1 Air-gapped environments #
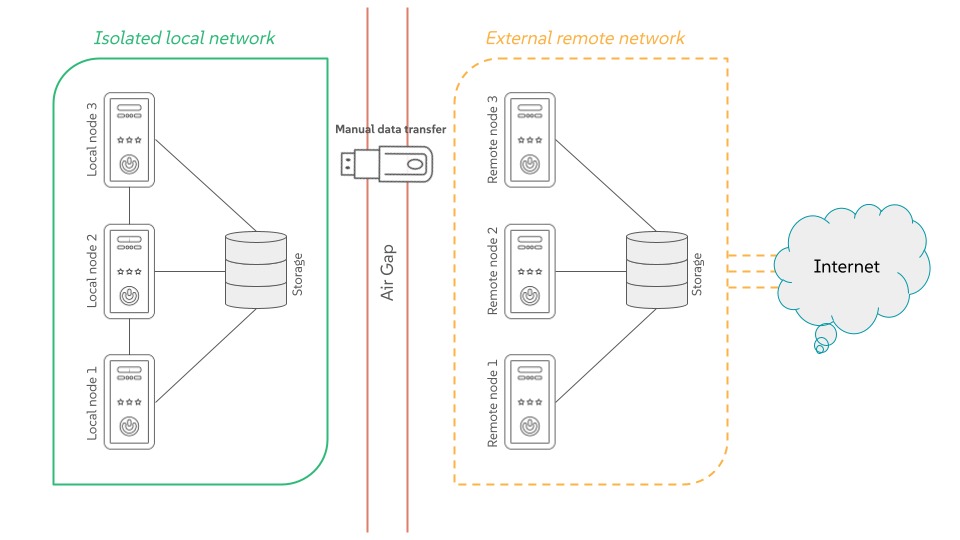
An air-gapped environment is a security measure where a single host or the whole network is isolated from all other networks, such as the public Internet. This "air gap" acts as a physical or logical barrier, preventing any direct connection that could be exploited by cyber threats.
1.1 Why you need an air-gapped environment? #
The primary goal is to protect highly sensitive data and critical systems from unauthorized access, cyber attacks, malware and ransomware. Air-gapped environments are typically found in situations where security is of the utmost importance, such as:
Military and government networks handling classified information.
Industrial control systems (ICS) for critical infrastructure like power plants and water treatment facilities.
Financial institutions and stock exchanges.
Systems controlling nuclear power plants or other life-critical operations.
1.2 How do air-gapped environments work? #
There are two types of air gaps:
- Physical air gaps
This is the most secure method, where the system is disconnected from any network. It might even involve placing the system in a shielded room.
- Logical air gaps
This type uses software controls such as firewall rules and network segmentation to create a highly restricted connection. While it offers more convenience, it is not as secure as a physical air gap because the air-gapped system is still technically connected to a network.
1.3 What challenges do air-gapped environments face? #
When working in air-gapped systems, you usually face the following limitations:
- Manual updates
Air-gapped systems cannot automatically receive software or security updates from external networks. You must manually download and install updates, which can be time-consuming and create vulnerabilities if not done regularly.
- Insider threats and physical attacks
An air gap does not protect against threats that gain physical access to the system, such as a malicious insider with a compromised USB drive.
- Limited functionality
The lack of connectivity limits the system’s ability to communicate with other devices or services, making it less efficient for many modern applications.