24 Configuring a VPN server #
Internet connections are easily available and affordable. However, not all connections are secure. Using a Virtual Private Network (VPN), you can create a secure network within an insecure network such as the Internet or Wi-Fi. It can be implemented in different ways and serves several purposes. In this chapter, we focus on the OpenVPN implementation to link branch offices via secure wide area networks (WANs).
24.1 Conceptual overview #
This section defines some terms regarding VPN and gives a brief overview of some scenarios.
24.1.1 Terminology #
- Endpoint
The two “ends” of a tunnel, the source or destination client.
- Tap device
A tap device simulates an Ethernet device (layer 2 packets in the OSI model, such as Ethernet frames). A tap device is used for creating a network bridge. It works with Ethernet frames.
- Tun device
A tun device simulates a point-to-point network (layer 3 packets in the OSI model, such as IP packets). A tun device is used with routing and works with IP frames.
- Tunnel
Linking two locations through a primarily public network. From a more technical viewpoint, it is a connection between the client's device and the server's device. A tunnel is encrypted, but it does need to be by definition.
24.1.2 VPN scenarios #
Whenever you set up a VPN connection, your IP packets are transferred over a secured tunnel. A tunnel can use either a tun or tap device. They are virtual network kernel drivers which implement the transmission of Ethernet frames or IP frames/packets.
Any user space program, such as OpenVPN, can attach itself to a tun or tap device to receive packets sent by your operating system. The program is also able to write packets to the device.
There are many solutions to set up and build a VPN connection. This section focuses on the OpenVPN package. Compared to other VPN software, OpenVPN can be operated in two modes:
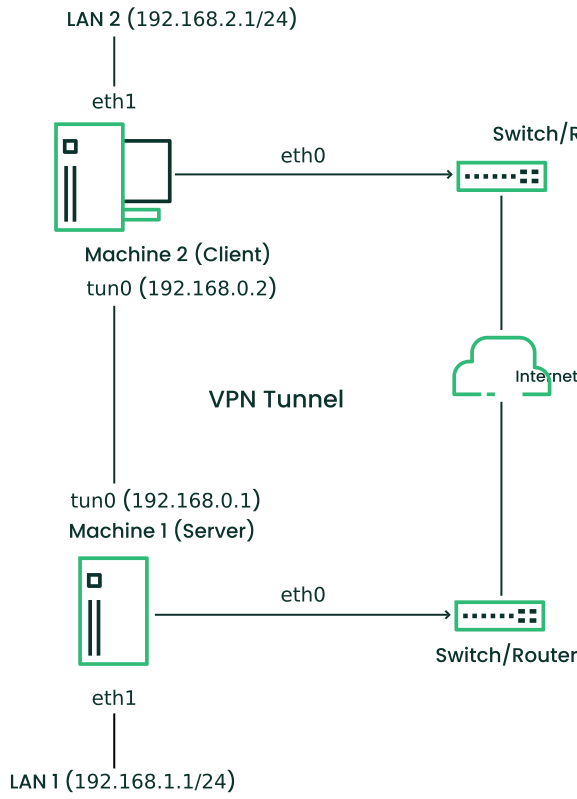
- Routed VPN
Routing is an easy solution to set up. It is more efficient and scales better than a bridged VPN. Furthermore, it allows the user to tune MTU (Maximum Transfer Unit) to raise efficiency. However, in a heterogeneous environment, if you do not have a Samba server on the gateway, NetBIOS broadcasts do not work. If you need IPv6, the drivers for the tun devices on both ends must support this protocol explicitly. This scenario is depicted in Figure 24.1, “Routed VPN”.
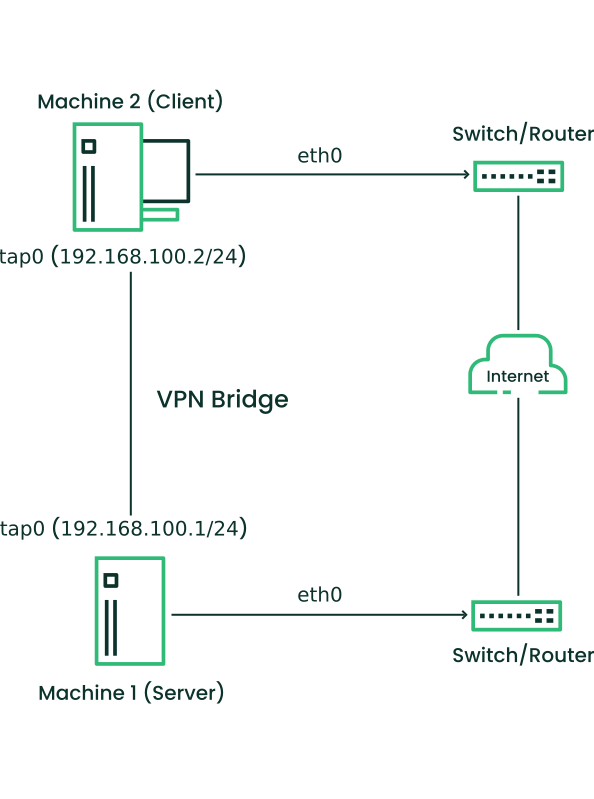
Figure 24.1: Routed VPN #- Bridged VPN
Bridging is a more complex solution. It is recommended when you need to browse Windows file shares across the VPN without setting up a Samba or WINS server. Bridged VPN uses network TAP devices, that simulate a link layer between the VPN endpoints and operate in layer 2 carrying Ethernet frames. This makes it possible to use non-IP protocols (such as IPX) or applications relying on network broadcasts. However, it is less efficient than routed VPN. Another disadvantage is that it does not scale well. This scenario is depicted in the following figures.
- Scenario 1
The TAP devices are only available on the VPN endpoints themselves. Layer 2 VPN traffic comes only directly from the Server (Machine 1) side or the Client (Machine 2).
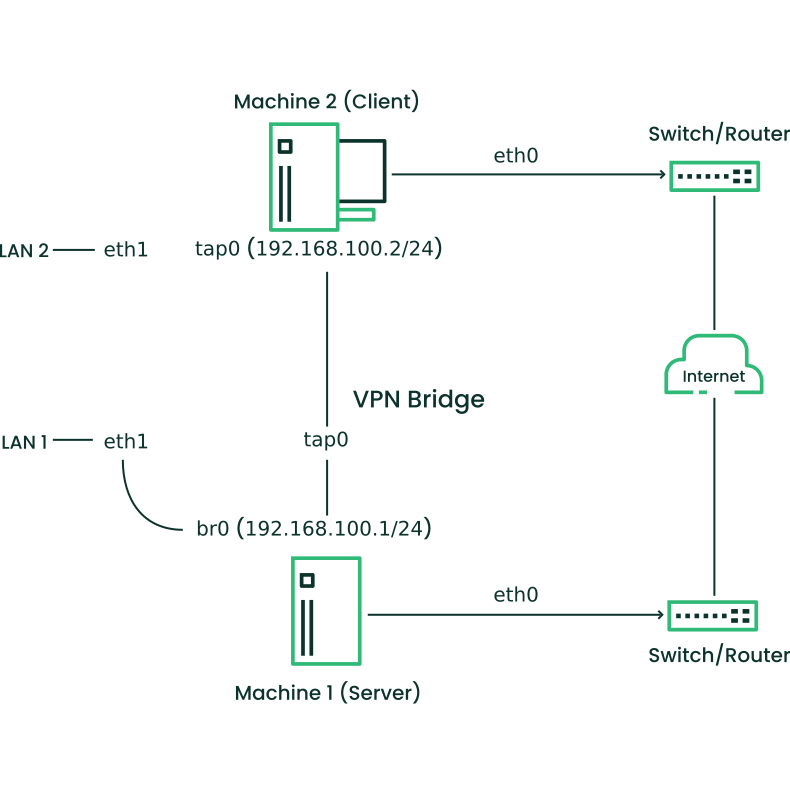
- Scenario 2
The TAP device
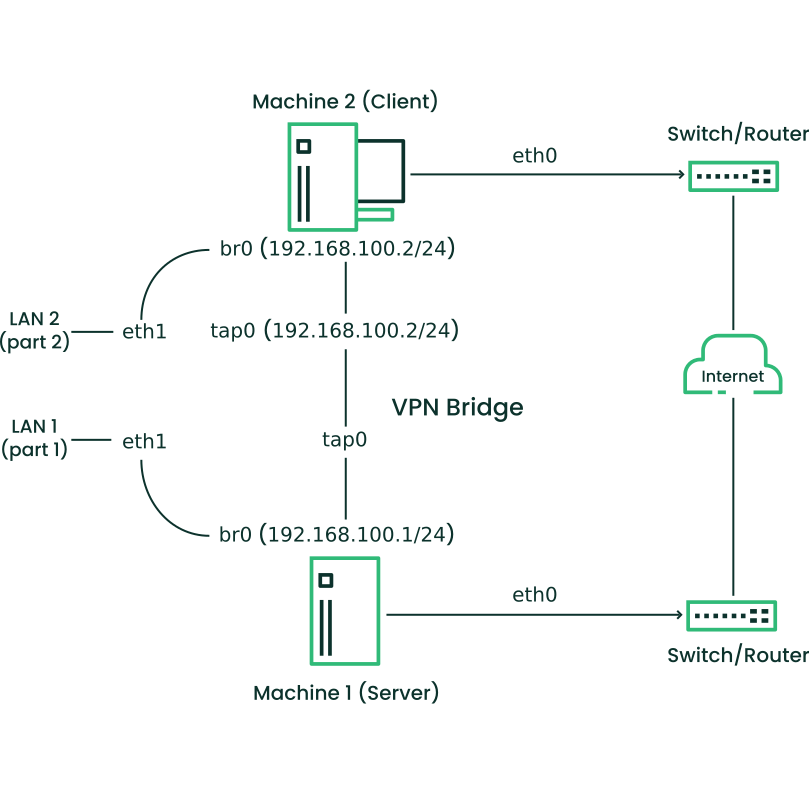
tap0on the Server (Machine 1) side is bridged to theeth1network interface connected to LAN 1. Layer 2 traffic reachingtap0via the bridgebr0will be forwarded via the VPN bridge to the Client (Machine 2) system.- Scenario 3
On both sides, the Server (Machine 1) and Client (Machine 2), the TAP device
tap0is bridged to a local network interfaceeth1. Layer 2 traffic from the client network LAN 2 will be forwarded to the server network LAN 1 and vice versa.
Figure 24.2: Bridged VPN - scenario 1 #Figure 24.3: Bridged VPN - scenario 2 #Figure 24.4: Bridged VPN - scenario 3 #
The major difference between bridging and routing is that a routed VPN cannot IP-broadcast while a bridged VPN can.
24.2 Setting up a simple test scenario #
In the following example, we create a point-to-point VPN tunnel. The
example demonstrates how to create a VPN tunnel between one client and a
server. It is assumed that your VPN server uses private IP addresses
like IP_OF_SERVER
and your client uses the IP address
IP_OF_CLIENT.
Make sure you select addresses which do not conflict with other IP addresses.
This following scenario is provided as an example meant for familiarizing yourself with VPN technology. Do not use this as a real world scenario, as it can compromise the security and safety of your IT infrastructure.
To simplify working with OpenVPN configuration files, we recommend the following:
Place your OpenVPN configuration files in the directory
/etc/openvpn.Name your configuration files
MY_CONFIGURATION.conf.If there are multiple files that belong to the same configuration, place them in a subdirectory like
/etc/openvpn/MY_CONFIGURATION.
24.2.1 Configuring the VPN server #
To configure a VPN server, proceed as follows:
Install the package
openvpnon the machine that later becomes your VPN server.Open a shell, become
rootand create the VPN secret key:#openvpn --genkey secret /etc/openvpn/secret.keyCopy the secret key to your client:
#scp /etc/openvpn/secret.key root@IP_OF_CLIENT:/etc/openvpn/Create the file
/etc/openvpn/server.confwith the following content:dev tun ifconfig IP_OF_SERVER IP_OF_CLIENT secret secret.key
Set up a tun device configuration by creating a file called
/etc/sysconfig/network/ifcfg-tun0with the following content:STARTMODE='manual' BOOTPROTO='static' TUNNEL='tun' TUNNEL_SET_OWNER='nobody' TUNNEL_SET_GROUP='nobody' LINK_REQUIRED=no PRE_UP_SCRIPT='systemd:openvpn@server' PRE_DOWN_SCRIPT='systemd:openvpn@service'
The notation
openvpn@serverpoints to the OpenVPN server configuration file located at/etc/openvpn/server.conf. For more information, see/usr/share/doc/packages/openvpn/README.SUSE.If you use a firewall, start YaST and open UDP port 1194 ( › › ).
Start the OpenVPN server service by setting the tun device to
up:>sudowicked ifup tun0You should see the confirmation:
tun0 up
24.2.2 Configuring the VPN clients #
To configure the VPN client, do the following:
Install the package
openvpnon your client VPN machine.Create
/etc/openvpn/client.confwith the following content:remote DOMAIN_OR_PUBLIC_IP_OF_SERVER dev tun ifconfig IP_OF_CLIENT IP_OF_SERVER secret secret.key
Replace the placeholder IP_OF_CLIENT in the first line with either the domain name, or the public IP address of your server.
Set up a tun device configuration by creating a file called
/etc/sysconfig/network/ifcfg-tun0with the following content:STARTMODE='manual' BOOTPROTO='static' TUNNEL='tun' TUNNEL_SET_OWNER='nobody' TUNNEL_SET_GROUP='nobody' LINK_REQUIRED=no PRE_UP_SCRIPT='systemd:openvpn@client' PRE_DOWN_SCRIPT='systemd:openvpn@client'
If you use a firewall, start YaST and open UDP port 1194 as described in Step 6 of Procedure 24.1, “VPN server configuration”.
Start the OpenVPN server service by setting the tun device to
up:>sudowicked ifup tun0You should see the confirmation:
tun0 up
24.2.3 Testing the VPN example scenario #
After OpenVPN has successfully started, test the availability of the tun device with the following command:
ip addr show tun0
To verify the VPN connection, use ping on both client
and server side to see if they can reach each other. Ping the server
from the client:
ping -I tun0 IP_OF_SERVER
Ping the client from the server:
ping -I tun0 IP_OF_CLIENT
24.3 Setting up your VPN server using a certificate authority #
The example in Section 24.2 is useful for testing, but not for daily work. This section explains how to build a VPN server that allows more than one connection at the same time. This is done with a public key infrastructure (PKI). A PKI consists of a pair of public and private keys for the server and each client, and a certificate authority (CA), which is used to sign every server and client certificate.
This setup involves the following basic steps:
24.3.1 Creating certificates #
Before a VPN connection can be established, the client must authenticate the server certificate. Conversely, the server must also authenticate the client certificate. This is called mutual authentication.
Creating certificates is not supported on SUSE Linux Enterprise Server. The following assumes you have created a CA certificate, a server certificate, and a client certificate on another system.
The server certificate is required in the PEM and unencrypted
key in PEM formats. Copy the PEM version to
/etc/openvpn/server_crt.pem on the VPN server. The
unencrypted version needs to go to
/etc/openvpn/server_key.pem.
Client certificates need to be of the format PKCS12 (preferred) or PEM. The
certificate in PKCS12 format needs to contain the CA chain and needs to be
copied to
/etc/openvpn/CLIENT.p12. In
case you have client certificates in PEM format containing the CA chain,
copy them to
/etc/openvpn/CLIENT.pem. In
case you have split the PEM certificates into client certificate
(*.ca), client key (*.key), and
the CA certificate (*.ca), copy these files to
/etc/openvpn/ on each client.
The CA certificate needs to be copied to
/etc/openvpn/vpn_ca.pem on the server and each client.
If you split client certificates into client certificate, client key, and the CA certificate, you need to provide the respective file names in the OpenVPN configuration file on the respective clients (see Example 24.1, “VPN server configuration file”).
24.3.2 Configuring the VPN server #
As the basis of your configuration file, copy
/usr/share/doc/packages/openvpn/sample-config-files/server.conf
to /etc/openvpn/. Then customize it to your needs.
# /etc/openvpn/server.conf port 1194 1 proto udp 2 dev tun0 3 # Security 4 ca vpn_ca.pem cert server_crt.pem key server_key.pem # ns-cert-type server remote-cert-tls client 5 dh server/dh2048.pem 6 server 192.168.1.0 255.255.255.0 7 ifconfig-pool-persist /var/run/openvpn/ipp.txt 8 # Privileges 9 user nobody group nobody # Other configuration 10 keepalive 10 120 comp-lzo persist-key persist-tun # status /var/log/openvpn-status.tun0.log 11 # log-append /var/log/openvpn-server.log 12 verb 4
The TCP/UDP port on which OpenVPN listens. You need to open the port in the firewall, see Chapter 23, Masquerading and firewalls. The standard port for VPN is 1194, so you can leave that as it is. | |
The protocol, either UDP or TCP. | |
The tun or tap device. For the difference between these, see Section 24.1.1, “Terminology”. | |
The following lines contain the relative or absolute path to the root
server CA certificate ( | |
Require that peer certificates have been signed with an explicit key usage and extended key usage based on RFC3280 TLS rules. | |
The Diffie-Hellman parameters. Create the required file with the following command: openssl dhparam -out /etc/openvpn/dh2048.pem 2048 | |
Supplies a VPN subnet. The server can be reached by
| |
Records a mapping of clients and its virtual IP address in the given file. Useful when the server goes down and (after the restart) the clients get their previously assigned IP address. | |
For security reasons, run the OpenVPN daemon with reduced privileges. To
do so, specify that it should use the group and user
| |
Several configuration options—see the comment in the
example configuration file:
| |
Enable this option to write short status updates with statistical data (“operational status dump”) to the named file. By default, this is not enabled.
All output is written to the system journal, which can be displayed with
| |
By default, log messages go to syslog. Overwrite this behavior by
removing the hash character. In that case, all messages go to
|
After having completed this configuration, you can see log messages of
your OpenVPN server under /var/log/openvpn.log.
After having started it for the first time, it should finish with:
... Initialization Sequence Completed
If you do not see this message, check the log carefully for any hints of what is wrong in your configuration file.
24.3.3 Configuring the VPN clients #
As the basis of your configuration file, copy
/usr/share/doc/packages/openvpn/sample-config-files/client.conf
to /etc/openvpn/. Then customize it to your needs.
# /etc/openvpn/client.conf client 1 dev tun 2 proto udp 3 remote IP_OR_HOST_NAME 1194 4 resolv-retry infinite nobind remote-cert-tls server 5 # Privileges 6 user nobody group nobody # Try to preserve some state across restarts. persist-key persist-tun # Security 7 pkcs12 client1.p12 comp-lzo 8
Specifies that this machine is a client. | |
The network device. Both clients and server must use the same device. | |
The protocol. Use the same settings as on the server. | |
This is security option for clients which ensures that the host they connect to is a designated server. | |
Replace the placeholder IP_OR_HOST_NAME
with the respective host name or IP address of your VPN server. After
the host name, the port of the server is given. You can have multiple
lines of | |
For security reasons, run the OpenVPN daemon with reduced privileges. To
do so, specify that it should use the group and user
| |
Contains the client files. For security reasons, use a separate pair of files for each client. | |
Turn on compression. Only use this parameter if compression is enabled on the server as well. |
24.4 Setting up a VPN server or client using YaST #
You can also use YaST to set up a VPN server. However, the YaST module does not support OpenVPN. Instead, it provides support for the IPsec protocol (as implemented in the software StrongSwan). Like OpenVPN, IPsec is a widely supported VPN scheme.
To start the YaST VPN module, select › .
Under , activate .
To create a new VPN, click , then enter a name for the connection.
Under , select .
Then choose the scenario:
The scenarios and are best suited to Linux client setups.
The scenario sets up a configuration that is natively supported by modern versions of Android, iOS, and macOS. It is based on a pre-shared key setup with an additional user name and password authentication.
The scenario is a configuration that is natively supported by Windows and BlackBerry devices. It is based on a certificate setup with an additional user name and password authentication.
For this example, choose .
To specify the key, click . Activate , then type the secret key. Confirm with .
Choose whether and how to limit access within your VPN under . To enable only certain IP ranges, specify these in CIDR format, separated by commas in . For more information about the CIDR format, see https://en.wikipedia.org/wiki/Classless_Inter-Domain_Routing.
Under , specify the format of IP addresses your VPN should provide to its clients.
To finish, click . The YaST VPN module automatically adds and enables firewall rules to allow clients to connect to the new VPN.
To view the connection status, in the following confirmation window, click . You can see the output of
systemctl statusfor your VPN, which allows you to check if the VPN is running and configured correctly.
24.5 More information #
For more information about VPN, see:
https://openvpn.net: the OpenVPN home page
manopenvpn/usr/share/doc/packages/openvpn/sample-config-files/: example configuration files for different scenarios./usr/src/linux/Documentation/networking/tuntap.txt, to install thekernel-sourcepackage.