16 Spectre/Meltdown checker #
spectre-meltdown-checker is a shell script to test if
your system is vulnerable to the several speculative execution
vulnerabilities that are in nearly all CPUs manufactured in the
past 20 years. This is a hardware flaw that potentially allows an attacker
to read all data on the system. On cloud computing services, where multiple
virtual machines are on a single physical host, an attacker can gain access
to all virtual machines. Fixing these vulnerabilities requires redesigning
and replacing CPUs. Until this happens, there are several software patches
that mitigate these vulnerabilities. If you have kept your SUSE systems
updated, all of these patches should already be installed.
spectre-meltdown-checker generates a detailed report. It
is impossible to guarantee that your system is secure, but it shows you
which mitigations are in place, and potential vulnerabilities.
16.1 Using spectre-meltdown-checker #
Install the script, and then run it as root without any options:
#zypper in spectre-meltdown-checker#spectre-meltdown-checker.sh
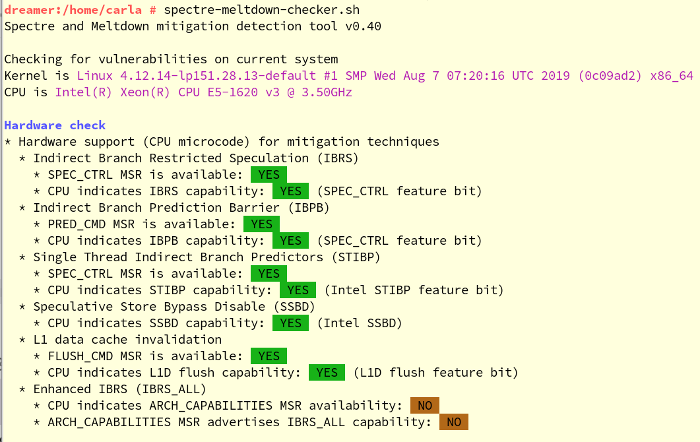
You will see colorful output like Figure 16.1, “Output from spectre-meltdown-checker”:
spectre-meltdown-checker.sh --help lists all options. It
is useful to pipe plain text output, with no colors, to a file:
# spectre-meltdown-checker.sh --no-color| tee filename.txt
The previous examples are on a running system, which is the default. You may
also run spectre-meltdown-checker offline by specifying
the paths to the kernel, config, and System.map files:
#cd /boot#spectre-meltdown-checker.sh \ --no-color \ --kernel vmlinuz-4.12.14-lp151.28.13-default \ --config config-4.12.14-lp151.28.13-default \ --map System.map-4.12.14-lp151.28.13-default| tee filename.txt
Other useful options are:
- --verbose, -v
Increase verbosity; repeat for more verbosity, for example
-v -v -v- --explain
Print human-readable explanations
- --batch [short] [json] [nrpe] [prometheus]
Format output in various machine-readable formats
spectre-meltdown-checker.sh --disclaimer provides
important information about what the script does, and does not do.
16.2 More information #
For more information, see the following references:
SUSE Knowledge Base article #7022937, Security Vulnerability: Spectre Variant 4 (Speculative Store Bypass) aka CVE-2018-3639: https://www.suse.com/support/kb/doc/?id=7022937
speed47/spectre-meltdown-checker source code on GitHub, with detailed references to relevant Common Vulnerabilities and Exposures (CVE): https://github.com/speed47/spectre-meltdown-checker
SUSE Blog article, Meltdown and Spectre Performance: https://www.suse.com/c/meltdown-spectre-performance/
SUSE Knowledge Base article #7022512, providing information on architectures, CVEs, and mitigations: https://www.suse.com/support/kb/doc/?id=7022512