7 YaST online update #
SUSE offers a continuous stream of software security updates for your product. By default, the update applet is used to keep your system up to date. Refer to Section 8.5, “The GNOME package updater” for further information on the update applet. This chapter covers the alternative tool for updating software packages: YaST Online Update.
The current patches for SUSE® Linux Enterprise Server are available from an update software repository. If you have registered your product during the installation, an update repository is already configured. If you have not registered SUSE Linux Enterprise Server, you can do so by starting the in YaST. Alternatively, you can manually add an update repository from a source you trust. To add or remove repositories, start the Repository Manager with › in YaST. Learn more about the Repository Manager in Section 8.4, “Managing software repositories and services”.
If you are not able to access the update catalog, this may happen because of an expired subscription. Normally, SUSE Linux Enterprise Server comes with a one-year or three-year subscription, during which you have access to the update catalog. This access will be denied after the subscription ends.
If an access to the update catalog is denied, you can see a warning message prompting you to visit the SUSE Customer Center and check your subscription. The SUSE Customer Center is available at https://scc.suse.com//.
By default, the firewall on SUSE Linux Enterprise Server only blocks incoming connections.
If your system is behind another firewall that blocks outgoing traffic,
make sure to allow connections to https://scc.suse.com/ and
https://updates.suse.com on ports 80 and 443 in order
to receive updates.
SUSE provides updates with different relevance levels:
- Security updates
Fix severe security hazards and should always be installed.
- Recommended updates
Fix issues that could compromise your computer.
- Optional updates
Fix non-security relevant issues or provide enhancements.
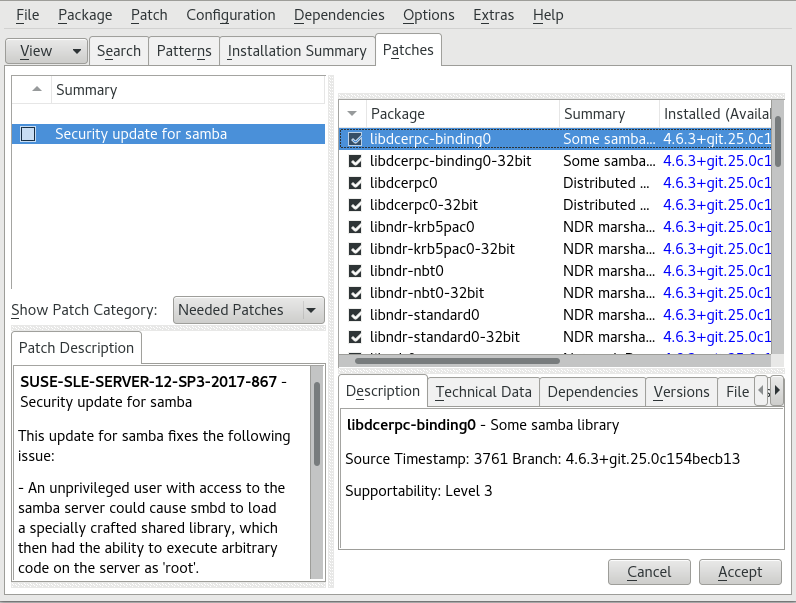
7.1 The online update dialog #
To open the YaST dialog, start YaST and
select › . Alternatively, start it from the command
line with yast2 online_update.
The window consists of four sections.
The section on the left lists the available
patches for SUSE Linux Enterprise Server. The patches are sorted by security relevance:
security, recommended, and
optional. You can change the view of the
section by selecting one of the following options
from :
- (default view)
Non-installed patches that apply to packages installed on your system.
Patches that either apply to packages not installed on your system, or patches that have requirements which have already have been fulfilled (because the relevant packages have already been updated from another source).
All patches available for SUSE Linux Enterprise Server.
Each list entry in the section consists of a
symbol and the patch name. For an overview of the possible symbols and their
meaning, press Shift–F1. Actions required by Security and
Recommended patches are automatically preset. These
actions are ,
and .
If you install an up-to-date package from a repository other than the update repository, the requirements of a patch for this package may be fulfilled with this installation. In this case, a check mark is displayed in front of the patch summary. The patch is visible in the list until you mark it for installation. This does not install the patch (because the package already is up to date), but mark the patch as having been installed.
Select an entry in the section to view a short at the bottom left corner of the dialog. The upper right section lists the packages included in the selected patch (a patch can consist of several packages). Click an entry in the upper right section to view details about the respective package that is included in the patch.
7.2 Installing patches #
The YaST Online Update dialog allows you to either install all available patches at once or manually select the desired patches. You may also revert patches that have been applied to the system.
By default, all new patches (except optional ones) that
are currently available for your system are already marked for installation.
They will be applied automatically once you click
or .
If one or multiple patches require a system reboot, you will be notified
about this before the patch installation starts. You can then either decide
to continue with the installation of the selected patches, skip the
installation of all patches that need rebooting and install the rest, or go
back to the manual patch selection.
Start YaST and select › .
To automatically apply all new patches (except
optionalones) that are currently available for your system, click or .First modify the selection of patches that you want to apply:
Use the respective filters and views that the interface provides. For details, refer to Section 7.1, “The online update dialog”.
Select or deselect patches according to your needs and wishes by right-clicking the patch and choosing the respective action from the context menu.
Important: Always apply security updatesDo not deselect any
security-related patches without a good reason. These patches fix severe security hazards and prevent your system from being exploited.Most patches include updates for several packages. To change actions for single packages, right-click a package in the package view and choose an action.
To confirm your selection and apply the selected patches, proceed with or .
After the installation is complete, click to leave the YaST . Your system is now up to date.
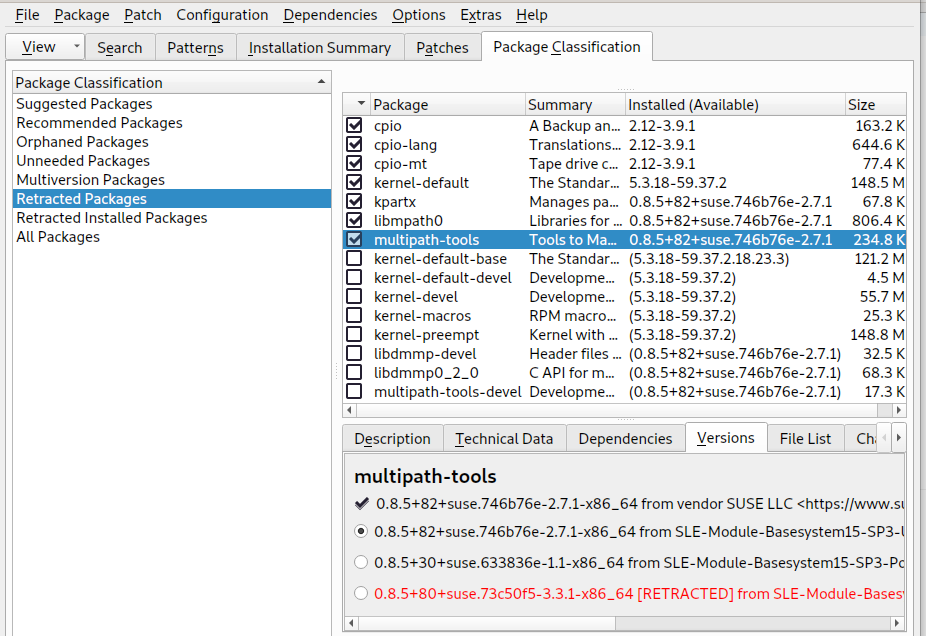
7.3 Viewing retracted patches #
Maintenance updates are carefully tested to minimize the risk of introducing a bug. If a patch proves to contain a bug, it is automatically retracted. A new update (with a higher version number) is issued to revert the buggy patch, and is blocked from being installed again. You can see retracted patches, and their history, on the tab.
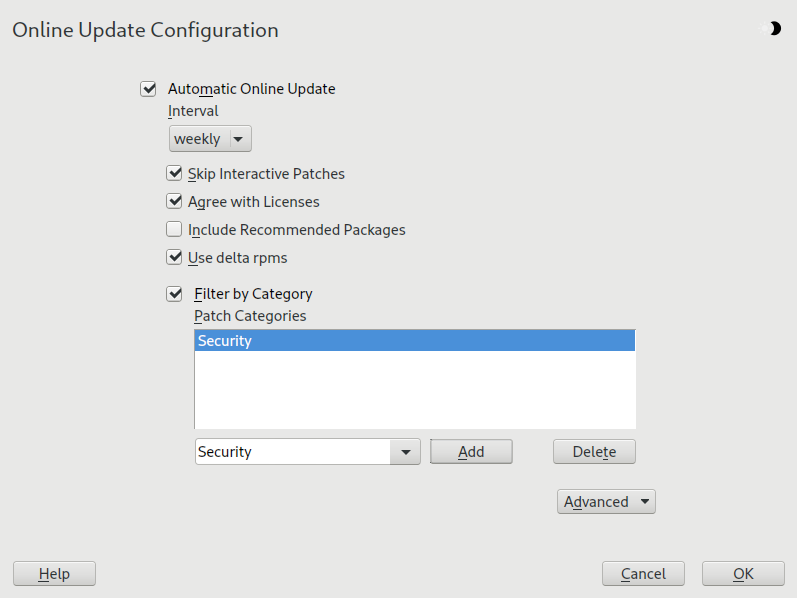
7.4 Automatic online update #
You may configure automatic updates with a daily, weekly or
monthly schedule with YaST. Install the
yast2-online-update-configuration
package.
By default, updates are downloaded as delta RPMs. Since rebuilding RPM packages from delta RPMs is a memory- and processor-intensive task, certain setups or hardware configurations may require you to disable the use of delta RPMs for the sake of performance.
Certain patches, such as kernel updates or packages requiring license agreements, require user interaction, which would cause the automatic update procedure to stop. You can configure skipping patches that require user interaction.
Use the tab in the YaST module to review available and installed patches, including references to bug reports and CVE bulletins.
After installation, start YaST and select › . Choose › . If the yast2-online-update-configuration is not installed, you will be prompted to do that.
Figure 7.3: YaST online update configuration #Alternatively, start the module with
yast2 online_update_configurationfrom the command line.Choose the update interval: , , or .
Sometimes patches may require the attention of the administrator, for example when restarting critical services. For example, this might be an update for Docker Open Source Engine that requires all containers to be restarted. Before these patches are installed, the user is informed about the consequences and is asked to confirm the installation of the patch. Such patches are called “Interactive Patches”.
When installing patches automatically, it is assumed that you have accepted the installation of interactive patches. If you prefer to review these patches before they get installed, check . In this case, interactive patches will be skipped during automated patching. Make sure to periodically run a manual online update, to check whether interactive patches are waiting to be installed.
To automatically accept any license agreements, activate .
To automatically install all packages recommended by updated packages, activate .
To disable the use of delta RPMs (for performance reasons), un-check .
To filter the patches by category (such as security or recommended), check and add the appropriate patch categories from the list. Only patches of the selected categories will be installed. It is a good practice to enable only automatic updates, and to manually review all others. Patching is normally reliable, but you may wish to test non-security patches, and roll them back if you encounter any problems.
supply patches for package management and YaST features and modules.
patches provide crucial updates and bugfixes.
patches are optional bugfixes and enhancements.
are new packages.
is equivalent to miscellaneous.
is unused.
Confirm your configuration by clicking .
The automatic online update does not automatically restart the system afterward. If there are package updates that require a system reboot, you need to do this manually.