16 Enhancing virtual machine security with AMD SEV-SNP #
You can enhance the security of your virtual machines with AMD Secure Encrypted Virtualization-Secure Nested Paging (SEV-SNP). The AMD SEV-SNP feature isolates virtual machines from the host system and other VMs, protecting the data and code. This feature encrypts data and ensures that all changes with the code and data in the VM are detected or tracked. Since this isolates VMs, the other VMs or the host machine are not affected with threats.
This section explains the steps to enable and use AMD SEV-SNP on your AMD EPYC server with SUSE Linux Enterprise Server 15 SP6.
This feature is shipped as a technology preview in SUSE Linux Enterprise Server 15 SP6. The necessary packages are not part of the default installation or repositories. These packages are shipped via a confidential compute module.
16.1 Supported hardware #
A system with an AMD EPYC (3rd Gen or newer) is required to run AMD SEV-SNP virtual machines. The BIOS of the AMD machine must provide the necessary options to enable support for confidential computing on the platform.
16.2 Enabling confidential compute module #
The necessary packages for AMD SEV-SNP feature are shipped via a confidential compute module. You must enable it at system installation time or later via the SUSEConnect command-line tool.
To check whether the module is already enabled, run the command:
>sudosuseconnect -lThis displays the list of available modules with their activation status and commands to enable the inactive modules.
The inactive confidential compute module appears as given below:
Confidential Computing Technical Preview Module 15 SP6 x86_64 Activate with: suseconnect -p sle-module-confidential-computing/15.6/x86_64
To enable the confidential computing module technology preview, run the command:
>sudosuseconnect -p sle-module-confidential-computing/15.6/x86_64Registering system to SUSE Customer Center Updating system details on https://scc.suse.com ... Activating sle-module-confidential-computing 15.6 x86_64 ... Adding service to system ... Installing release package ... Successfully registered systemThe confidential compute module is enabled and you can install the packages.
16.3 Installing packages and setting up the base system #
The confidential compute module provides replacement packages supporting AMD SEV-SNP. To ensure a maximum of compatibility, these packages are based on the code streams from SUSE Linux Enterprise Server 15 SP6.
The three components that need to be replaced are:
The Linux kernel
QEMU Virtual Machine Monitor
libvirtframework
To install the replacement packages, run the command:
>sudozypper install --from SLE-Module-Confidential-Computing-15-SP6-Pool --from SLE-Module-Confidential-Computing-15-SP6-Updates qemu-ovmf-x86_64 libvirt kernel-cocoAfter replacing the packages, you must set up the system with a configuration change to make the AMD SEV-SNP feature ready to use. The IOMMU on the host side must be configured in non-passthrough mode. This is required to prevent peripheral devices from writing to memory that belongs to an encrypted guest and destroying its data integrity. The default IOMMU configuration in SUSE Linux Enterprise Server 15 SP6 is
passthroughmode.To disable the IOMMU configuration in SUSE Linux Enterprise Server 15 SP6, open the
/etc/default/grubfile and addiommu=noptto theGRUB_CMDLINE_LINUX_DEFAULTvariable.To update the bootloader configuration, run the command:
>sudo;update-bootloaderThe system is now ready to be restarted with the confidential computing kernel. It is not selected as the default kernel in the bootloader, so ensure to select it in the boot menu.
16.4 Verifying setup #
You can verify the installation and configuration of the packages.
To verify whether the system has started with the new kernel, check the response for the command
uname -r.>sudouname -r6.4.0-150616.coco15sp6-cocoEnsure that the kernel version displayed contains the coco tag.
To check the initialization result of the AMD Secure Processor in the kernel log when the kernel is running, run the command:
>sudodmesg | grep -i ccp[ 10.103166] ccp 0000:42:00.1: enabling device (0000 -> 0002) [ 10.114951] ccp 0000:42:00.1: no command queues available [ 10.127137] ccp 0000:42:00.1: sev enabled [ 10.133152] ccp 0000:42:00.1: psp enabled [ 10.240817] ccp 0000:42:00.1: SEV firmware update successful [ 11.128307] ccp 0000:42:00.1: SEV API:1.55 build:8 [ 11.135057] ccp 0000:42:00.1: SEV-SNP API:1.55 build:8The message about the SEV-SNP API version indicates the successful initialization of the AMD Secure Processor. Sometimes it happens that these messages do not appear in the kernel log. In this case the BIOS settings or the IOMMU configuration are often the root-cause.
16.5 Launching an AMD SEV-SNP virtual machine #
You can run AMD SEV-SNP protected virtual machines using the libvirt framework once the confidential computing kernel is booted and the AMD Secure Processor is initialized.
libvirt has several ways of setting up new virtual machines. This document uses a prepared disk image and the virt-manager graphical user interface.
Connect virt-manager to the AMD EPYC host and create a new virtual machine.
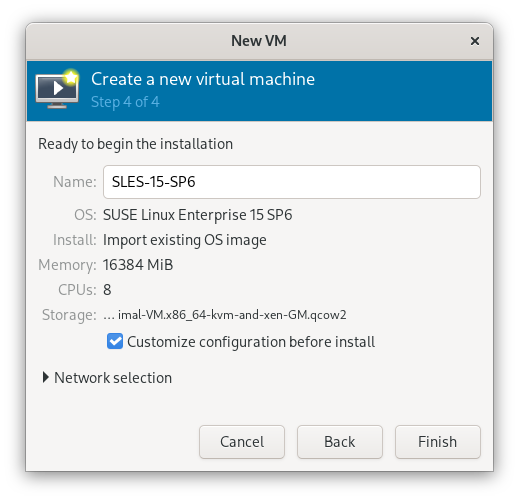
In the Create a new virtual machine window, select the details:
Select how you want to install the operating system.
Select the ISO or CDROM install media.
Select the memory and CPU settings.
Select the required storage details.
In the fifth step, verify the details and select Customize configuration before install.
Figure 16.1: Create Virtual Machine #Click Finish.
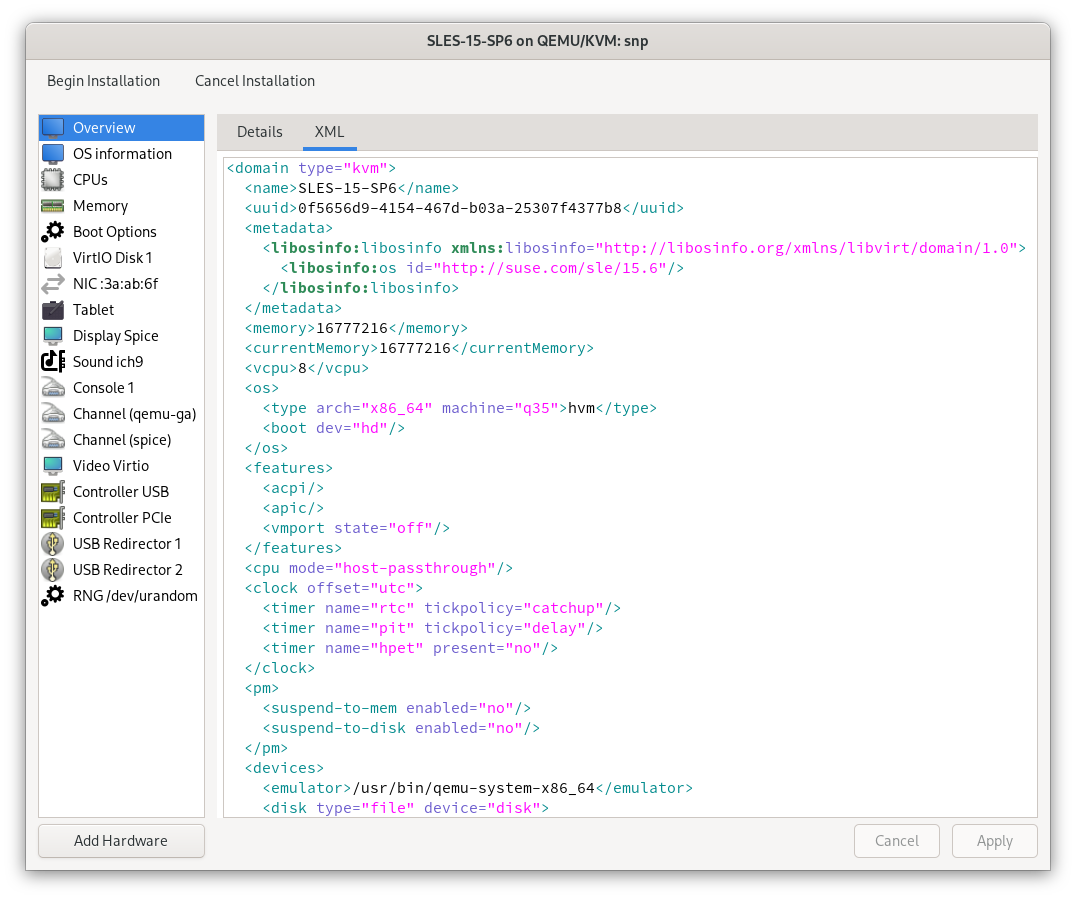
Select the XML tab in the virtual machine configuration window.
In the XML tab, you can edit the XML configuration of the virtual machine used by the
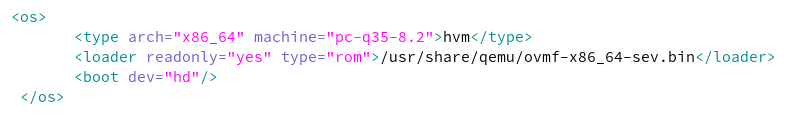
libvirtback-end.Figure 16.2: view of virtual machine configuration #To protect the virtual machine with AMD SEV-SNP, set the correct firmware by modifying the
ossection as given below:Figure 16.3: Set firmware #The
loaderline sets the firmware to the SEV version of OVMF.Add a
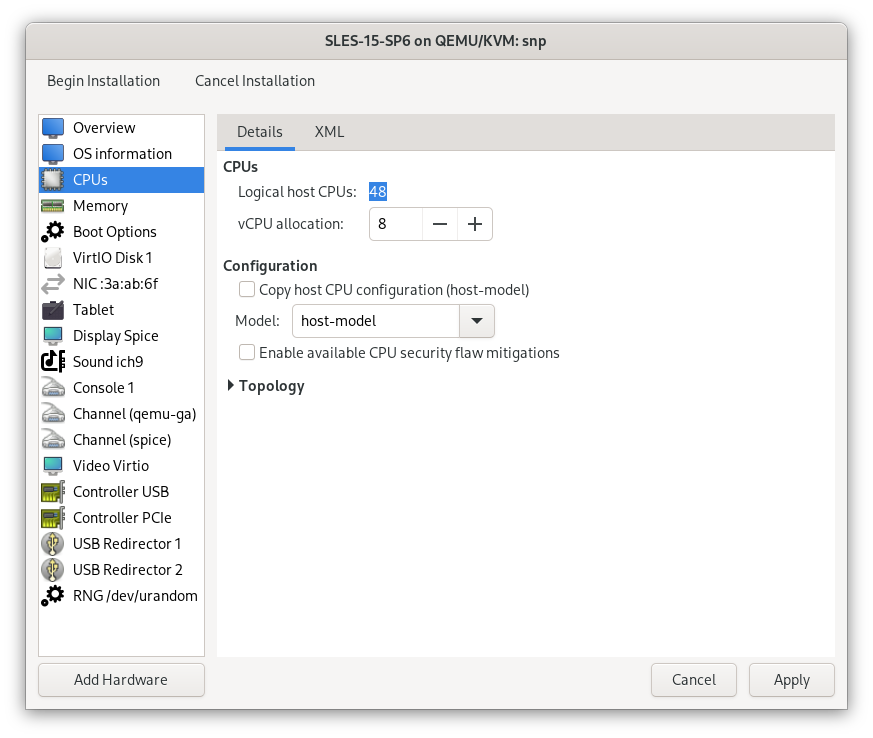
launchSecuritysection. For AMD SEV-SNP, the section looks like this:Figure 16.4: launchSecurity #Click Apply and then click the Details tab.
Select CPUs in the left-hand list and set the CPU Model to
host-model:Figure 16.5: The view of virtual machine configuration #Click Apply and click Begin Installation.
This starts the virtual machine and installs it according to your settings. The virtual machine boots up once the process is complete, and you can verify the AMD SEV-SNP protection.
16.6 Verifying the AMD SEV-SNP virtual machine #
From the appearance of the virtual machine, one cannot tell whether it runs in a confidential computing environment. But there are several ways to verify that from within the virtual machine.
To check the kernel log, run the command:
>sudodmesg | grep -i sev-snp[ 1.986186] Memory Encryption Features active: AMD SEV SEV-ES SEV-SNP
The presence of the SEV-SNP feature in the kernel log, among other active memory encryption features, shows that it is active for the virtual machine.
There are also cryptographically secure ways to prove the security of the AMD SEV-SNP environment.