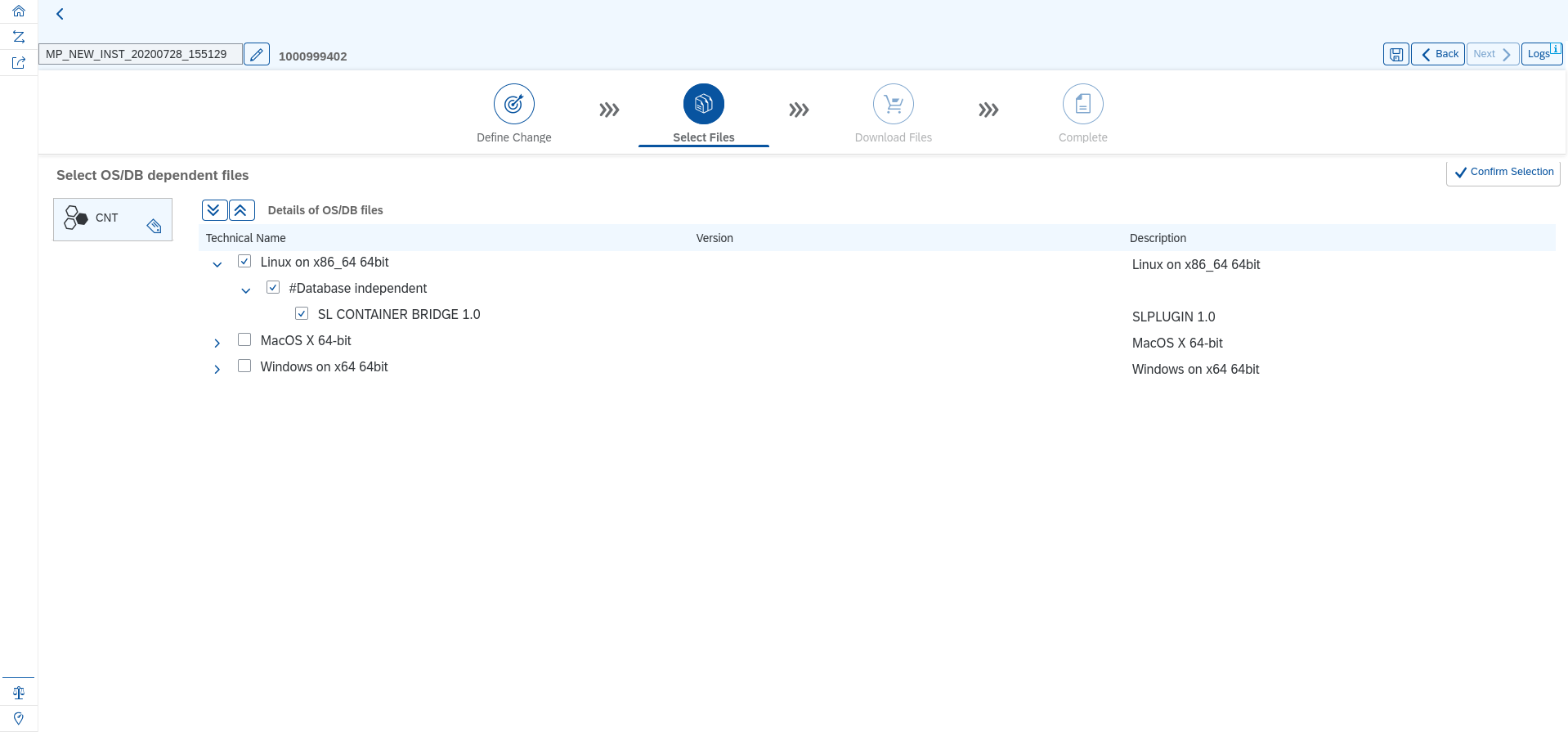
Figure 42: SAP Maintenance Planner: Select next if satisfied #Next, select the operating system upon which SAP Data Intelligence will be installed. Select "Linux on x86_64 64bit" and click "Confirm Selection":
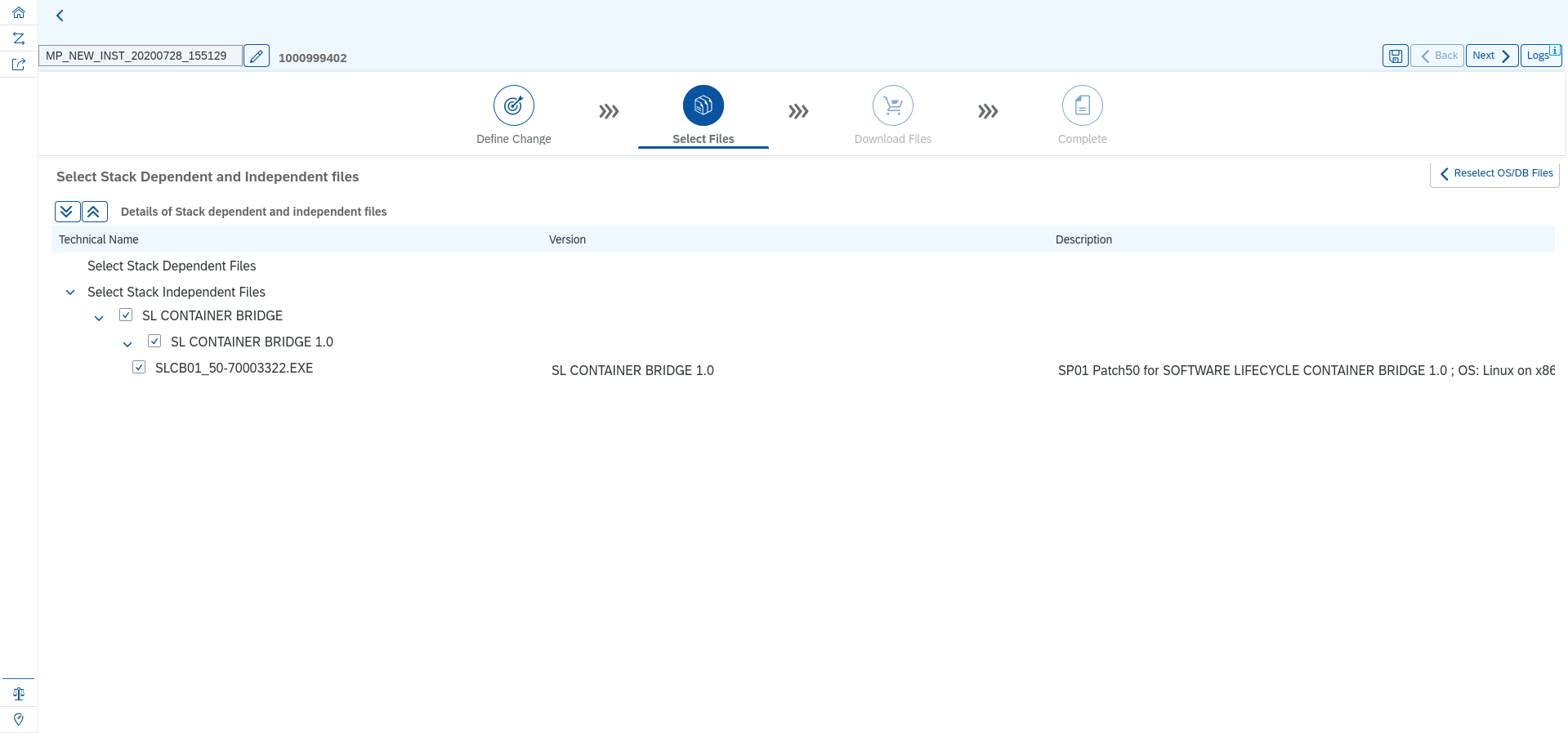
Figure 43: SAP Maintenance Planner: Select Linux and confirm #The next page shows the preselected files to use and download. Again, click the "Next" button on the upper right:
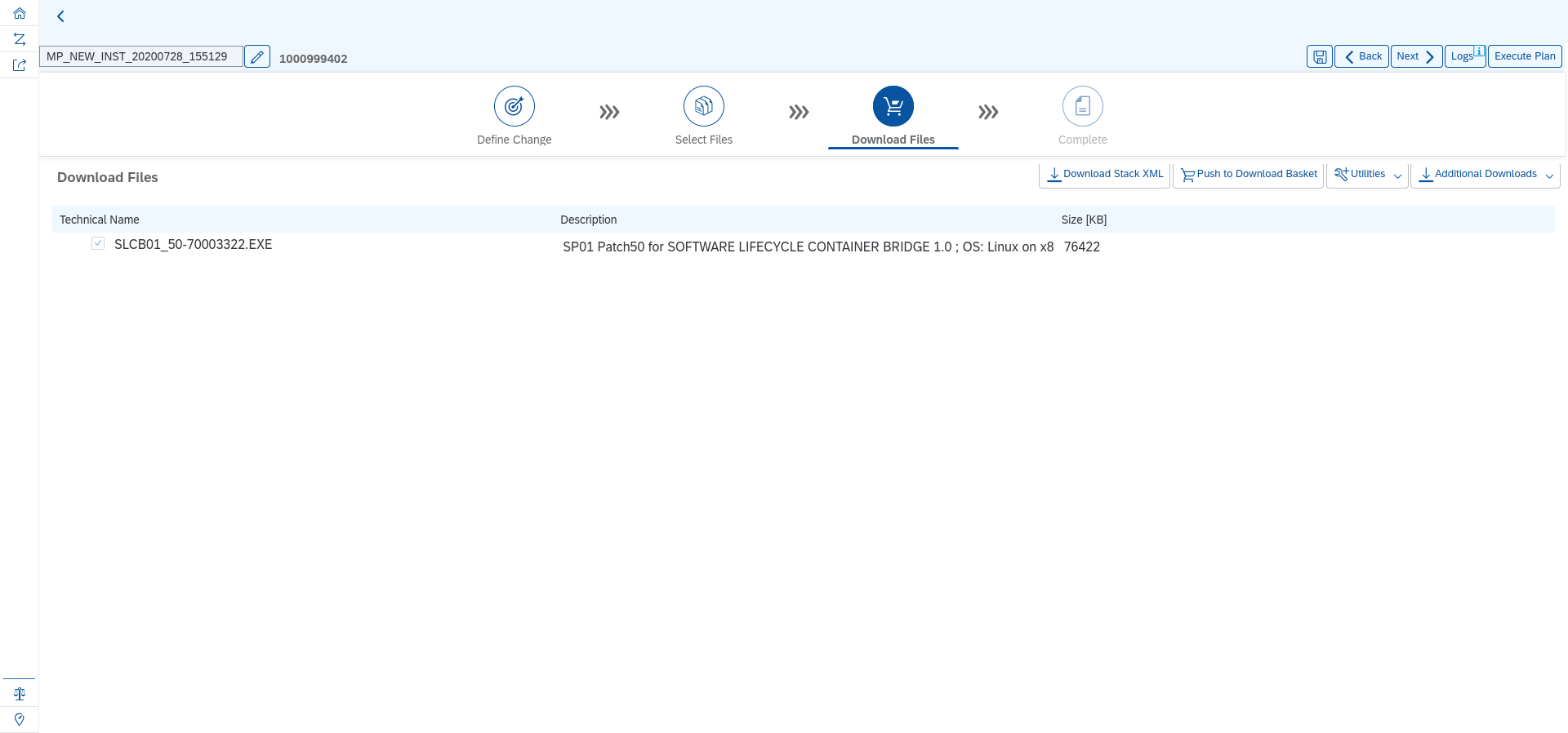
Figure 44: SAP Maintenance Planner: Confirm #You should now arrive at the "Download Files" page. The required SLC bridge is already preselected. Click "Next" to proceed:
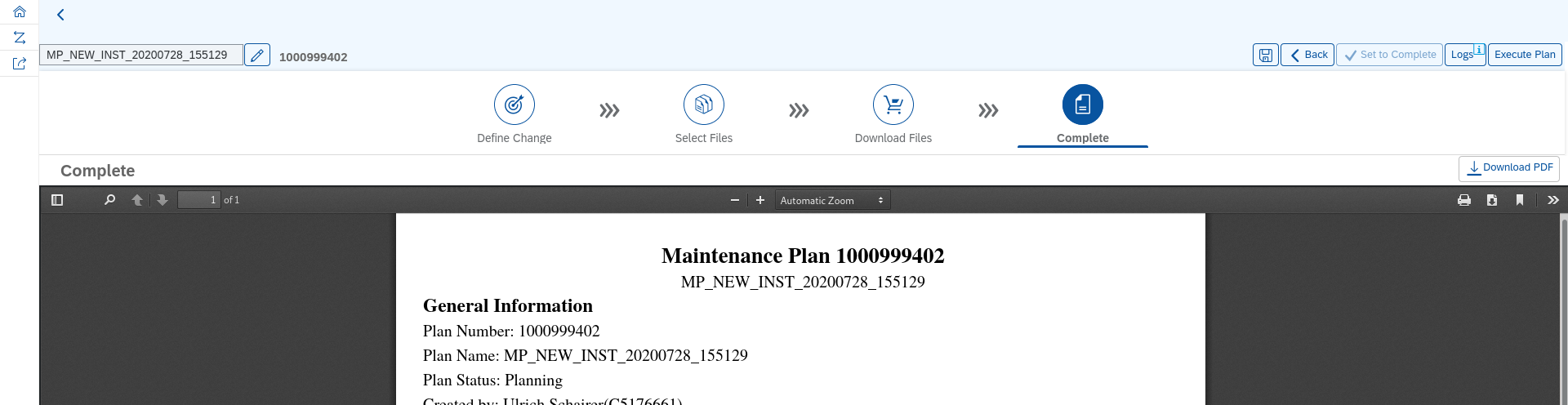
Figure 45: SAP Maintenance Planner: Execute Plan #Your maintenance plan is shown as PDF. Confirm everything by clicking the "Execute Plan" button on the upper right side:
Figure 46: SAP Maintenance Planner: Download Stack.xml and SLC Bridge Installer #Download the SLC Bridge Installer and copy it to your management workstation. You will need this file in Section 6.3, “Installing the SAP SLC Bridge”.
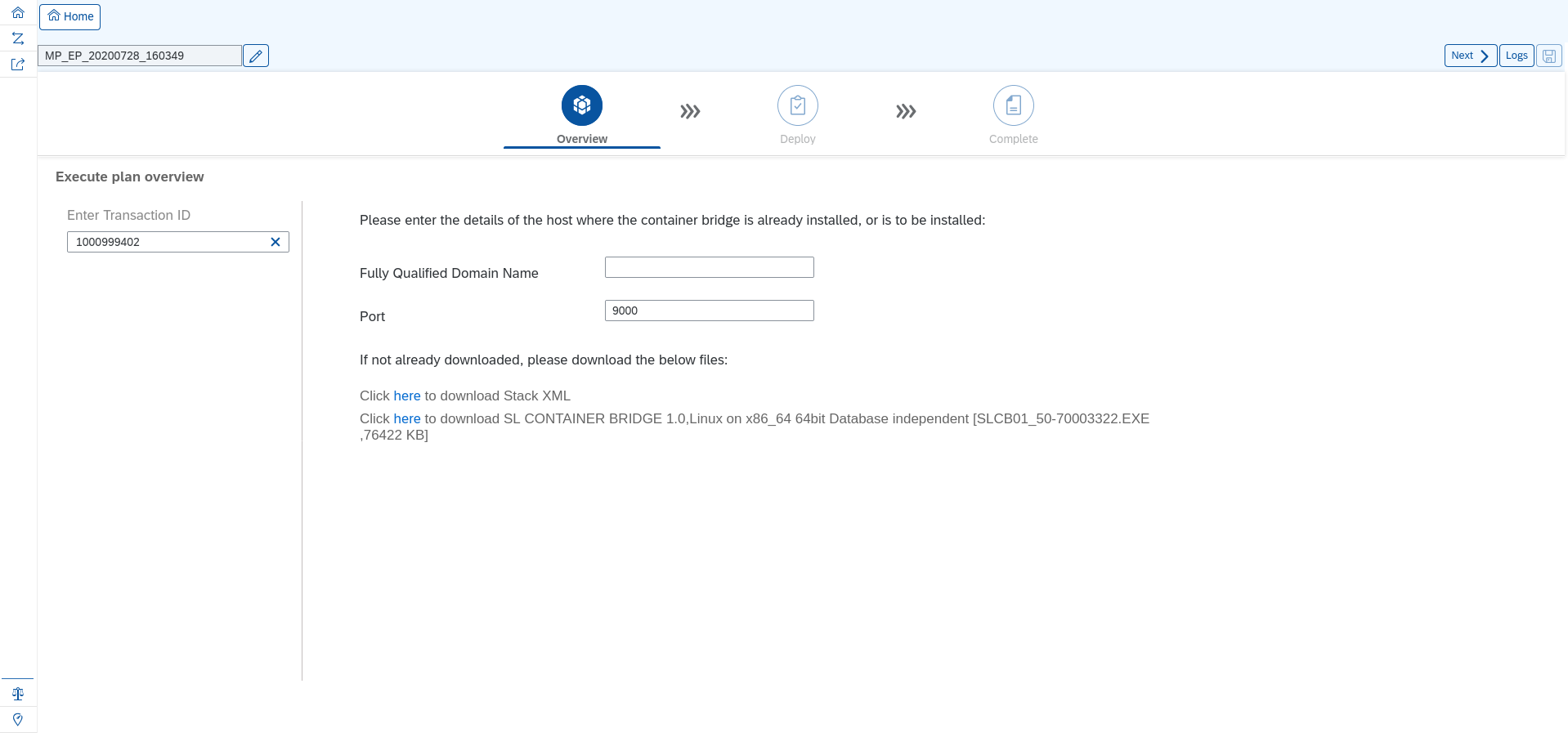
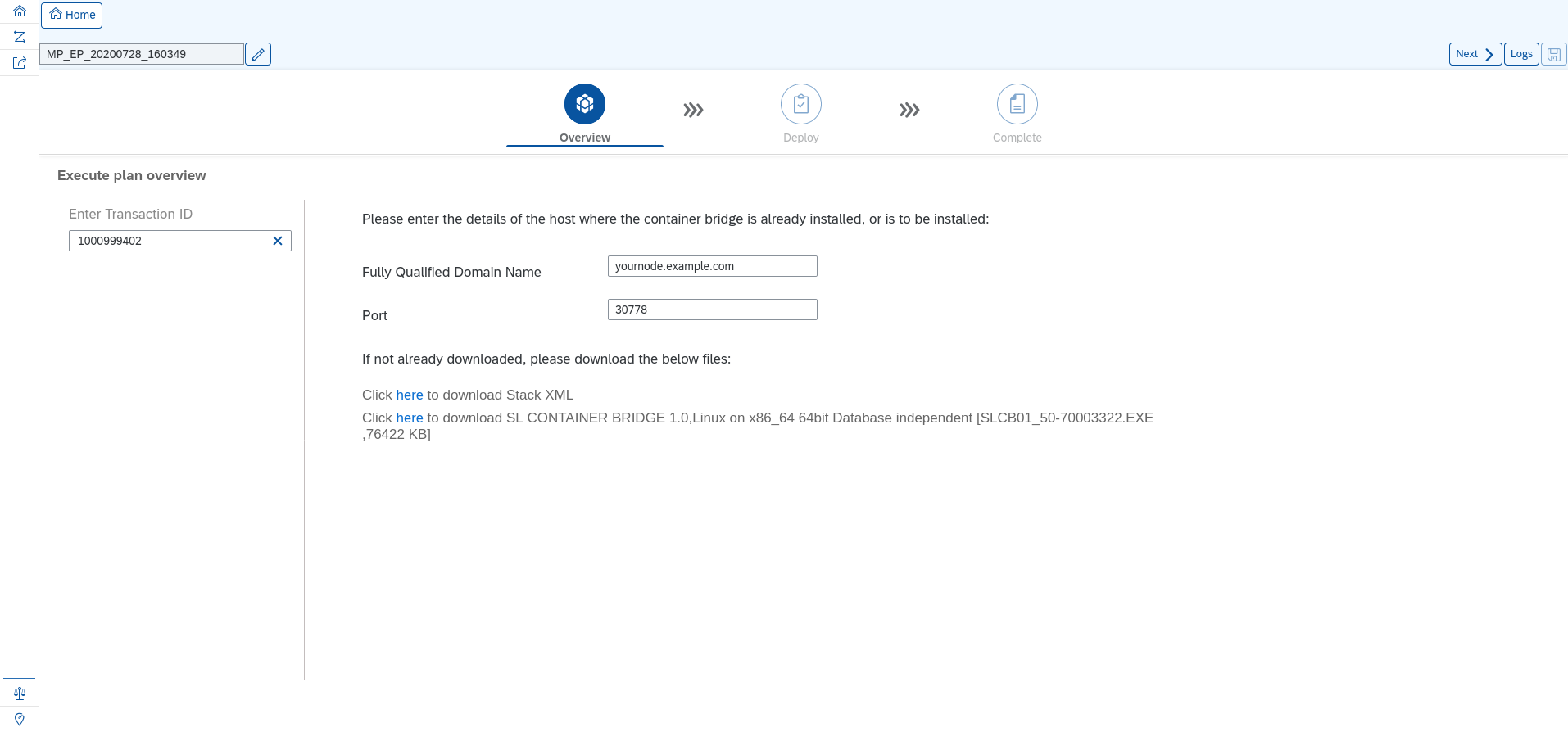
You will be prompted to enter the FQDN and the port of the machine your SLC bridge will run on:
Figure 47: SAP Maintenance Planner: Enter FQDN of host where the SLC Bridge will run #Fill in the values. An example looks as follows:
Figure 48: SAP Maintenance Planner: Example for host and port #
6.3 Installing the SAP SLC Bridge #
Download the file containing the SLC Bridge Installer.
If you have not already done so, copy this file to the management workstation.
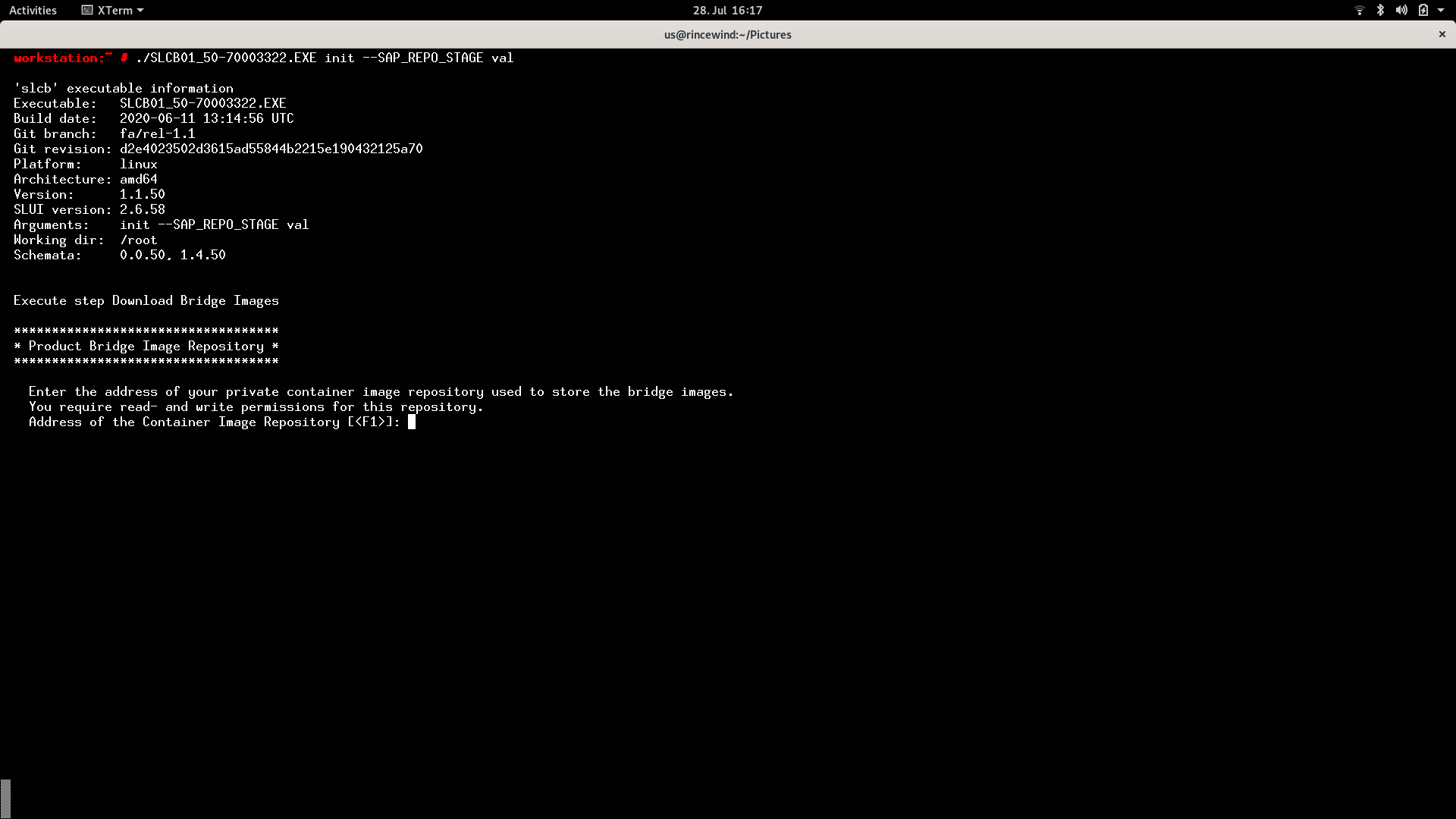
Run the SLC Bridge Installer on the management workstation.
$ ./SLCB01_<YOUR DOWNLOADED VERSION>.EXE init
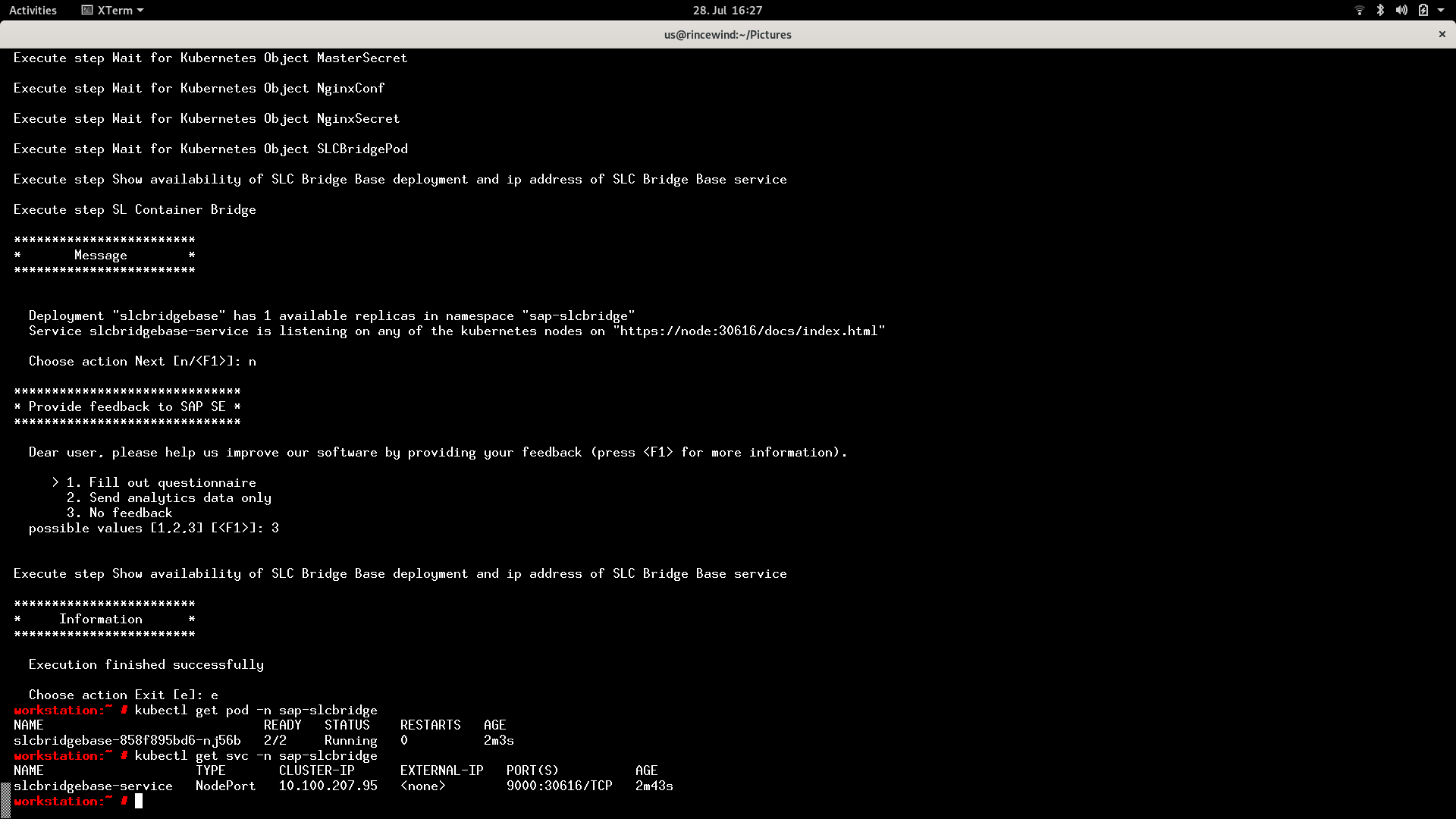
Figure 49: SAP SLC Bridge Installer #This interactive script gathers all the necessary information to run the SAP SLC Bridge, and at the end, deploys it into the CaaSP cluster.
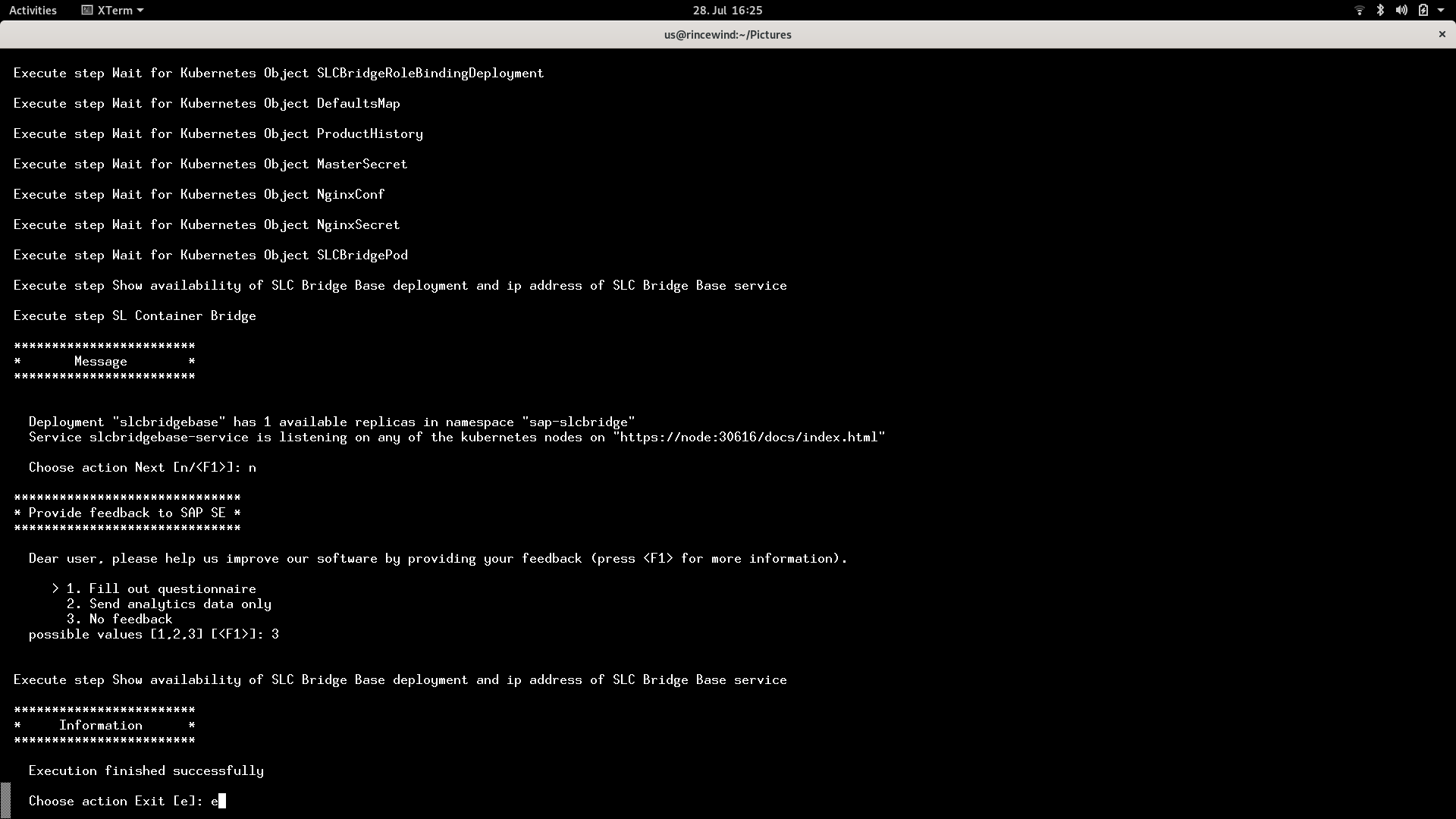
Figure 50: SAP SLC Bridge Information #Identify the service port for the SLC Bridge:
# kubectl -n sap-slcbridge get pods NAME READY STATUS RESTARTS AGE di-platform-full-product-bridge 2/2 Running 0 3d23h slcbridgebase-858f895bd6-74gps 2/2 Running 1 10d # kubectl -n sap-slcbridge get svc NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE di-platform-full-product-bridge-service ClusterIP 10.101.2.224 <none> 9000/TCP 3d23h slcbridgebase-service NodePort 10.97.79.26 <none> 9000:30778/TCP 10d
In our example, the port number on which the SLC Bridge listens is
30778.Make a note of this information. It is needed for the installation process via SAP Maintenance Planner.
Figure 51: SAP SLC Bridge #
6.4 Installing SAP Data Intelligence 3 #
This section describes the installation of SAP Data Intelligence 3 on top of SUSE CaaSP 4.2.
6.4.1 Preparations #
Before the installation of SAP DI 3 can start, some preparation work must be done:
Create a namespace on the Kubernetes cluster.
Define a (default) storage class on the Kubernetes cluster.
Adapt
PodSecurityPolicies.Create the necessary
ClusterRoleBindings.If you use self-signed certificates for the private registry, a special secret must be created.
Unless otherwise specified, all these tasks are run from the management workstation.
6.4.1.1 Creating namespace for SAP Data Intelligence 3 on Kubernetes #
Define the namespace into which SAP Data Intelligence 3 will be installed:
$ kubectl create namespace <YOUR NAMESPACE>
6.4.1.2 Creating Storage Class #
Create the storage class to provide volumes for SAP Data Intelligence 3 on SUSE Enterprise Storage.
Make sure that you have:
the connection data for your SUSE Enterprise Storage at hand
the IP addresses and port number (default: 6789) of the monitor nodes of your SES cluster
created a data pool on your SES cluster for use with SAP Data Intelligence 3
the name of this pool (
datahubin this example) available
Edit the example below to fit your environment.
$ cat > storageClass.yaml <<EOF apiVersion: storage.kubernetes.io/v1 kind: StorageClass metadata: annotations: storageclass.kubernetes.io/is-default-class: "true" name: datahub namespace: default parameters: adminId: admin adminSecretName: ceph-admin-secret adminSecretNamespace: default imageFeatures: layering imageFormat: "2" monitors: <IP ADDRESS OF MONITOR 1>:6789, <IP ADDRESS OF MONITOR 2>:6789, <IP ADDRESS OF MONITOR 3 >:6789 pool: datahub userId: admin userSecretName: ceph-user-secret provisioner: kubernetes.io/rbd reclaimPolicy: Delete volumeBindingMode: Immediate EOF $ kubectl create -f storageClass.yamlCreate secrets for the StorageClass.
Create the secrets needed to access the storage.
Obtain the keys from your SES cluster. These are located in
ceph.admin.keyringandceph.user.keyring.You must encode the keys with
base64.$ echo <YOUR KEY HERE> | base64
$ cat > ceph-admin-secret.yaml <<EOF apiVersion: v1 kind: Secret metadata: name: ceph-admin-secret type: "kubernetes.io/rbd" data: key: <YOUR BASE64 ENCODED KEY HERE> EOF$ cat > ceph-user-secret.yaml <<EOF apiVersion: v1 kind: Secret metadata: name: ceph-user-secret type: "kubernetes.io/rbd" data: key: <YOUR BASE64 ENCODED KEY HERE> EOF $ kubectl apply -f ceph-admin-secret.yaml $ kubectl apply -f ceph-user-secret.yamlCreate the credentials for accessing the StorageClass from the namespace where DI 3 will be installed into.
$ kubectl -n <YOUR NAMESPACE FOR DI 3> create -f ceph-admin-secret.yaml $ kubectl -n <YOUR NAMESPACE FOR DI 3> create -f ceph-user-secret.yaml
6.4.1.3 Creating PodSecurityPolicies and ClusterRoleBindings #
PodSecurityPolicies
$ kubectl edit psp suse.caasp.psp.privileged
Change the
pathPrefixinallowedHostPathsto/ClusterRoleBindings
$ cat > clusterrolebinding.yaml << EOF apiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRoleBinding metadata: name: suse:caasp:psp:privileged:default roleRef: apiGroup: rbac.authorization.k8s.io kind: ClusterRole name: suse:caasp:psp:privileged subjects: - kind: ServiceAccount name: default namespace: XXX - kind: ServiceAccount name: vora-vsystem-XXX namespace: XXX - kind: ServiceAccount name: vora-vsystem-XXX-vrep namespace: XXX - kind: ServiceAccount name: XXX-elasticsearch namespace: XXX - kind: ServiceAccount name: XXX-fluentd namespace: XXX - kind: ServiceAccount name: XXX-nodeexporter namespace: XXX - kind: ServiceAccount name: vora-vflow-server namespace: XXX - kind: ServiceAccount name: mlf-deployment-api namespace: XXX EOF $ sed -i s/XXX/<your-di-namespace>/g clusterrolebinding.yaml $ kubectl apply -f clusterrolebinding.yaml
Additional changes
$ kubectl edit clusterrolebinding system:node
Insert the following at the end of the file:
subjects: - apiGroup: rbac.authorization.k8s.io kind: Group name: system:nodes
If you use self-signed SSL certificates for the secure private registry, create a secret for accessing this registry.
NoteThe certificate chain should be saved in
pemformat into a single file calledcert.export NAMESPACE=<your namespace> mv cert cert_with_carriage_return tr -d '\r' < cert_with_carriage_return > cert kubectl create secret generic cmcertificates --from-file=cert -n $NAMESPACE
6.4.2 Installing SAP Data Intelligence 3 #
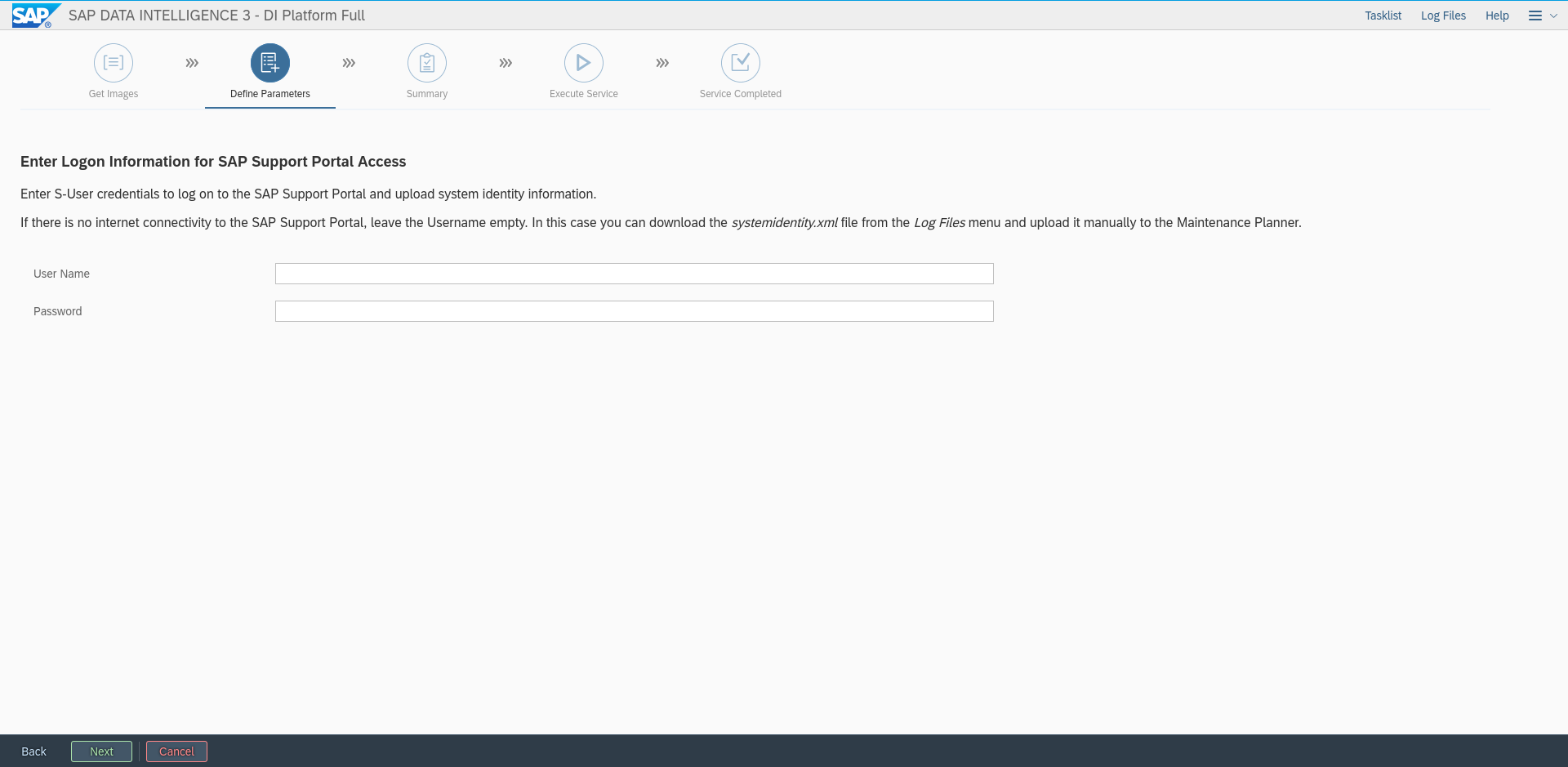
After you successfully finished the preparation stages, proceed with the installation of SAP Data Intelligence 3. To do so, several steps must be executed.
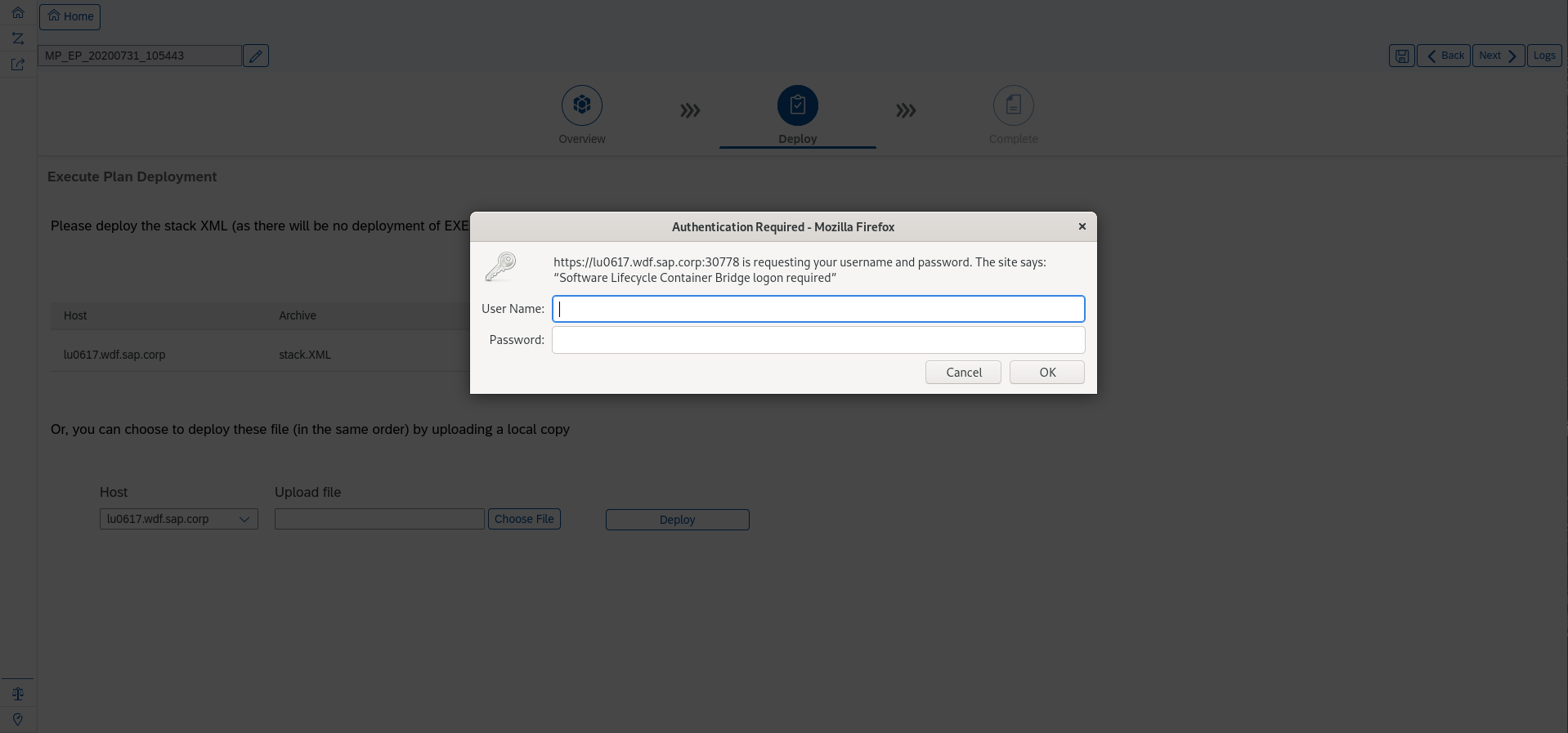
6.4.2.1 Connecting to the SLC Bridge #
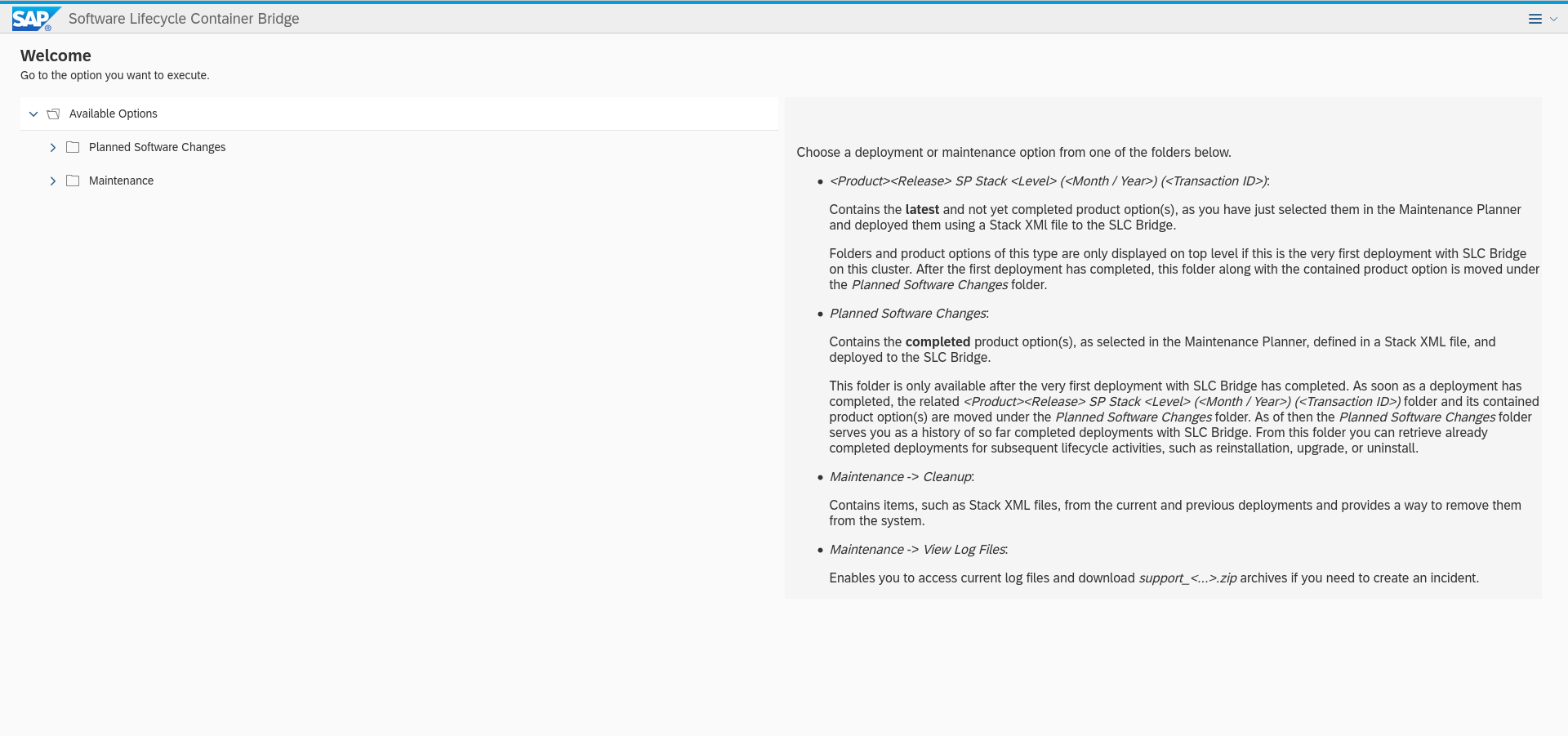
Point your browser to the SLC Bridge service:
https://<yournode>:<yourport>/docs/index.html
Fill in your credentials you created during the deployment of the SLC Bridge.
6.4.2.2 Installing the workflow #
Connect and authenticate to the SLC Bridge service created above. Use the credentials created during the setup of the SLC Bridge:
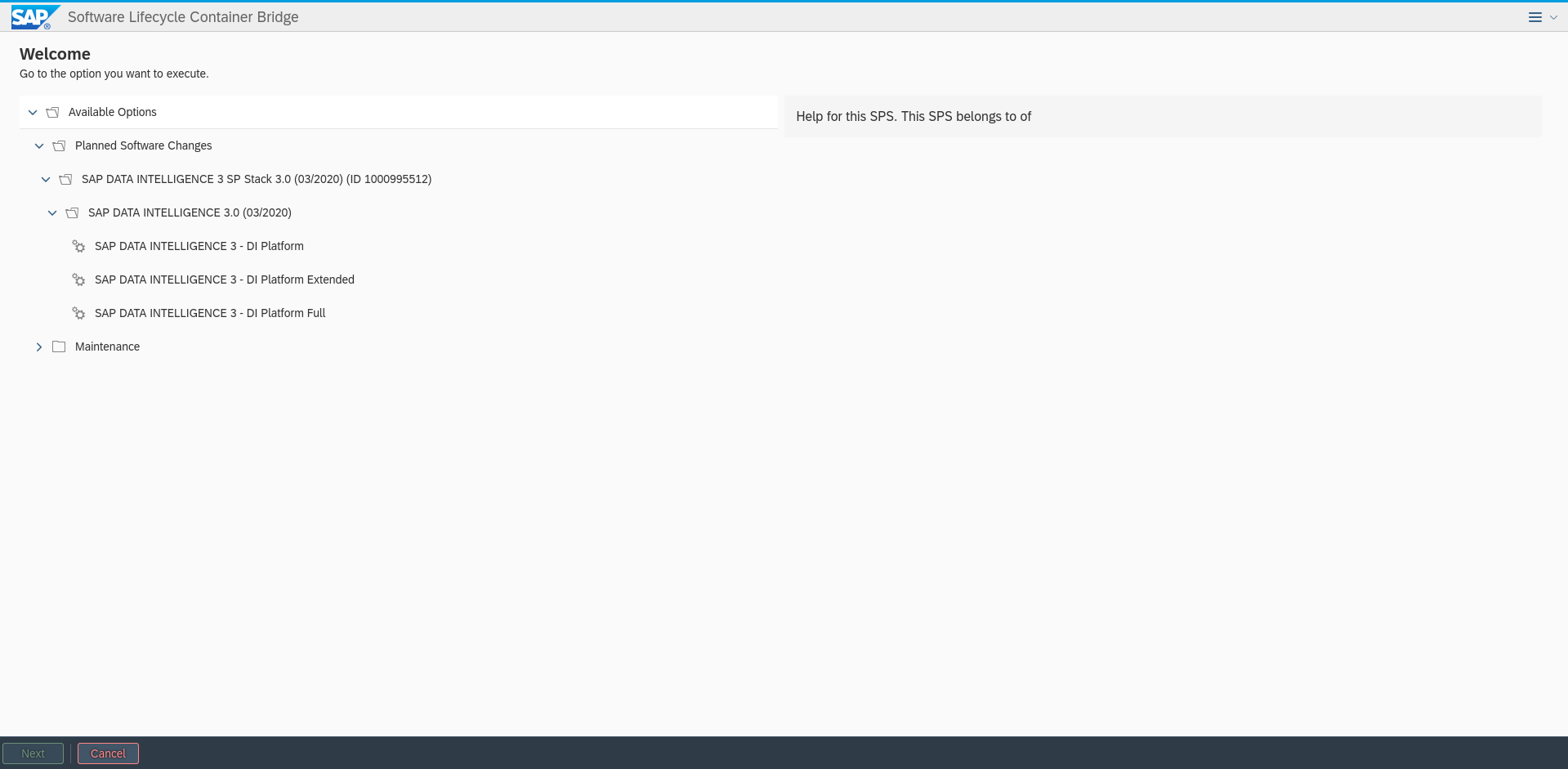
Figure 52: Connect and authenticate to the SLCB Service #Select "Planned software Changes":
Figure 53: Installing planned software changes #Select the SAP Data Intelligence deployment required by your needs. Click "Next":
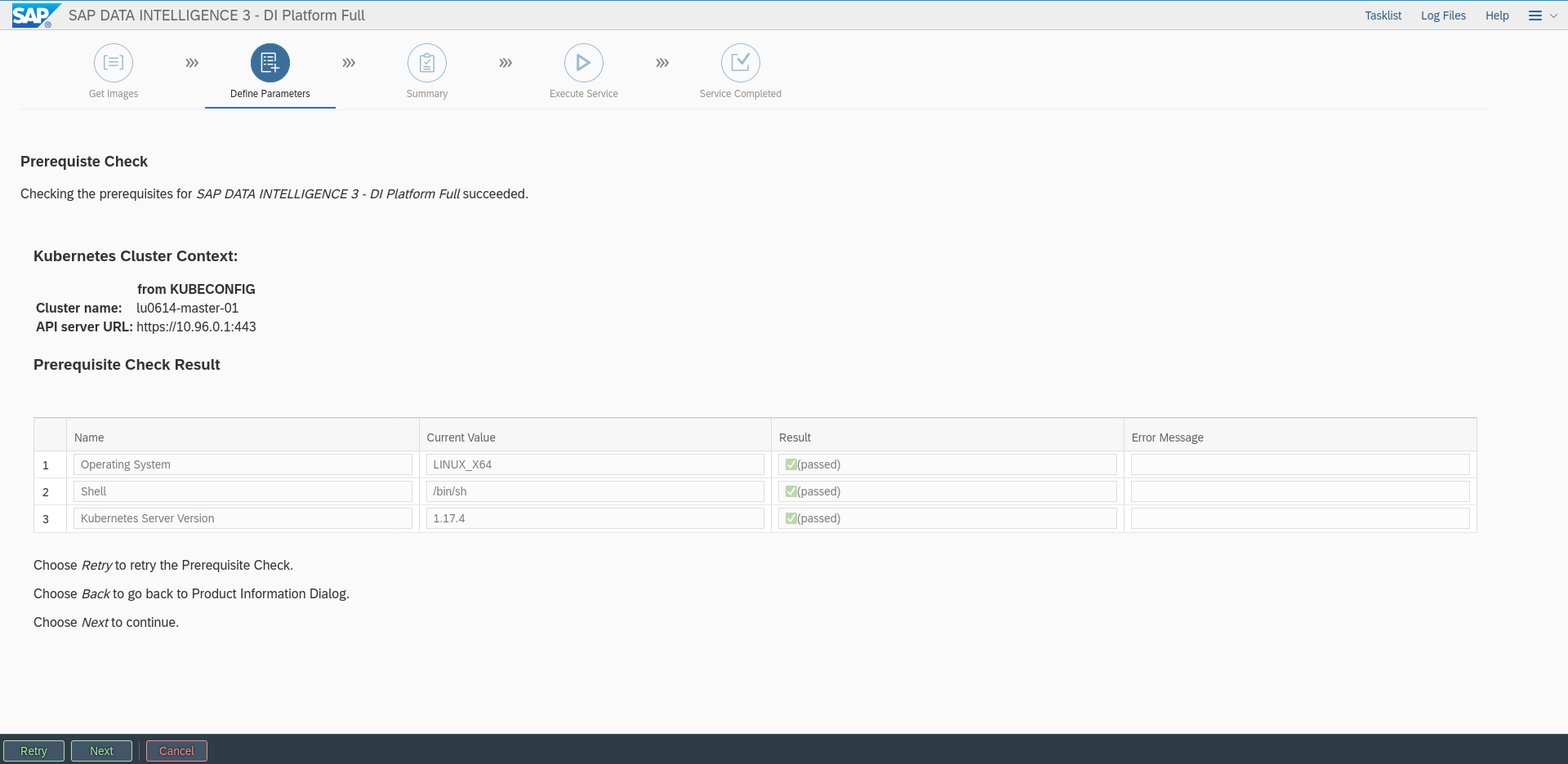
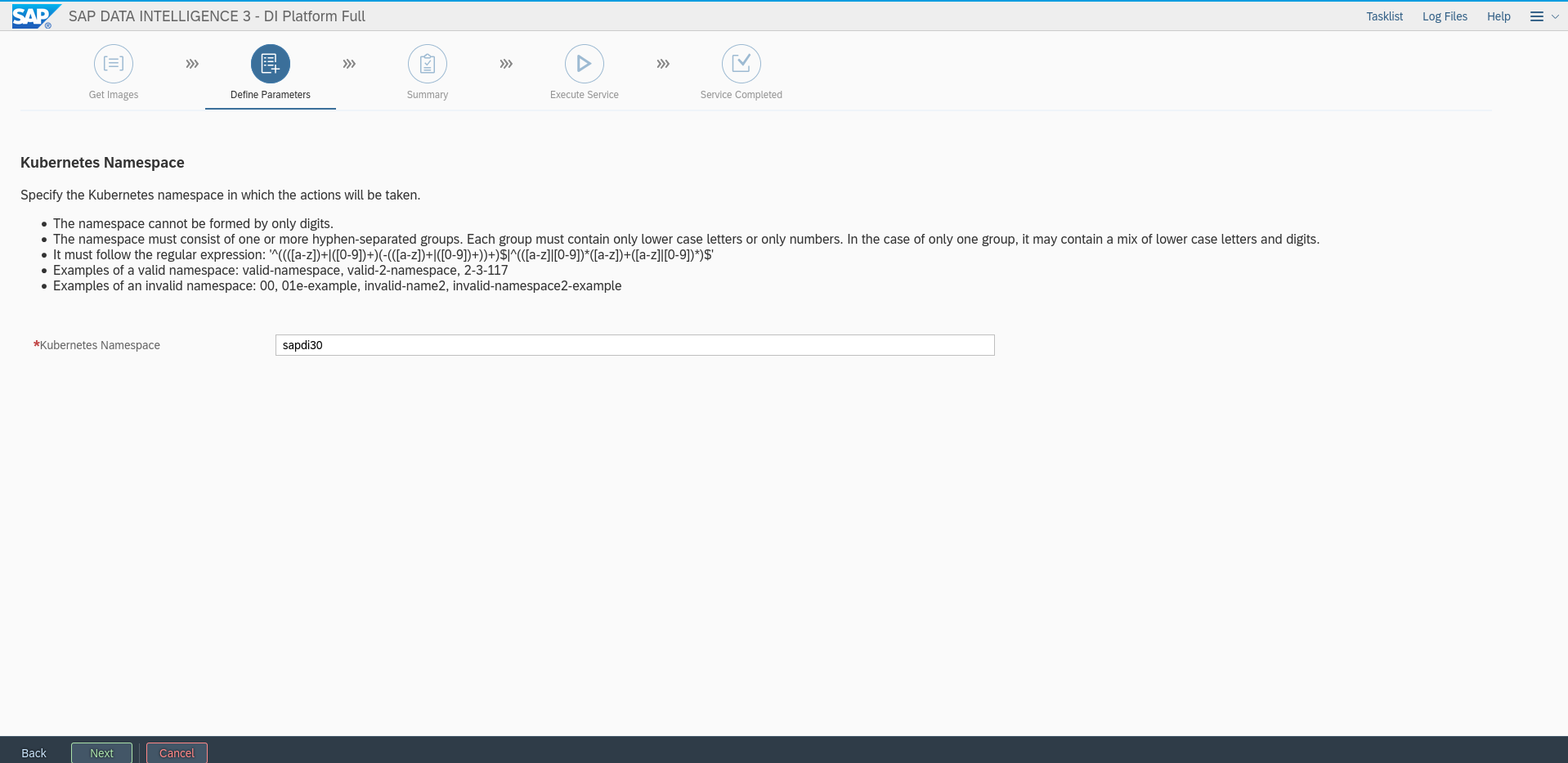
Figure 54: Installing the required SAP DI deployment #Enter the Kubernetes namespace created beforehand, for example
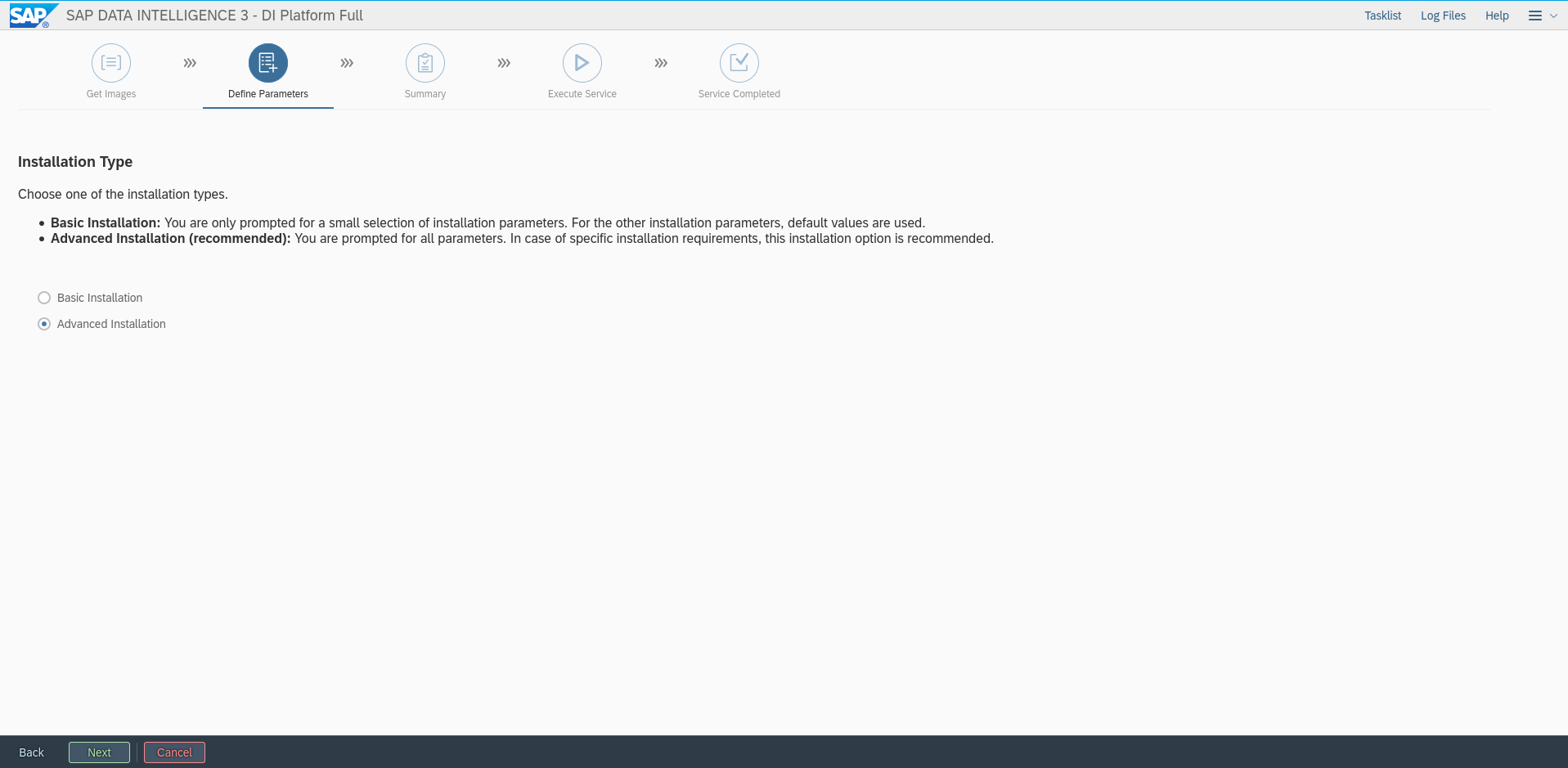
di310. Click "Next":Figure 55: Installing Pre-requisites Check #Figure 56: Installation Enter kubernetes namespace #Select "Advanced Installation":
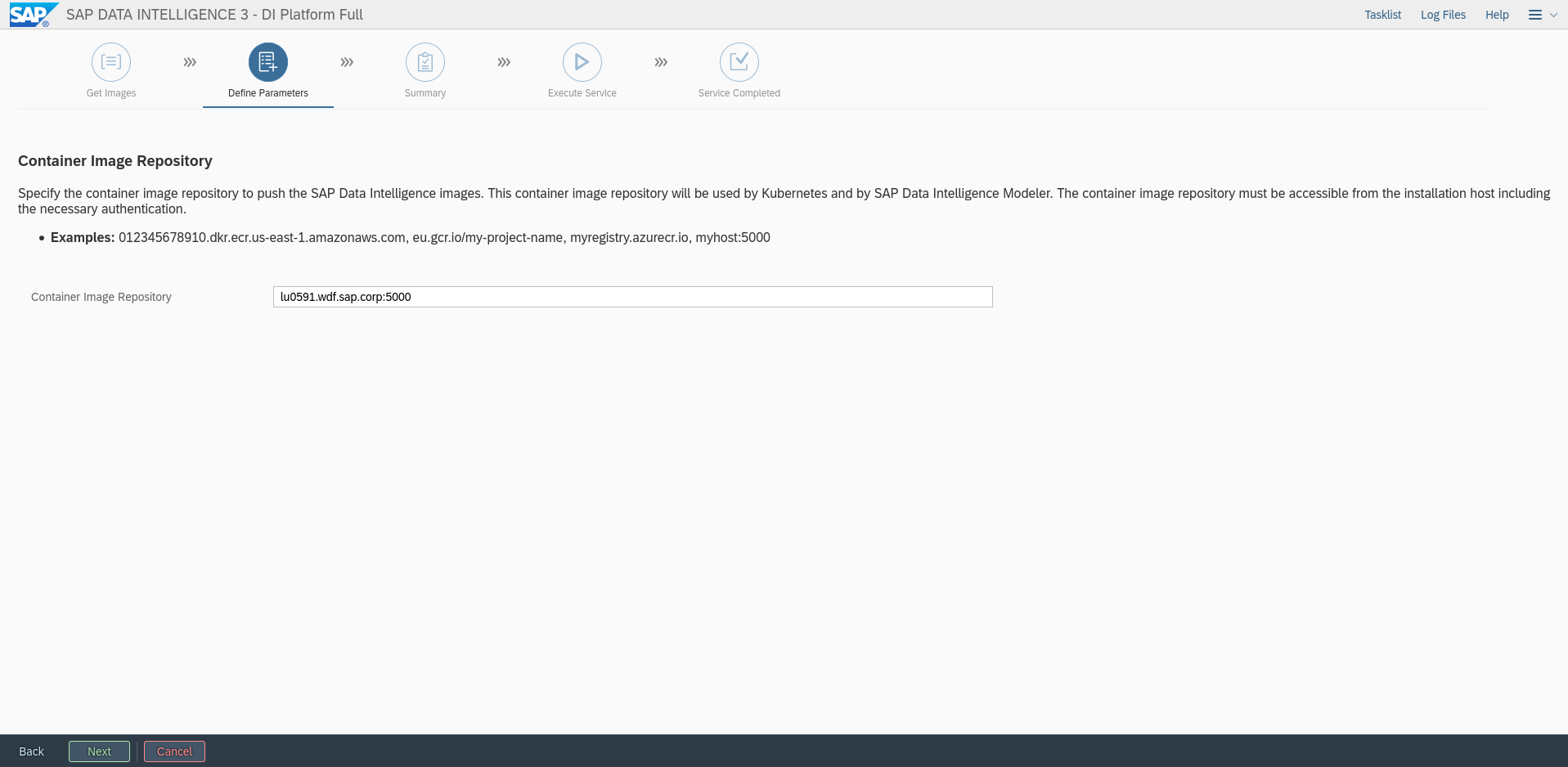
Figure 57: Installing advanced installation #Enter the URI of your Private secure registry. Click "Next":
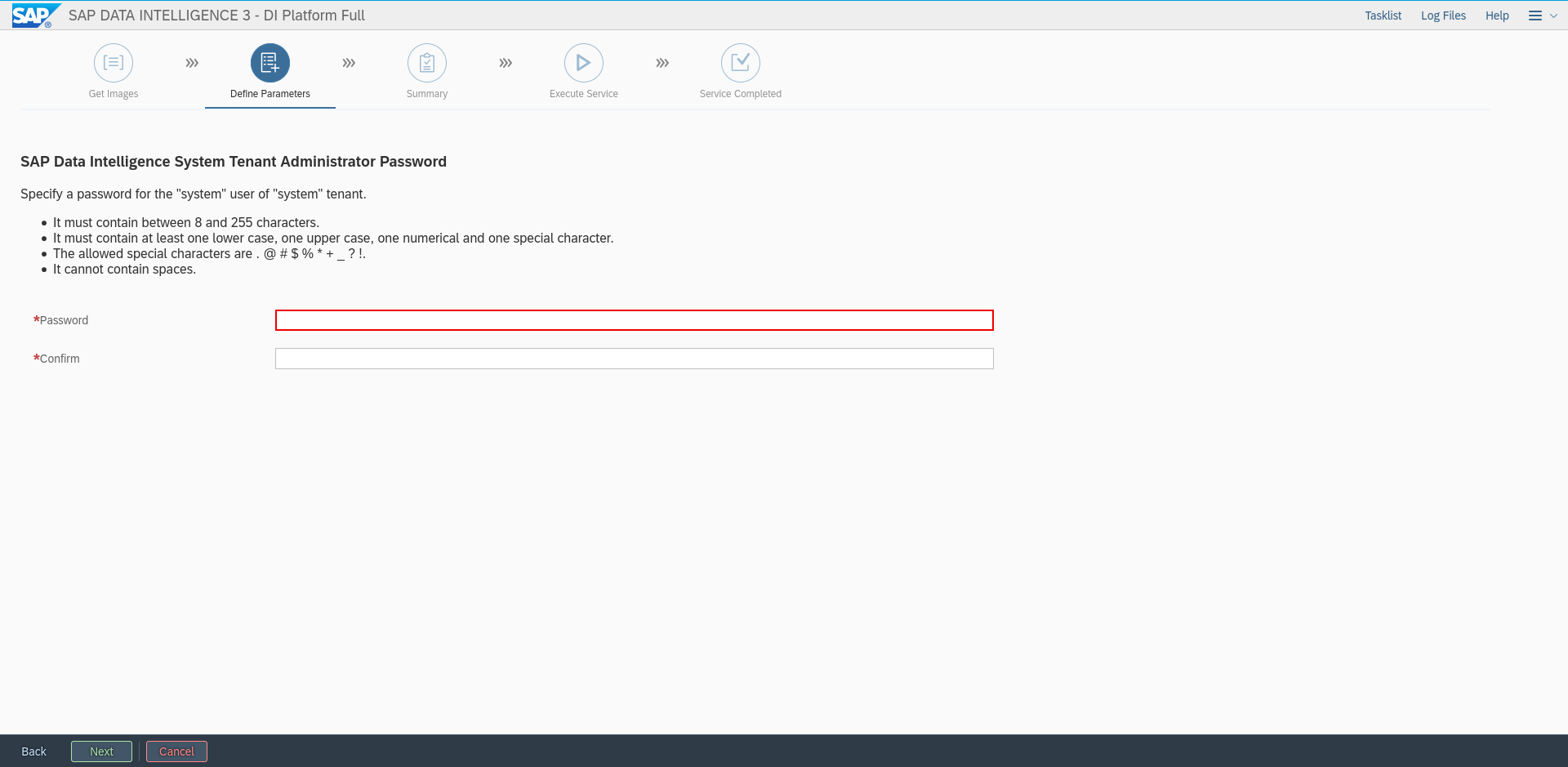
Figure 58: Installing Private Container registry #Enter a password for the system tenant in SAP DI 3.0:
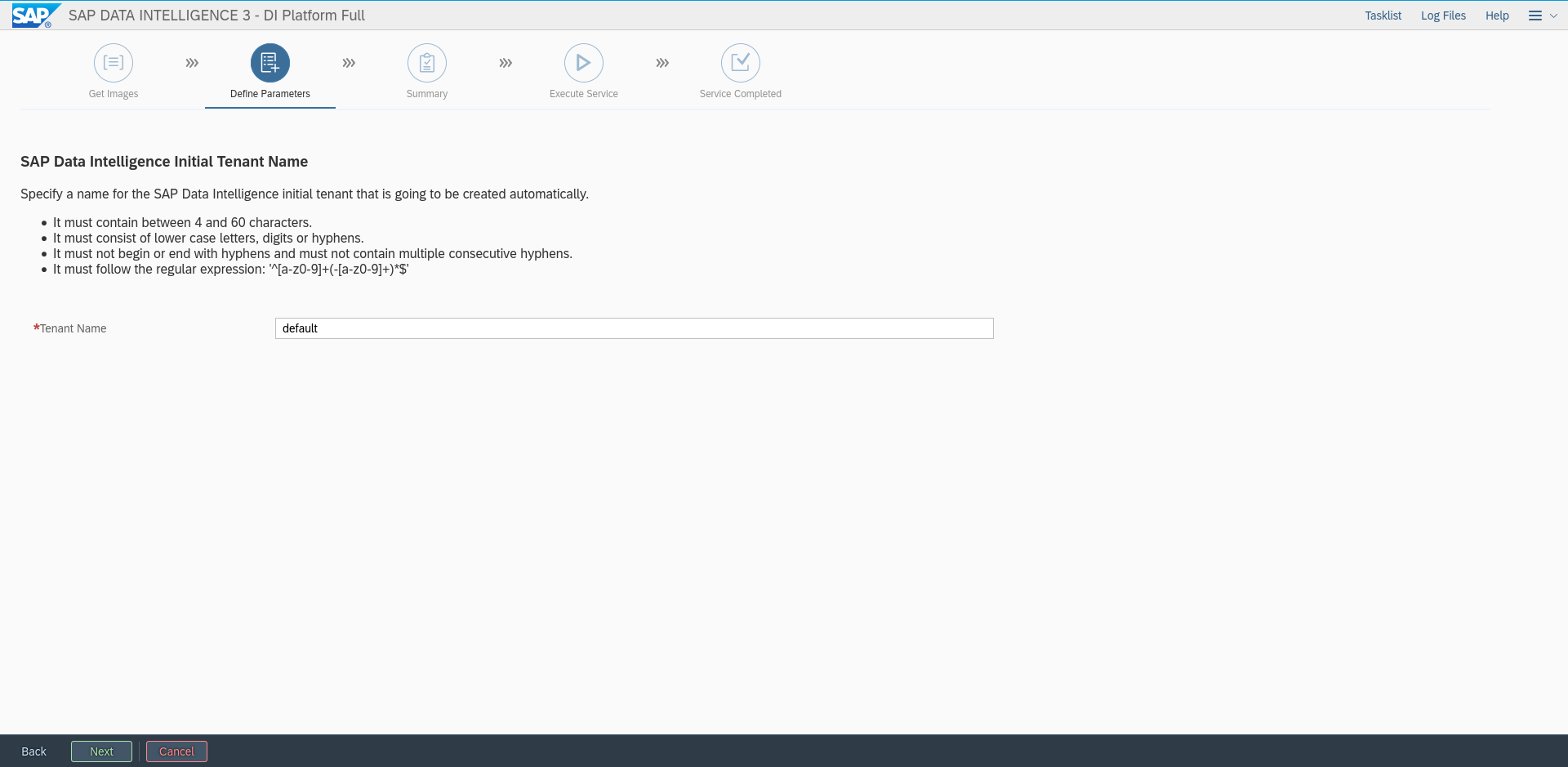
Figure 59: Enter System tenant password #Assign a name to the initially created tenant, for example "default":
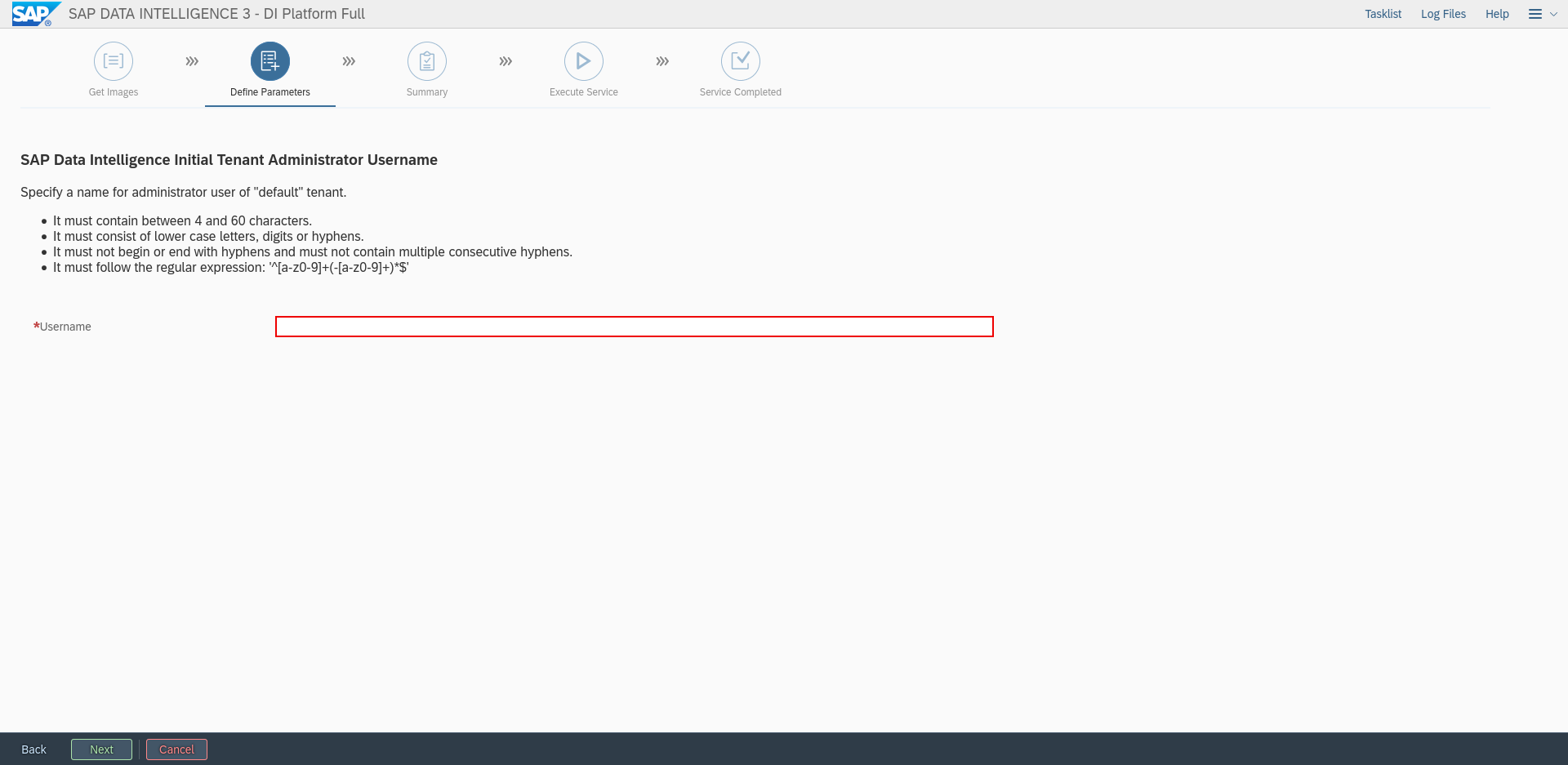
Figure 60: Assign a name to created default tenant #Create the administrator user for the default tenant in SAP DI 3.0:
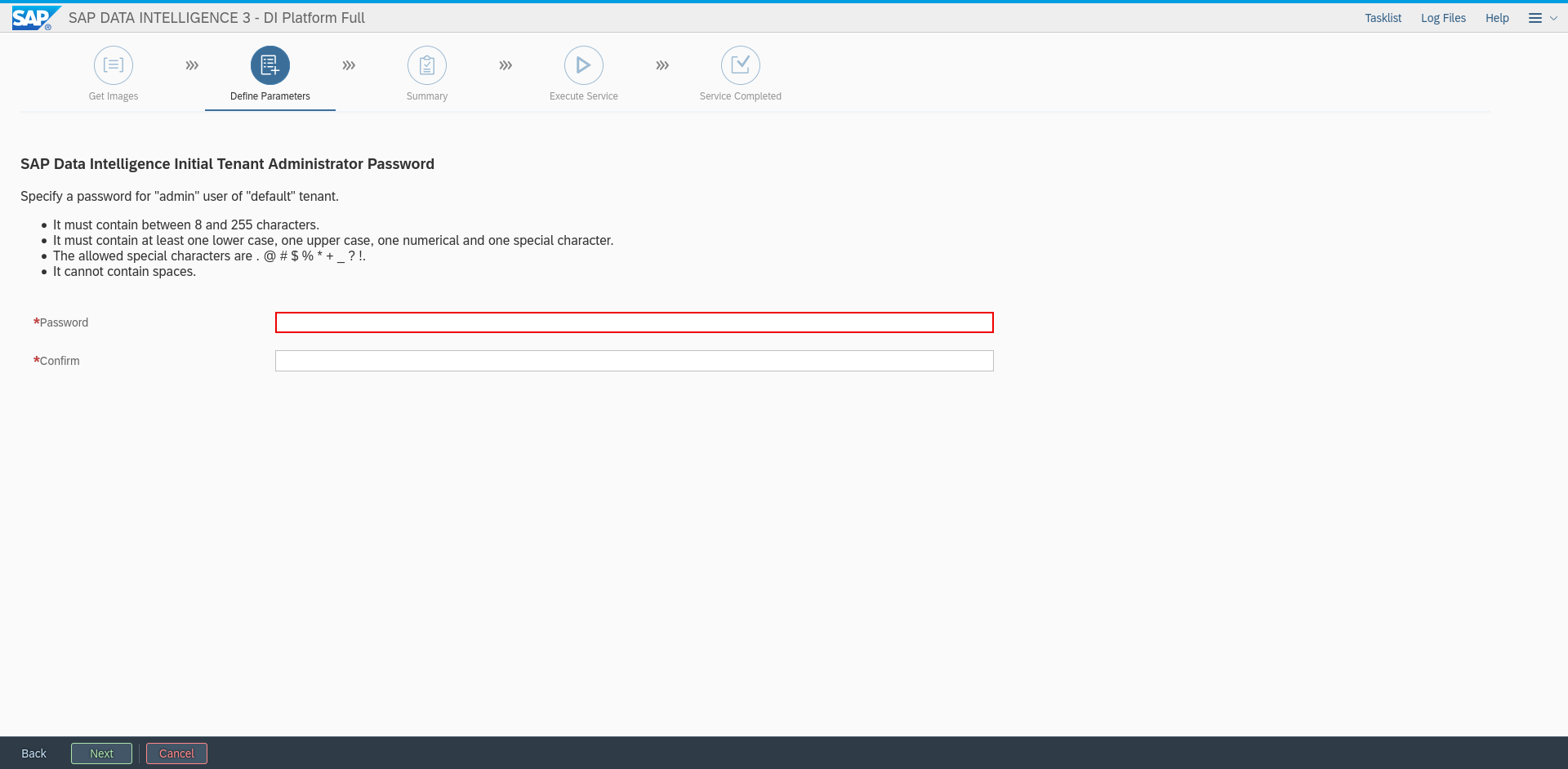
Figure 61: Create Admin user name of default tenant #Set the password for the administrator user of the default tenant:
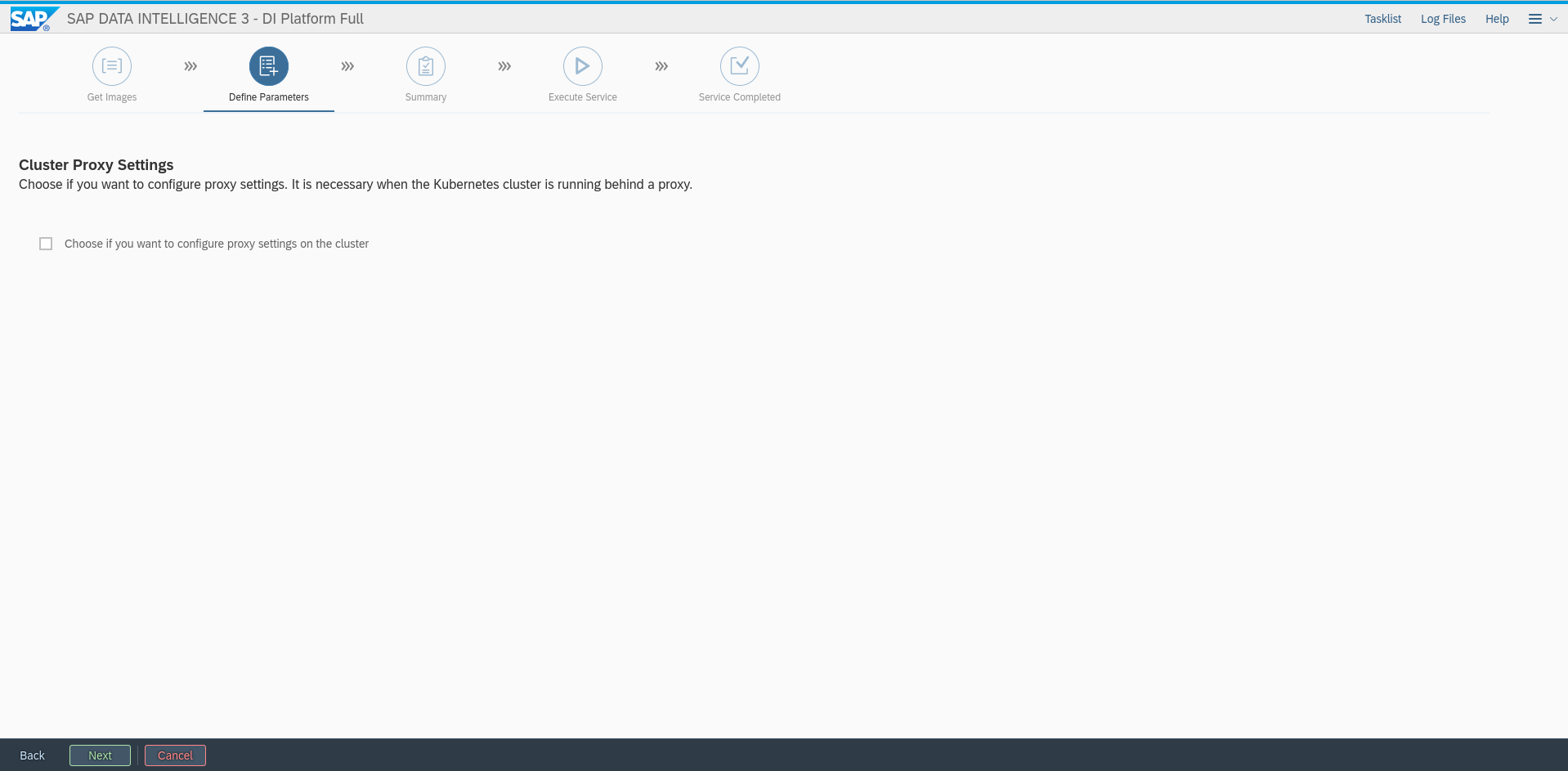
Figure 62: Set admin user password #If you need a proxy to connect to the Internet, set the proxy settings accordingly:
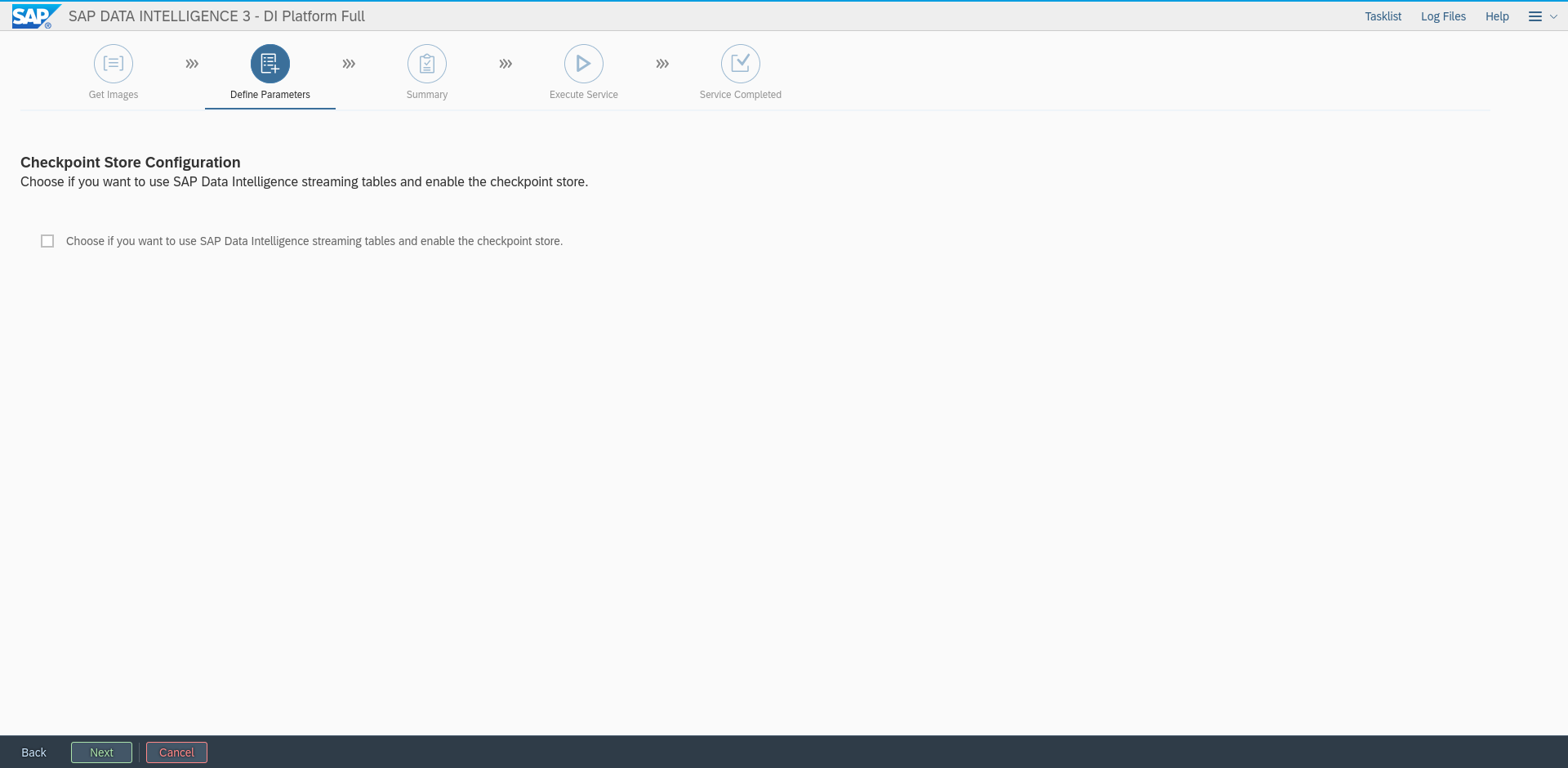
Figure 63: Set proxy settings #Select if you want to use a checkpoint storage:
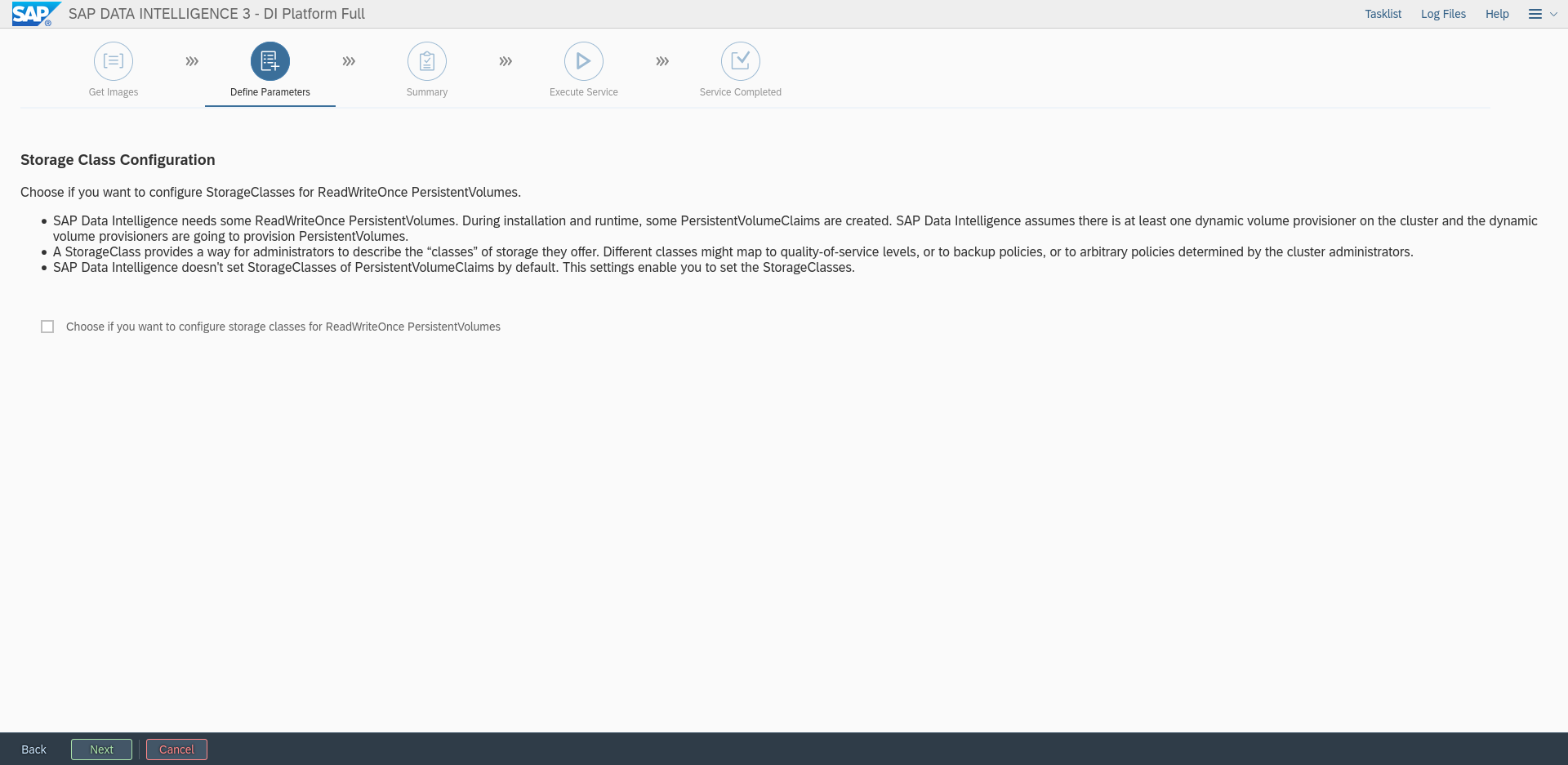
Figure 64: Configure checkpoint storage #Define the storage class that should be used by SAP DI 3.0. Enter the name of the storage class you created previously:
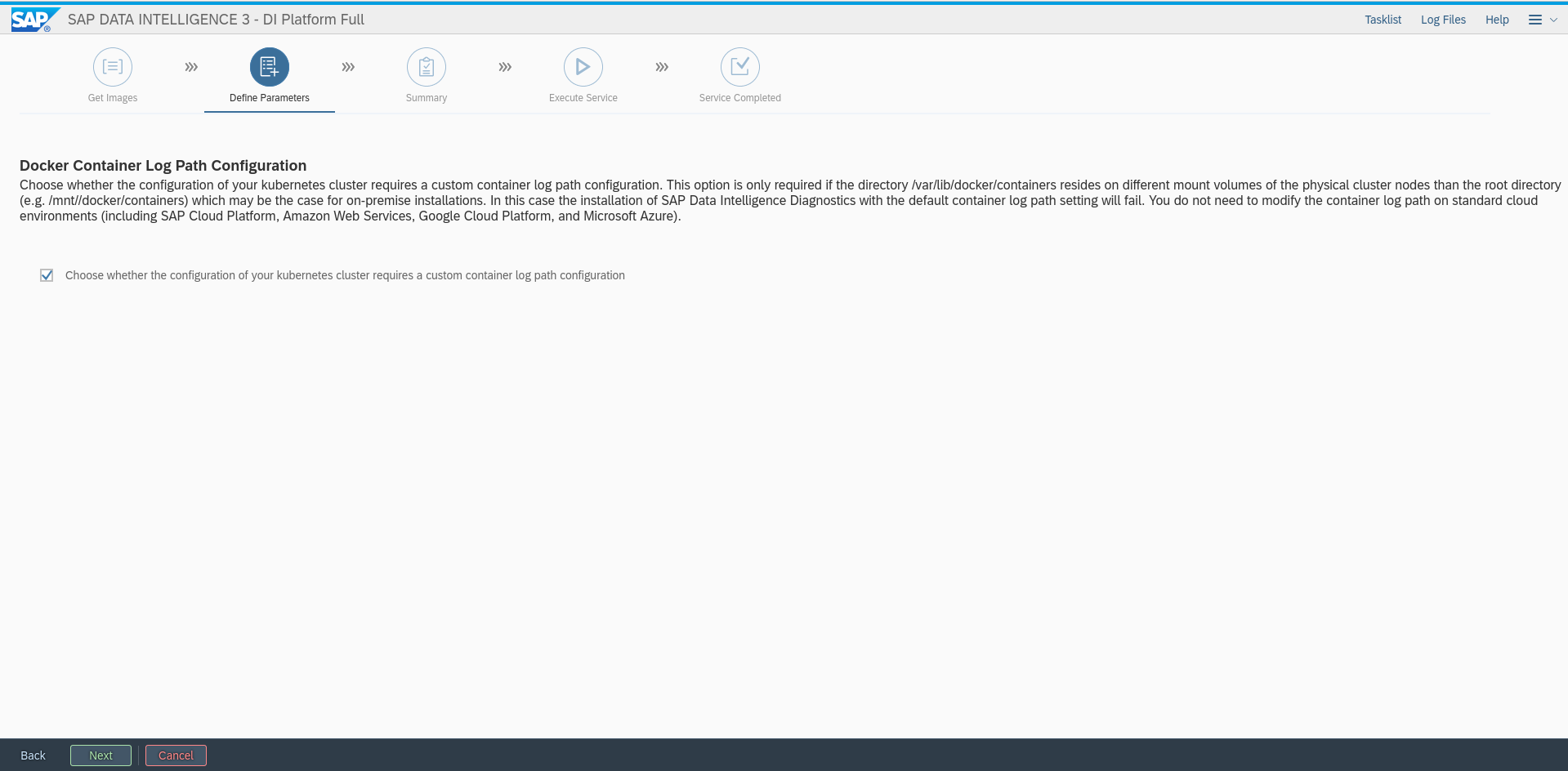
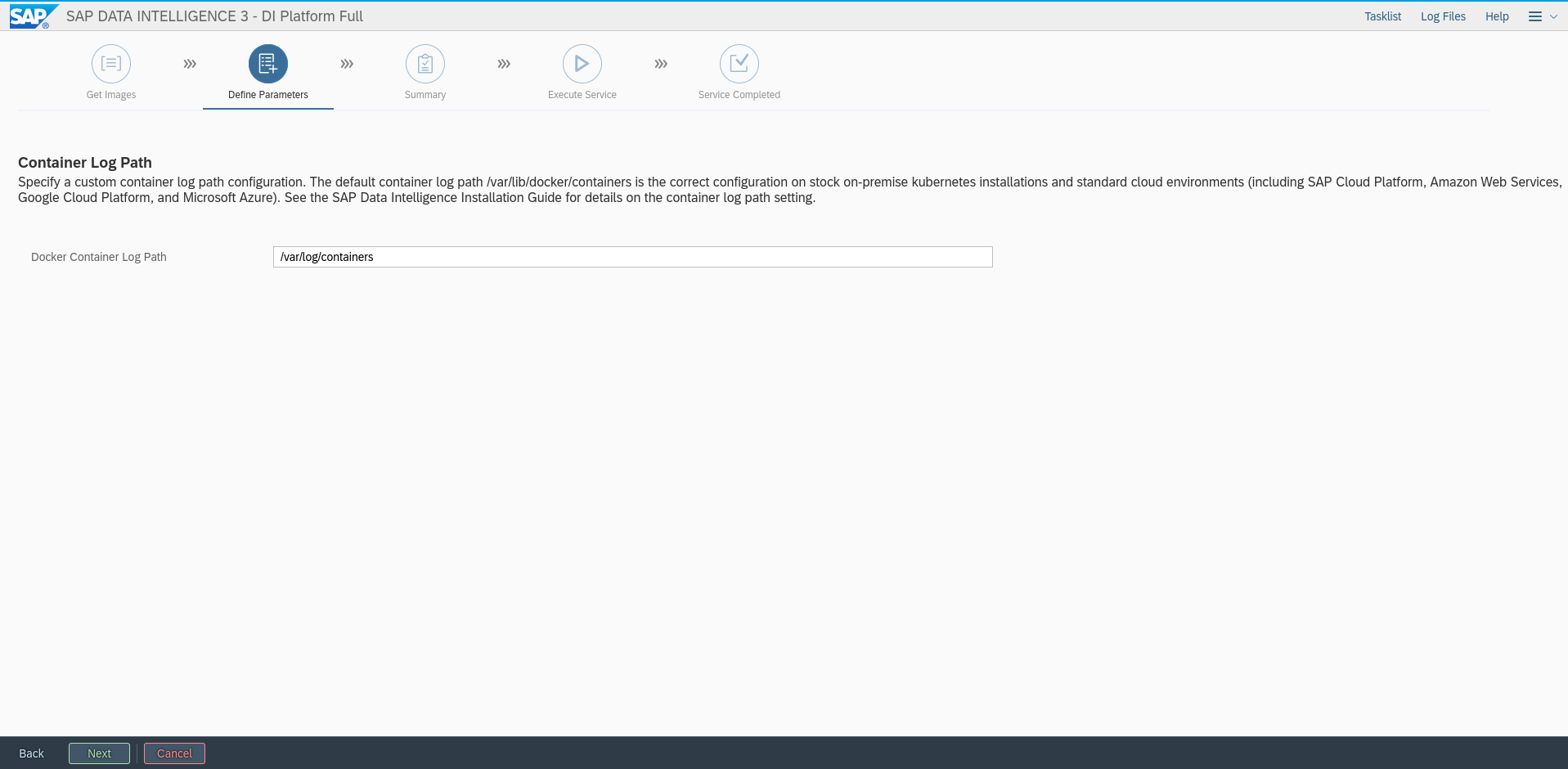
Figure 65: Define storage class to be used #For the SAP DI 3 installation on SUSE CaaSP 4.2 the docker log path needs to be adapted. Check the check box and click "Next":
Figure 66: Adapt Docker log path #Enter the docker log path: "/var/log/containers"
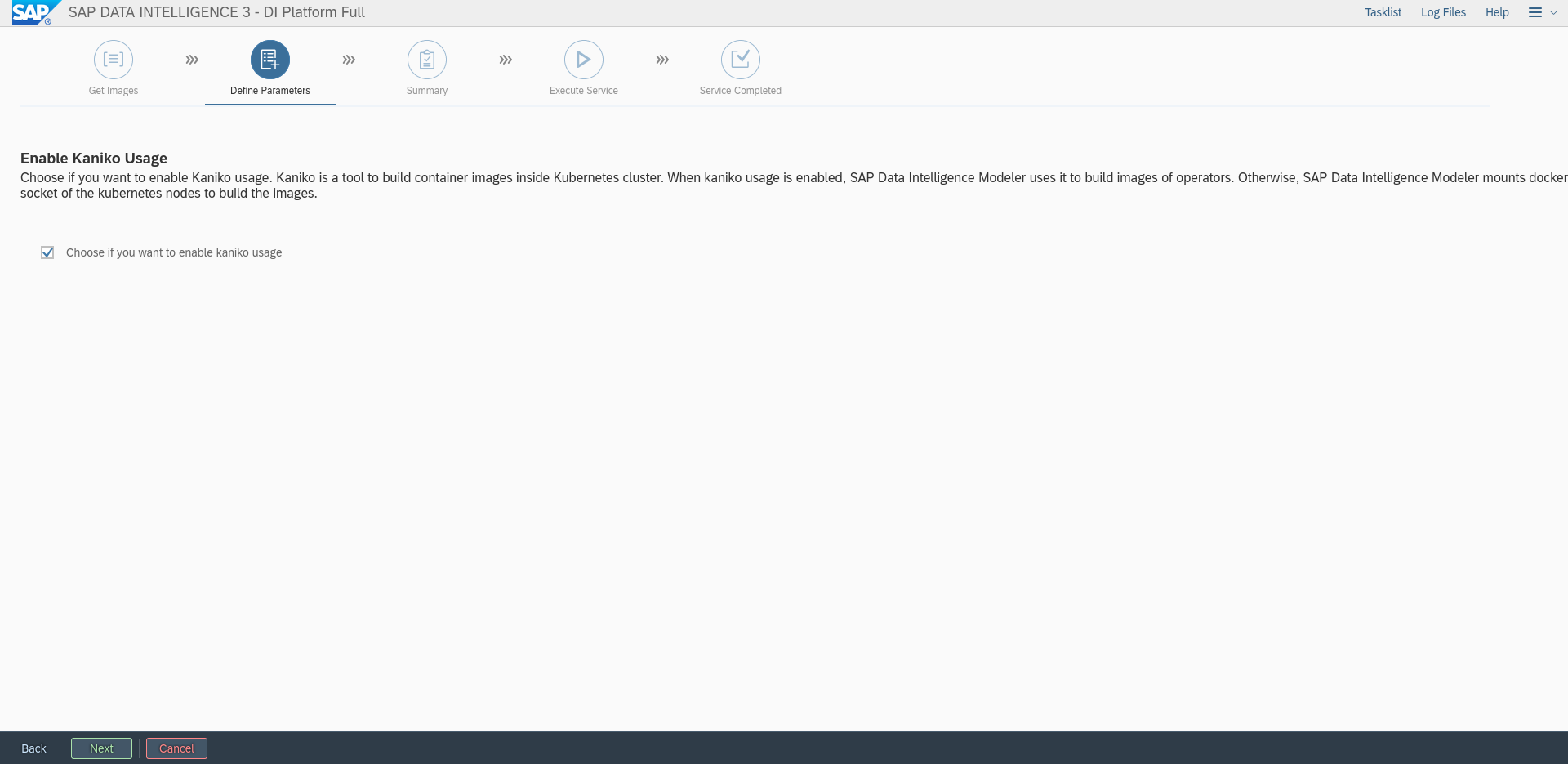
Figure 67: Enter Docker log path #Enable Kaniko:
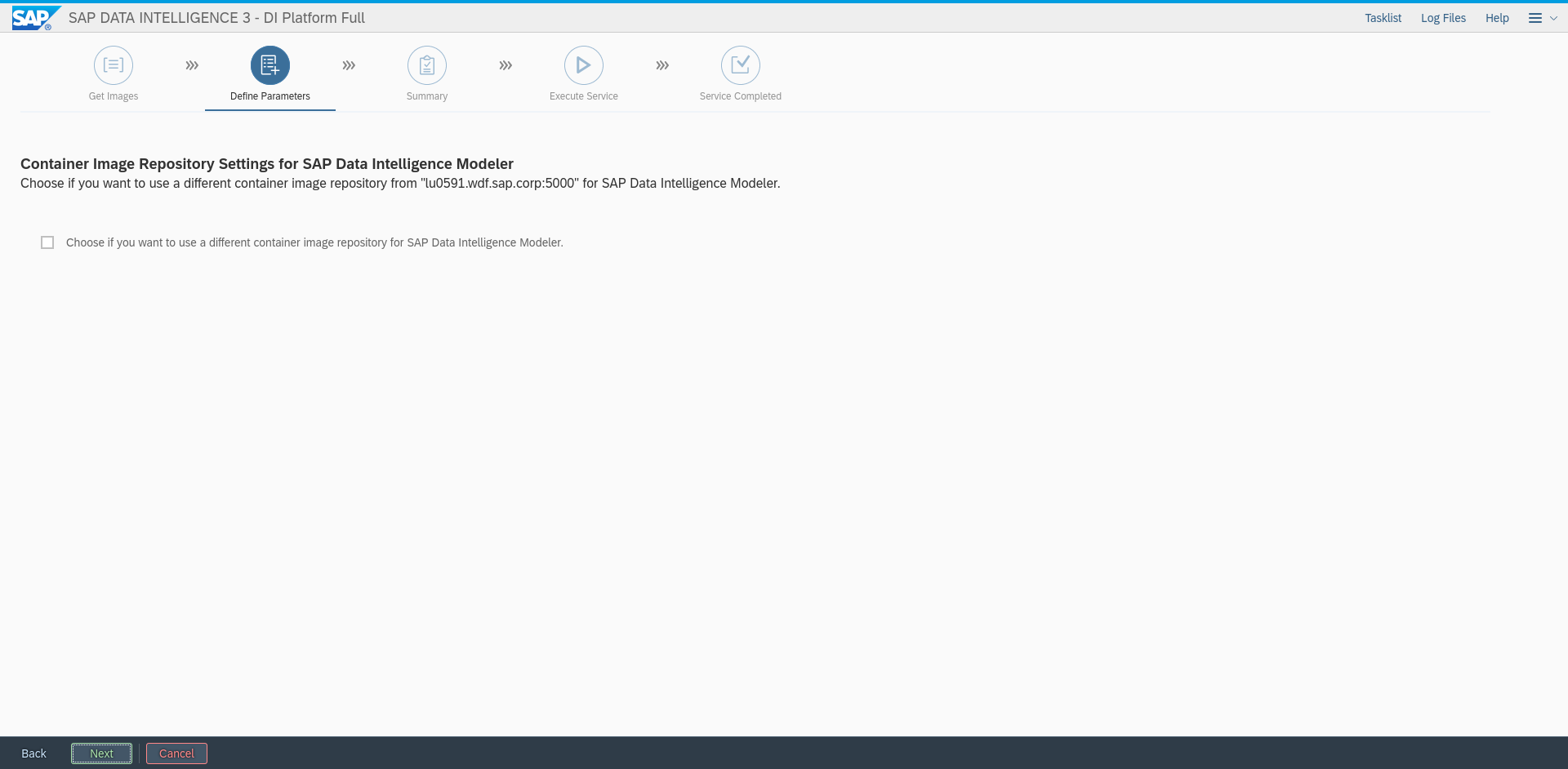
Figure 68: Enable Kaniko #Here, a different private registry can be configured if needed. To proceed, click "Next":
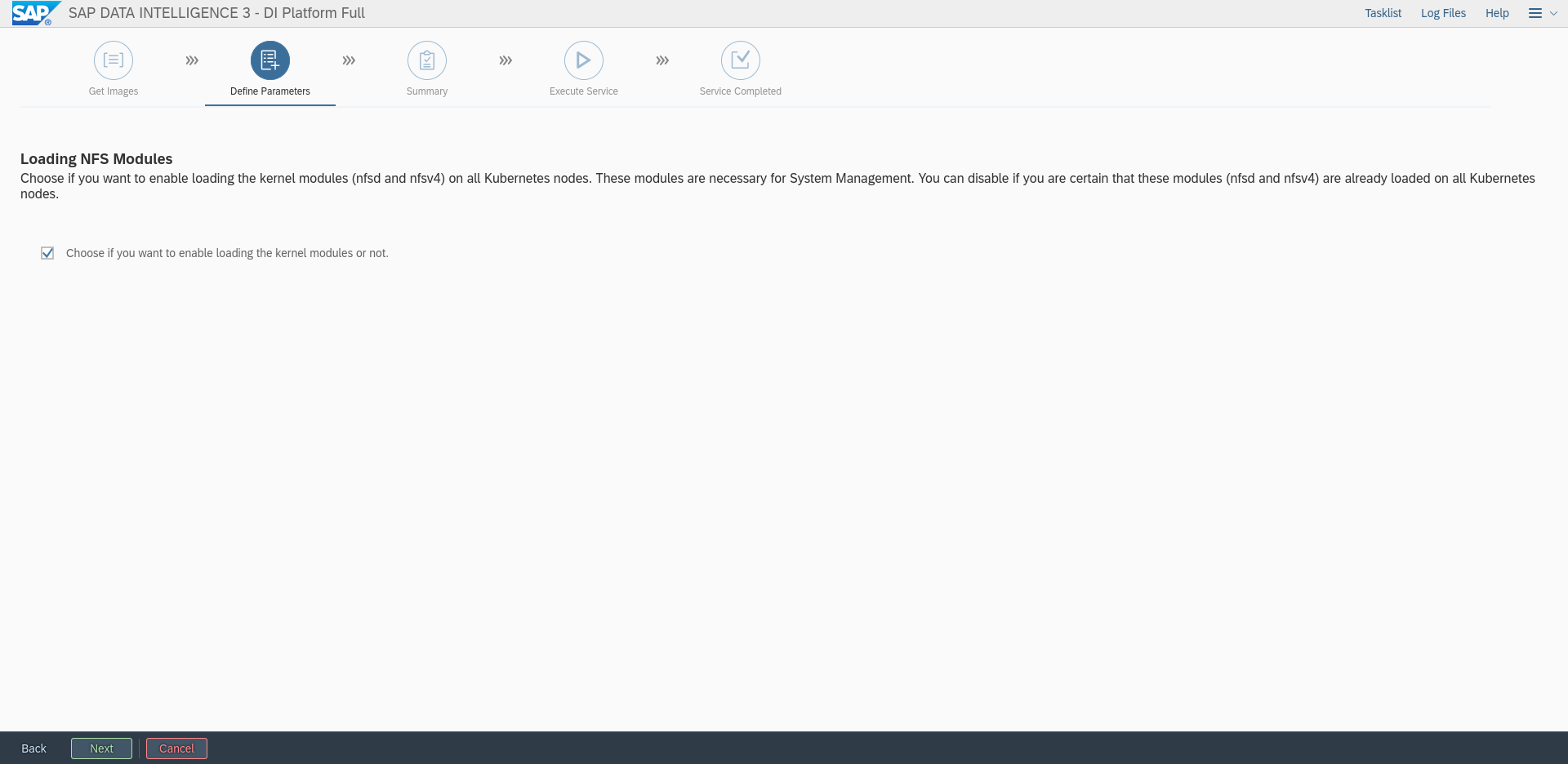
Figure 69: Configure Docker registry for SAP DI Modeler images #Enable the loading of NFS kernel modules. This ensures that the NFS kernel modules are loaded on all Kubernetes nodes. Check the check box and click "Next":
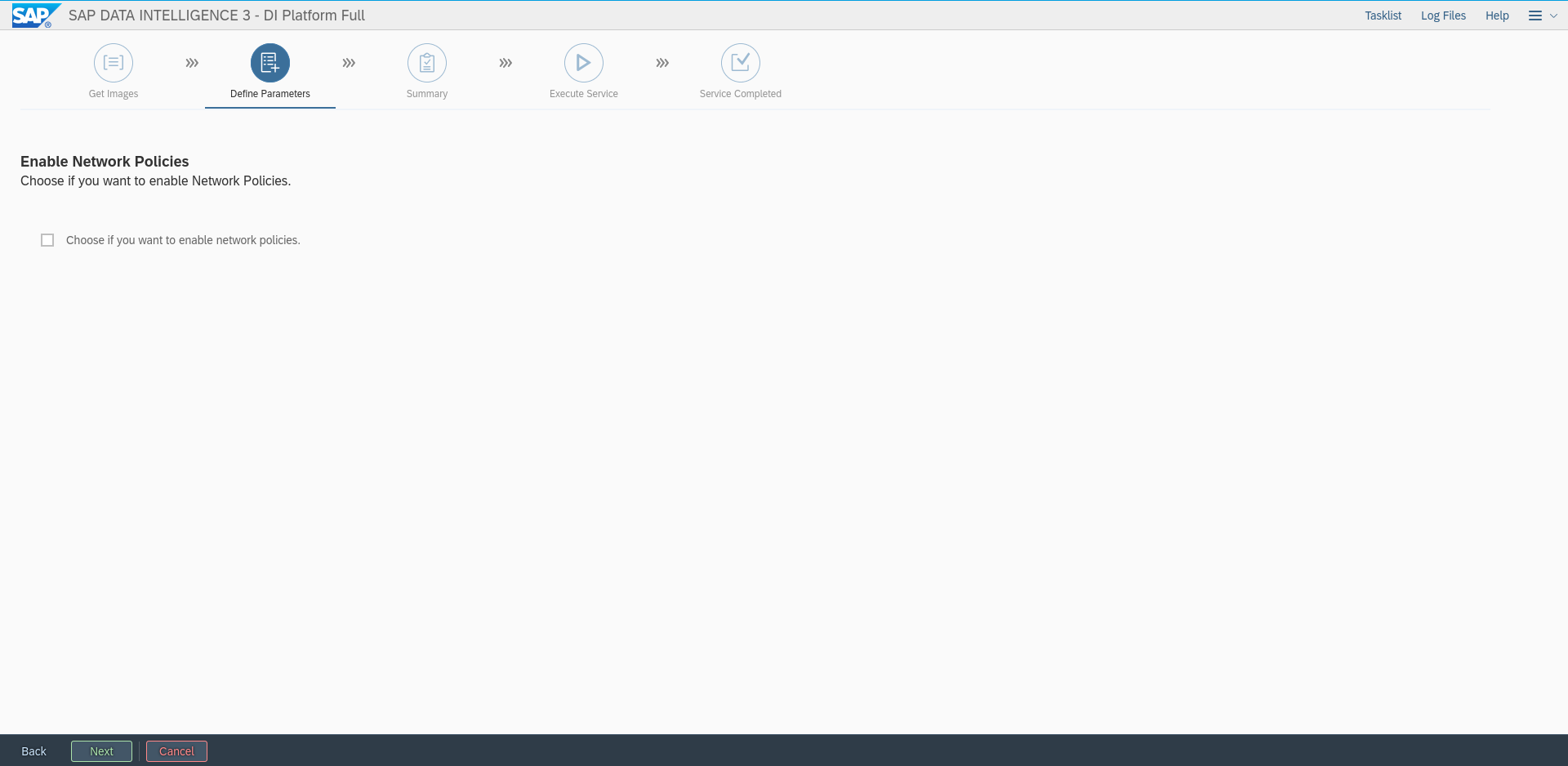
Figure 70: Loading NFS kernel modules #If needed, enable Network policies. Click "Next":
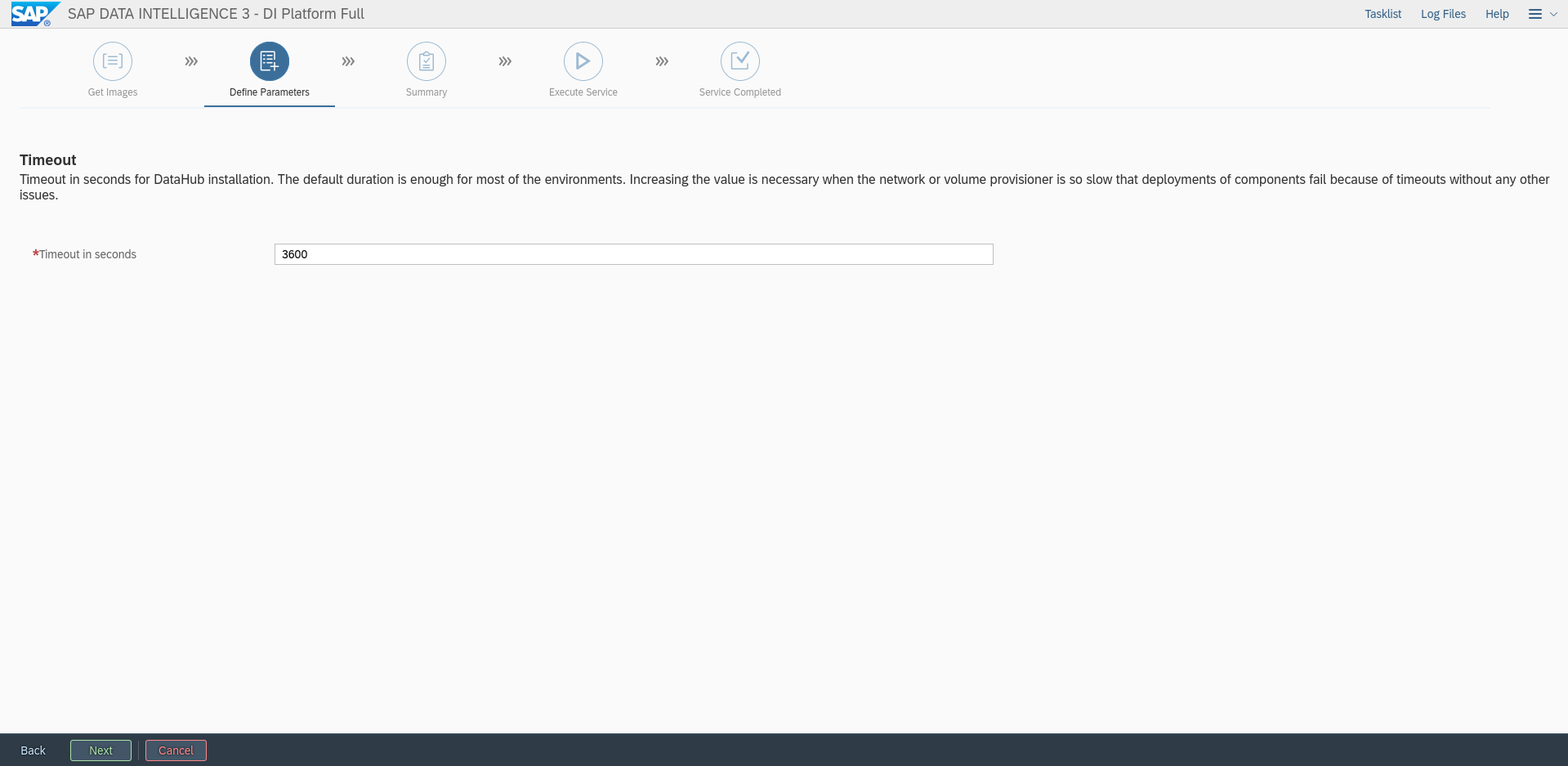
Figure 71: Enable Network policies #Configure timeout during installation, leave the default and click "Next":
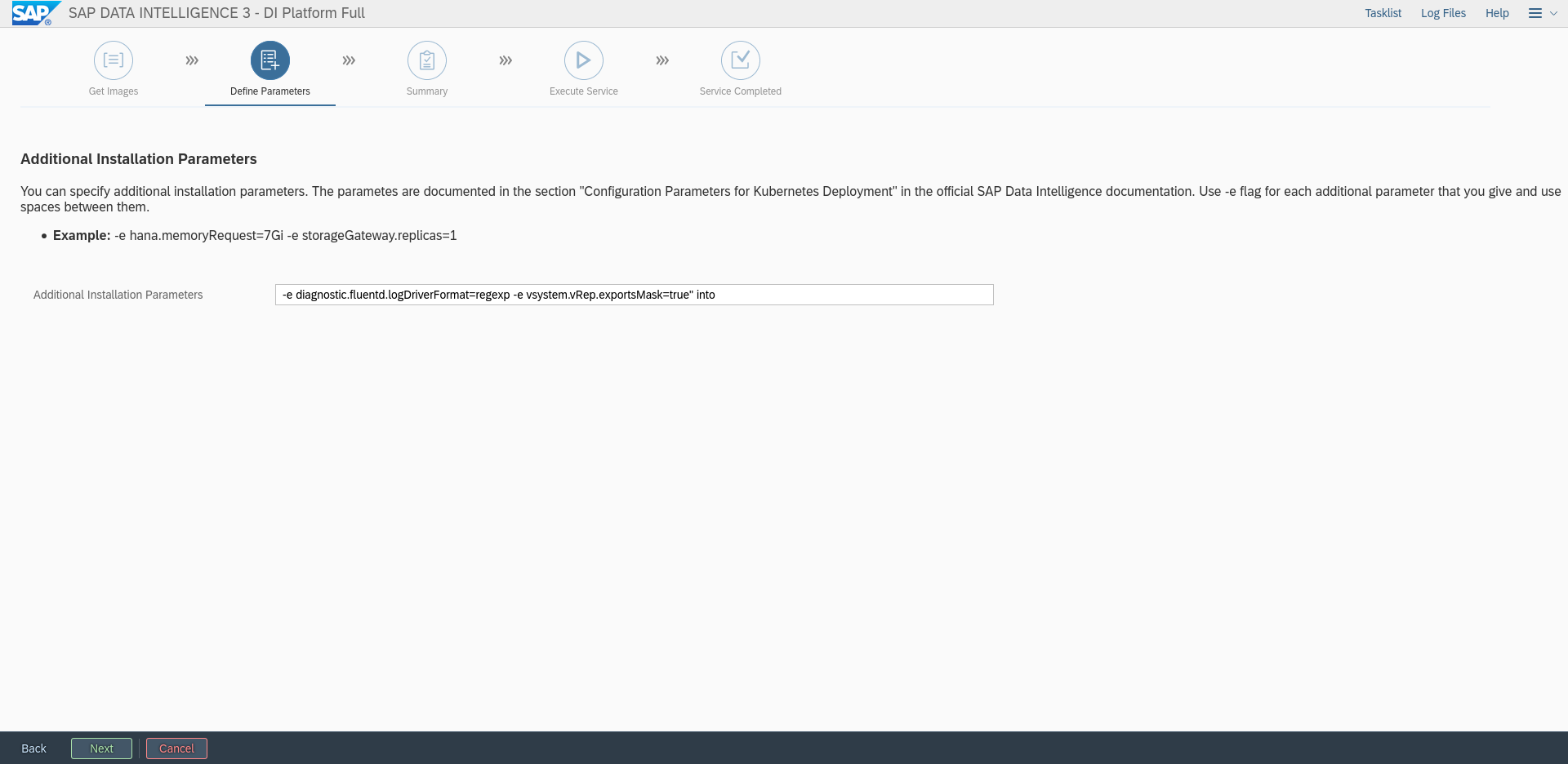
Figure 72: Configuring timeout during installation of SAP DI 3 #In the field "Additional Installation Parameters", enter:
-e diagnostic.fluentd.logDriverFormat=regexp -e vsystem.vRep.exportsMask=trueFigure 73: Additional Installation Parameters 1 #Figure 74: Additional Installation Parameters 2 #
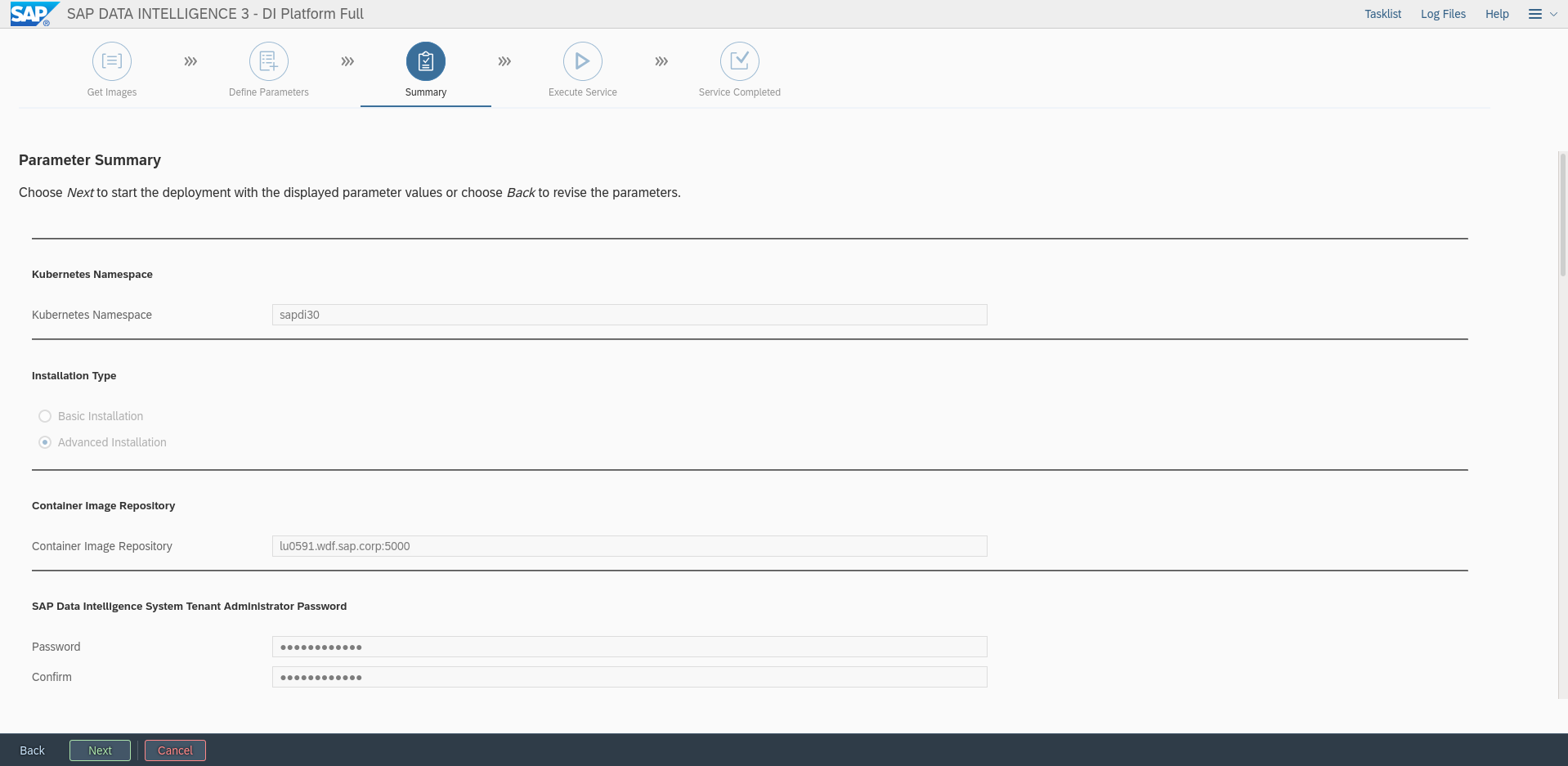
Check the Summary page. Check if the settings are correct:
Figure 75: Summary of Installation parameters #Click "Next" to start the deployment of SAP DI 3.0.
Your installation should now be finished.
7 Legal notice #
Copyright © 2006–2025 SUSE LLC and contributors. All rights reserved.
Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or (at your option) version 1.3; with the Invariant Section being this copyright notice and license. A copy of the license version 1.2 is included in the section entitled "GNU Free Documentation License".
SUSE, the SUSE logo and YaST are registered trademarks of SUSE LLC in the United States and other countries. For SUSE trademarks, see https://www.suse.com/company/legal/.
Linux is a registered trademark of Linus Torvalds. All other names or trademarks mentioned in this document may be trademarks or registered trademarks of their respective owners.
Documents published as part of the SUSE Best Practices series have been contributed voluntarily by SUSE employees and third parties. They are meant to serve as examples of how particular actions can be performed. They have been compiled with utmost attention to detail. However, this does not guarantee complete accuracy. SUSE cannot verify that actions described in these documents do what is claimed or whether actions described have unintended consequences. SUSE LLC, its affiliates, the authors, and the translators may not be held liable for possible errors or the consequences thereof.
Below we draw your attention to the license under which the articles are published.
8 GNU Free Documentation License #
Copyright © 2000, 2001, 2002 Free Software Foundation, Inc. 51 Franklin St, Fifth Floor, Boston, MA 02110-1301 USA. Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is not allowed.
0. PREAMBLE#
The purpose of this License is to make a manual, textbook, or other functional and useful document "free" in the sense of freedom: to assure everyone the effective freedom to copy and redistribute it, with or without modifying it, either commercially or noncommercially. Secondarily, this License preserves for the author and publisher a way to get credit for their work, while not being considered responsible for modifications made by others.
This License is a kind of "copyleft", which means that derivative works of the document must themselves be free in the same sense. It complements the GNU General Public License, which is a copyleft license designed for free software.
We have designed this License in order to use it for manuals for free software, because free software needs free documentation: a free program should come with manuals providing the same freedoms that the software does. But this License is not limited to software manuals; it can be used for any textual work, regardless of subject matter or whether it is published as a printed book. We recommend this License principally for works whose purpose is instruction or reference.
1. APPLICABILITY AND DEFINITIONS#
This License applies to any manual or other work, in any medium, that contains a notice placed by the copyright holder saying it can be distributed under the terms of this License. Such a notice grants a world-wide, royalty-free license, unlimited in duration, to use that work under the conditions stated herein. The "Document", below, refers to any such manual or work. Any member of the public is a licensee, and is addressed as "you". You accept the license if you copy, modify or distribute the work in a way requiring permission under copyright law.
A "Modified Version" of the Document means any work containing the Document or a portion of it, either copied verbatim, or with modifications and/or translated into another language.
A "Secondary Section" is a named appendix or a front-matter section of the Document that deals exclusively with the relationship of the publishers or authors of the Document to the Document’s overall subject (or to related matters) and contains nothing that could fall directly within that overall subject. (Thus, if the Document is in part a textbook of mathematics, a Secondary Section may not explain any mathematics.) The relationship could be a matter of historical connection with the subject or with related matters, or of legal, commercial, philosophical, ethical or political position regarding them.
The "Invariant Sections" are certain Secondary Sections whose titles are designated, as being those of Invariant Sections, in the notice that says that the Document is released under this License. If a section does not fit the above definition of Secondary then it is not allowed to be designated as Invariant. The Document may contain zero Invariant Sections. If the Document does not identify any Invariant Sections then there are none.
The "Cover Texts" are certain short passages of text that are listed, as Front-Cover Texts or Back-Cover Texts, in the notice that says that the Document is released under this License. A Front-Cover Text may be at most 5 words, and a Back-Cover Text may be at most 25 words.
A "Transparent" copy of the Document means a machine-readable copy, represented in a format whose specification is available to the general public, that is suitable for revising the document straightforwardly with generic text editors or (for images composed of pixels) generic paint programs or (for drawings) some widely available drawing editor, and that is suitable for input to text formatters or for automatic translation to a variety of formats suitable for input to text formatters. A copy made in an otherwise Transparent file format whose markup, or absence of markup, has been arranged to thwart or discourage subsequent modification by readers is not Transparent. An image format is not Transparent if used for any substantial amount of text. A copy that is not "Transparent" is called "Opaque".
Examples of suitable formats for Transparent copies include plain ASCII without markup, Texinfo input format, LaTeX input format, SGML or XML using a publicly available DTD, and standard-conforming simple HTML, PostScript or PDF designed for human modification. Examples of transparent image formats include PNG, XCF and JPG. Opaque formats include proprietary formats that can be read and edited only by proprietary word processors, SGML or XML for which the DTD and/or processing tools are not generally available, and the machine-generated HTML, PostScript or PDF produced by some word processors for output purposes only.
The "Title Page" means, for a printed book, the title page itself, plus such following pages as are needed to hold, legibly, the material this License requires to appear in the title page. For works in formats which do not have any title page as such, "Title Page" means the text near the most prominent appearance of the work’s title, preceding the beginning of the body of the text.
A section "Entitled XYZ" means a named subunit of the Document whose title either is precisely XYZ or contains XYZ in parentheses following text that translates XYZ in another language. (Here XYZ stands for a specific section name mentioned below, such as "Acknowledgements", "Dedications", "Endorsements", or "History".) To "Preserve the Title" of such a section when you modify the Document means that it remains a section "Entitled XYZ" according to this definition.
The Document may include Warranty Disclaimers next to the notice which states that this License applies to the Document. These Warranty Disclaimers are considered to be included by reference in this License, but only as regards disclaiming warranties: any other implication that these Warranty Disclaimers may have is void and has no effect on the meaning of this License.
2. VERBATIM COPYING#
You may copy and distribute the Document in any medium, either commercially or noncommercially, provided that this License, the copyright notices, and the license notice saying this License applies to the Document are reproduced in all copies, and that you add no other conditions whatsoever to those of this License. You may not use technical measures to obstruct or control the reading or further copying of the copies you make or distribute. However, you may accept compensation in exchange for copies. If you distribute a large enough number of copies you must also follow the conditions in section 3.
You may also lend copies, under the same conditions stated above, and you may publicly display copies.
3. COPYING IN QUANTITY#
If you publish printed copies (or copies in media that commonly have printed covers) of the Document, numbering more than 100, and the Document’s license notice requires Cover Texts, you must enclose the copies in covers that carry, clearly and legibly, all these Cover Texts: Front-Cover Texts on the front cover, and Back-Cover Texts on the back cover. Both covers must also clearly and legibly identify you as the publisher of these copies. The front cover must present the full title with all words of the title equally prominent and visible. You may add other material on the covers in addition. Copying with changes limited to the covers, as long as they preserve the title of the Document and satisfy these conditions, can be treated as verbatim copying in other respects.
If the required texts for either cover are too voluminous to fit legibly, you should put the first ones listed (as many as fit reasonably) on the actual cover, and continue the rest onto adjacent pages.
If you publish or distribute Opaque copies of the Document numbering more than 100, you must either include a machine-readable Transparent copy along with each Opaque copy, or state in or with each Opaque copy a computer-network location from which the general network-using public has access to download using public-standard network protocols a complete Transparent copy of the Document, free of added material. If you use the latter option, you must take reasonably prudent steps, when you begin distribution of Opaque copies in quantity, to ensure that this Transparent copy will remain thus accessible at the stated location until at least one year after the last time you distribute an Opaque copy (directly or through your agents or retailers) of that edition to the public.
It is requested, but not required, that you contact the authors of the Document well before redistributing any large number of copies, to give them a chance to provide you with an updated version of the Document.
4. MODIFICATIONS#
You may copy and distribute a Modified Version of the Document under the conditions of sections 2 and 3 above, provided that you release the Modified Version under precisely this License, with the Modified Version filling the role of the Document, thus licensing distribution and modification of the Modified Version to whoever possesses a copy of it. In addition, you must do these things in the Modified Version:
Use in the Title Page (and on the covers, if any) a title distinct from that of the Document, and from those of previous versions (which should, if there were any, be listed in the History section of the Document). You may use the same title as a previous version if the original publisher of that version gives permission.
List on the Title Page, as authors, one or more persons or entities responsible for authorship of the modifications in the Modified Version, together with at least five of the principal authors of the Document (all of its principal authors, if it has fewer than five), unless they release you from this requirement.
State on the Title page the name of the publisher of the Modified Version, as the publisher.
Preserve all the copyright notices of the Document.
Add an appropriate copyright notice for your modifications adjacent to the other copyright notices.
Include, immediately after the copyright notices, a license notice giving the public permission to use the Modified Version under the terms of this License, in the form shown in the Addendum below.
Preserve in that license notice the full lists of Invariant Sections and required Cover Texts given in the Document’s license notice.
Include an unaltered copy of this License.
Preserve the section Entitled "History", Preserve its Title, and add to it an item stating at least the title, year, new authors, and publisher of the Modified Version as given on the Title Page. If there is no section Entitled "History" in the Document, create one stating the title, year, authors, and publisher of the Document as given on its Title Page, then add an item describing the Modified Version as stated in the previous sentence.
Preserve the network location, if any, given in the Document for public access to a Transparent copy of the Document, and likewise the network locations given in the Document for previous versions it was based on. These may be placed in the "History" section. You may omit a network location for a work that was published at least four years before the Document itself, or if the original publisher of the version it refers to gives permission.
For any section Entitled "Acknowledgements" or "Dedications", Preserve the Title of the section, and preserve in the section all the substance and tone of each of the contributor acknowledgements and/or dedications given therein.
Preserve all the Invariant Sections of the Document, unaltered in their text and in their titles. Section numbers or the equivalent are not considered part of the section titles.
Delete any section Entitled "Endorsements". Such a section may not be included in the Modified Version.
Do not retitle any existing section to be Entitled "Endorsements" or to conflict in title with any Invariant Section.
Preserve any Warranty Disclaimers.
If the Modified Version includes new front-matter sections or appendices that qualify as Secondary Sections and contain no material copied from the Document, you may at your option designate some or all of these sections as invariant. To do this, add their titles to the list of Invariant Sections in the Modified Version’s license notice. These titles must be distinct from any other section titles.
You may add a section Entitled "Endorsements", provided it contains nothing but endorsements of your Modified Version by various parties—for example, statements of peer review or that the text has been approved by an organization as the authoritative definition of a standard.
You may add a passage of up to five words as a Front-Cover Text, and a passage of up to 25 words as a Back-Cover Text, to the end of the list of Cover Texts in the Modified Version. Only one passage of Front-Cover Text and one of Back-Cover Text may be added by (or through arrangements made by) any one entity. If the Document already includes a cover text for the same cover, previously added by you or by arrangement made by the same entity you are acting on behalf of, you may not add another; but you may replace the old one, on explicit permission from the previous publisher that added the old one.
The author(s) and publisher(s) of the Document do not by this License give permission to use their names for publicity for or to assert or imply endorsement of any Modified Version.
5. COMBINING DOCUMENTS#
You may combine the Document with other documents released under this License, under the terms defined in section 4 above for modified versions, provided that you include in the combination all of the Invariant Sections of all of the original documents, unmodified, and list them all as Invariant Sections of your combined work in its license notice, and that you preserve all their Warranty Disclaimers.
The combined work need only contain one copy of this License, and multiple identical Invariant Sections may be replaced with a single copy. If there are multiple Invariant Sections with the same name but different contents, make the title of each such section unique by adding at the end of it, in parentheses, the name of the original author or publisher of that section if known, or else a unique number. Make the same adjustment to the section titles in the list of Invariant Sections in the license notice of the combined work.
In the combination, you must combine any sections Entitled "History" in the various original documents, forming one section Entitled "History"; likewise combine any sections Entitled "Acknowledgements", and any sections Entitled "Dedications". You must delete all sections Entitled "Endorsements".
6. COLLECTIONS OF DOCUMENTS#
You may make a collection consisting of the Document and other documents released under this License, and replace the individual copies of this License in the various documents with a single copy that is included in the collection, provided that you follow the rules of this License for verbatim copying of each of the documents in all other respects.
You may extract a single document from such a collection, and distribute it individually under this License, provided you insert a copy of this License into the extracted document, and follow this License in all other respects regarding verbatim copying of that document.
7. AGGREGATION WITH INDEPENDENT WORKS#
A compilation of the Document or its derivatives with other separate and independent documents or works, in or on a volume of a storage or distribution medium, is called an "aggregate" if the copyright resulting from the compilation is not used to limit the legal rights of the compilation’s users beyond what the individual works permit. When the Document is included in an aggregate, this License does not apply to the other works in the aggregate which are not themselves derivative works of the Document.
If the Cover Text requirement of section 3 is applicable to these copies of the Document, then if the Document is less than one half of the entire aggregate, the Document’s Cover Texts may be placed on covers that bracket the Document within the aggregate, or the electronic equivalent of covers if the Document is in electronic form. Otherwise they must appear on printed covers that bracket the whole aggregate.
8. TRANSLATION#
Translation is considered a kind of modification, so you may distribute translations of the Document under the terms of section 4. Replacing Invariant Sections with translations requires special permission from their copyright holders, but you may include translations of some or all Invariant Sections in addition to the original versions of these Invariant Sections. You may include a translation of this License, and all the license notices in the Document, and any Warranty Disclaimers, provided that you also include the original English version of this License and the original versions of those notices and disclaimers. In case of a disagreement between the translation and the original version of this License or a notice or disclaimer, the original version will prevail.
If a section in the Document is Entitled "Acknowledgements", "Dedications", or "History", the requirement (section 4) to Preserve its Title (section 1) will typically require changing the actual title.
9. TERMINATION#
You may not copy, modify, sublicense, or distribute the Document except as expressly provided for under this License. Any other attempt to copy, modify, sublicense or distribute the Document is void, and will automatically terminate your rights under this License. However, parties who have received copies, or rights, from you under this License will not have their licenses terminated so long as such parties remain in full compliance.
10. FUTURE REVISIONS OF THIS LICENSE#
The Free Software Foundation may publish new, revised versions of the GNU Free Documentation License from time to time. Such new versions will be similar in spirit to the present version, but may differ in detail to address new problems or concerns. See http://www.gnu.org/copyleft/.
Each version of the License is given a distinguishing version number. If the Document specifies that a particular numbered version of this License "or any later version" applies to it, you have the option of following the terms and conditions either of that specified version or of any later version that has been published (not as a draft) by the Free Software Foundation. If the Document does not specify a version number of this License, you may choose any version ever published (not as a draft) by the Free Software Foundation.
ADDENDUM: How to use this License for your documents#
Copyright (c) YEAR YOUR NAME. Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or any later version published by the Free Software Foundation; with no Invariant Sections, no Front-Cover Texts, and no Back-Cover Texts. A copy of the license is included in the section entitled “GNU Free Documentation License”.
If you have Invariant Sections, Front-Cover Texts and Back-Cover Texts, replace the “ with…Texts.” line with this:
with the Invariant Sections being LIST THEIR TITLES, with the Front-Cover Texts being LIST, and with the Back-Cover Texts being LIST.
If you have Invariant Sections without Cover Texts, or some other combination of the three, merge those two alternatives to suit the situation.
If your document contains nontrivial examples of program code, we recommend releasing these examples in parallel under your choice of free software license, such as the GNU General Public License, to permit their use in free software.