Confidential Computing
Confidential Computing is a technology which allows protection of data in use by using hardware-based Trusted Execution Environment (TEE), the type of environments that provide increased level of security for data integrity, data confidentiality, and code integrity.
1. Confidential Computing with SUSE Manager
The trustworthiness of the TEE is checked with the attestation process. SUSE Manager can be used as an attestation server for the systems registered to it. It generates a report page for the systems which run in this mode. These systems need to be attested and checked on regular base. The history of the past checks is also stored and available per request.
Confidential Computing Attestation depends on the used hardware and environment where the attested systems are running on.
|
Confidential Computing Attestation is only available on x86_64 architecture. |
2. Requirements
Confidential Computing can be set up in an environment with the following characteristics:
-
Attested system (virtual machine) is SLES15 SP6 and bootstrapped to SUSE Manager
-
Hardware must have
AMD EPYC Milan CPUorAMD EPYC Genoa CPU -
BIOS must be configured to allow Confidential Computing attestation
-
Host OS and the virtualization software (KVM and libvirt) must support Confidential Computing.
3. Limitations
-
SLES15 SP6 has Confidential Computing attestation as technology preview.
-
SUSE Manager has Confidential Computing attestation as technology preview.
-
Secure boot is attested. However, currently KVM secure boot and SNP Guest are not working together.
4. Use Confidential Computing in SUSE Manager
|
For the exact steps for setting up and configuring Confidential Computing on your host, refer to the OS Vendor documentation. |
-
The attestation container is enabled during the installation of SUSE Manager with
mgradm install podman. -
Add the following to file
mgradm.yaml.coco: replicas: 1
-
To enable the attestation container after the installation, use the command line parameter
mgradm. -
Run the command
mgradm scale uyuni-server-attestation --replicas 1
-
To disable the already enabled attestation container, run the command:
mgradm scale uyuni-server-attestation --replicas 0
-
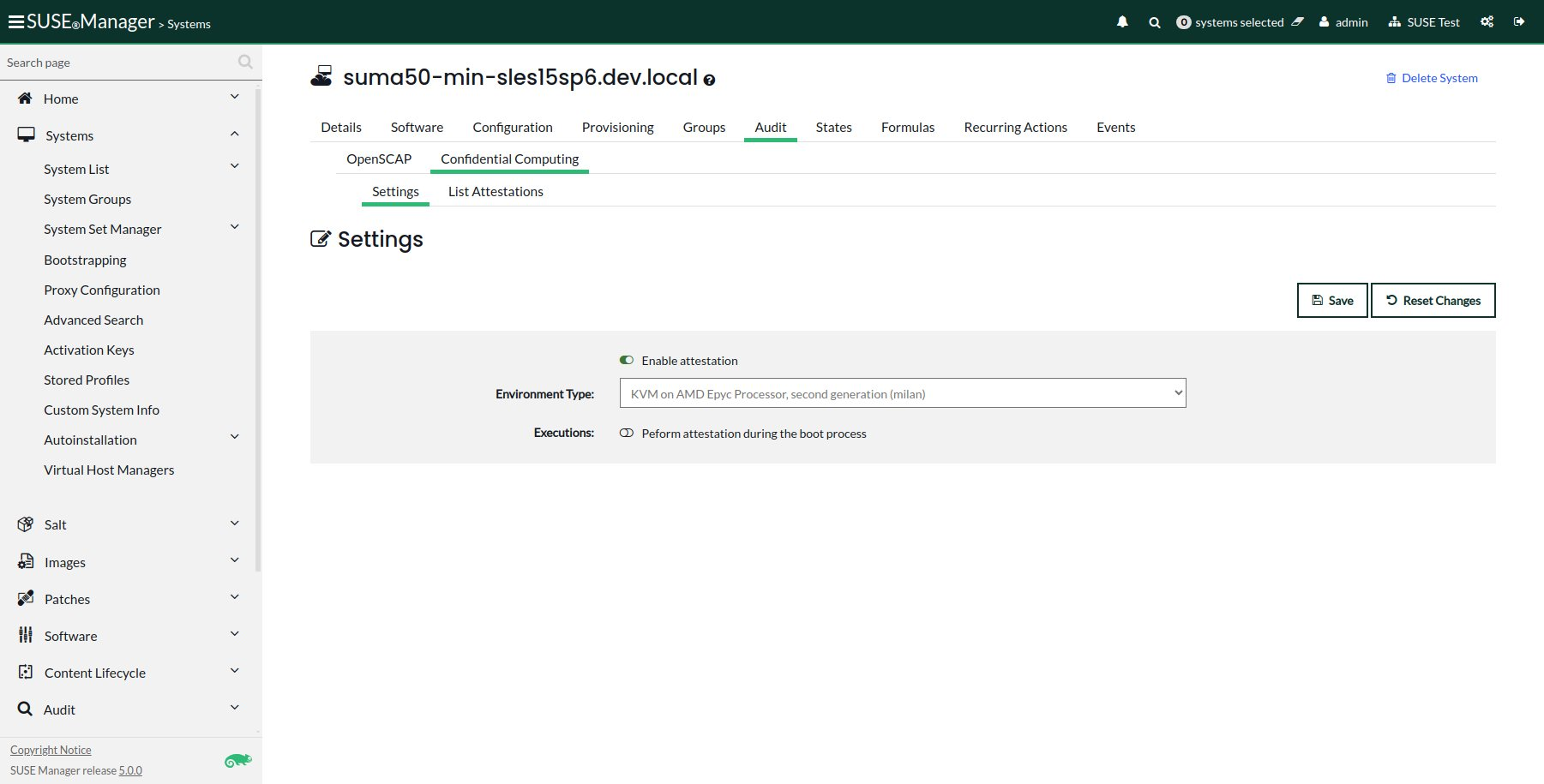
For the selected system, go to tab .
-
Enable the attestation by selecting the toggle button.
-
In the field
Environment Typeselect the correct option from the drop-down list. -
Click button Save to save the changes.
-
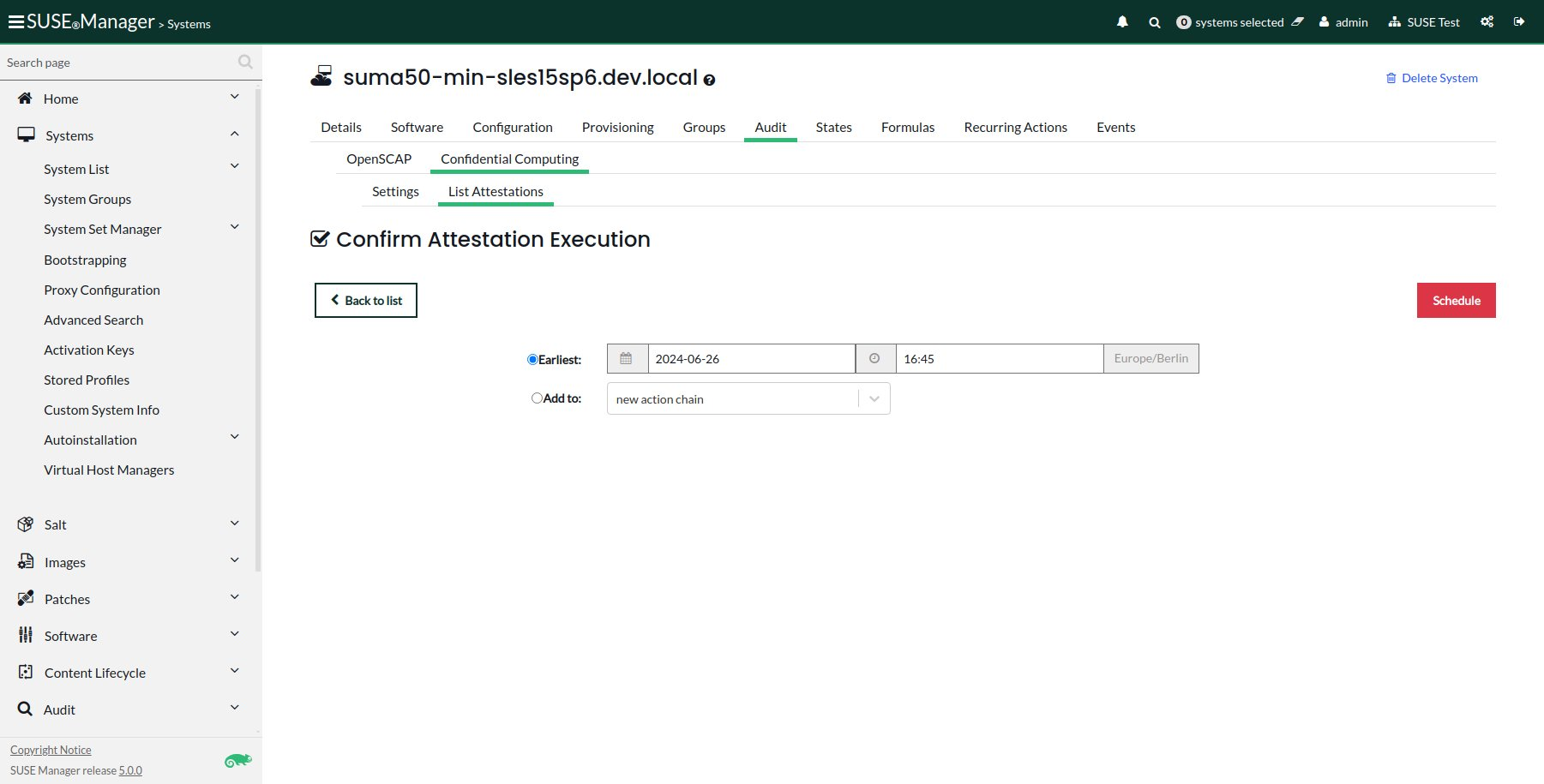
For the selected system, go to tab .
-
Click Schedule Attestation. The new form opens.
-
In the field
Earliestselect the time of running the attestation. -
If needed, add the newly created attestation to the action chain by selecting
Add tooption. -
Click button Schedule to save and schedule the new attestation execution.
-
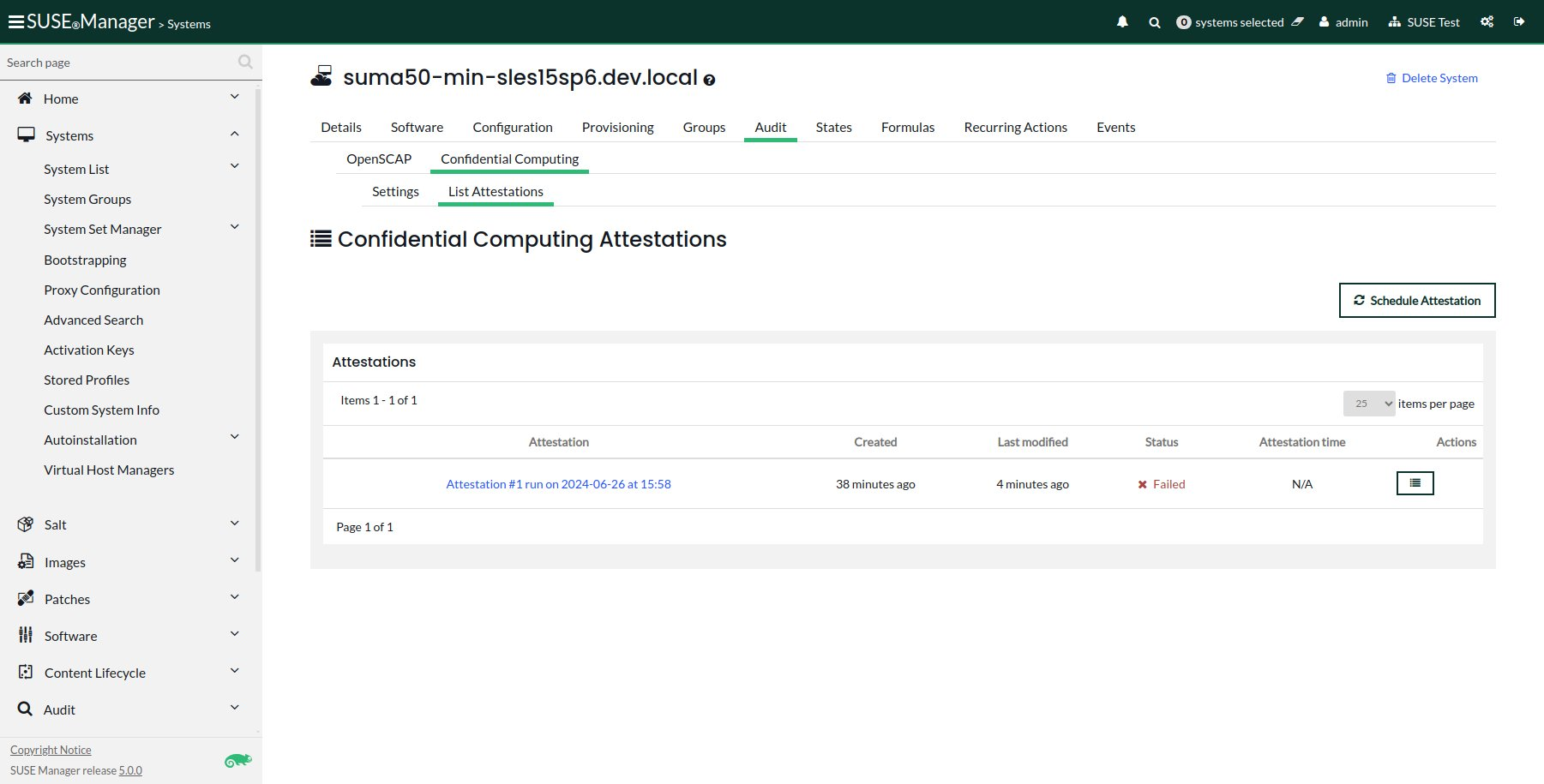
For the selected system, go to tab .
-
Find and select the report you want to view.
-
After clicking the selected attestation report tab
Overviewwill open.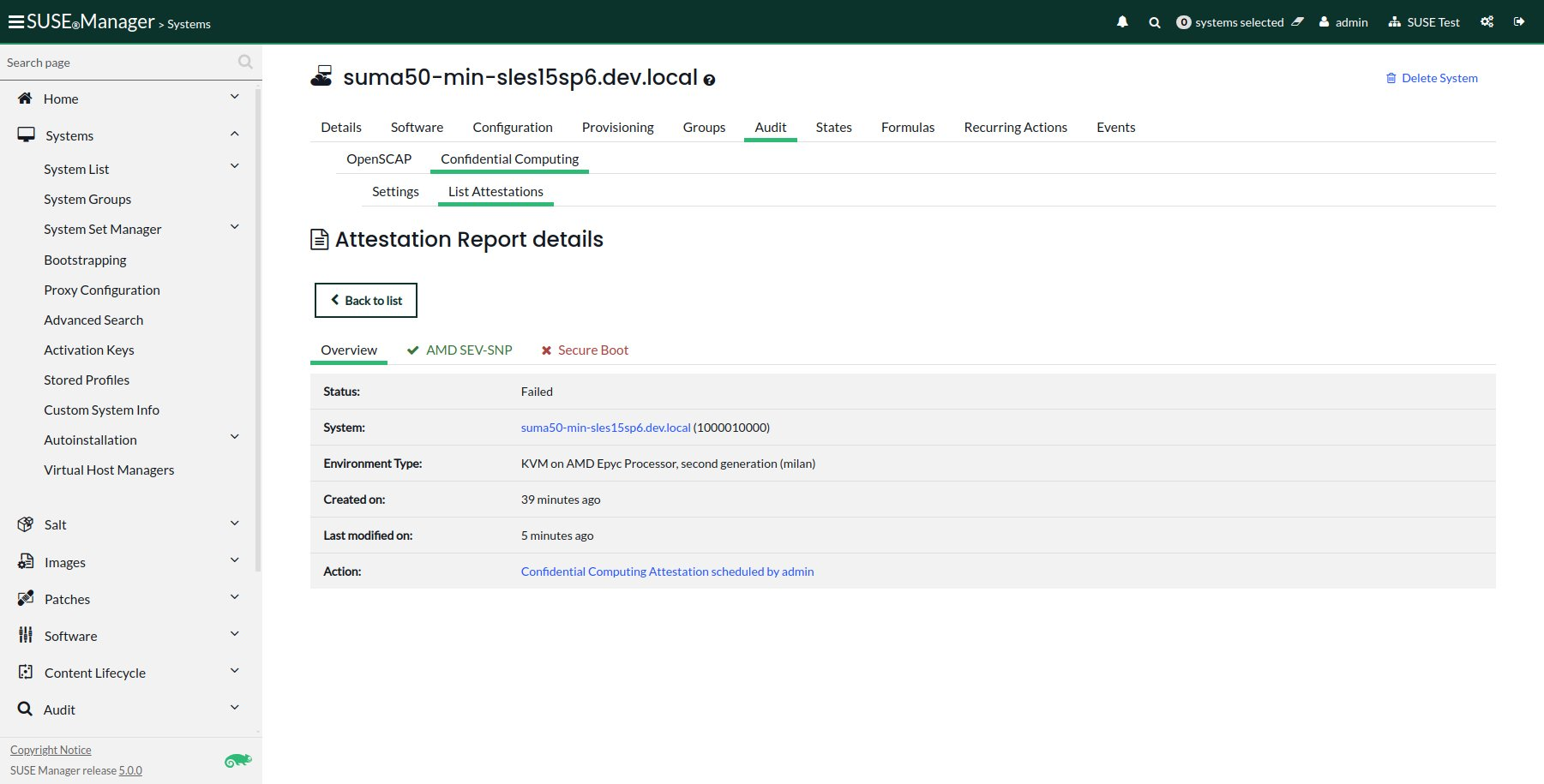
-
Move to the next tab
SEV-SNP.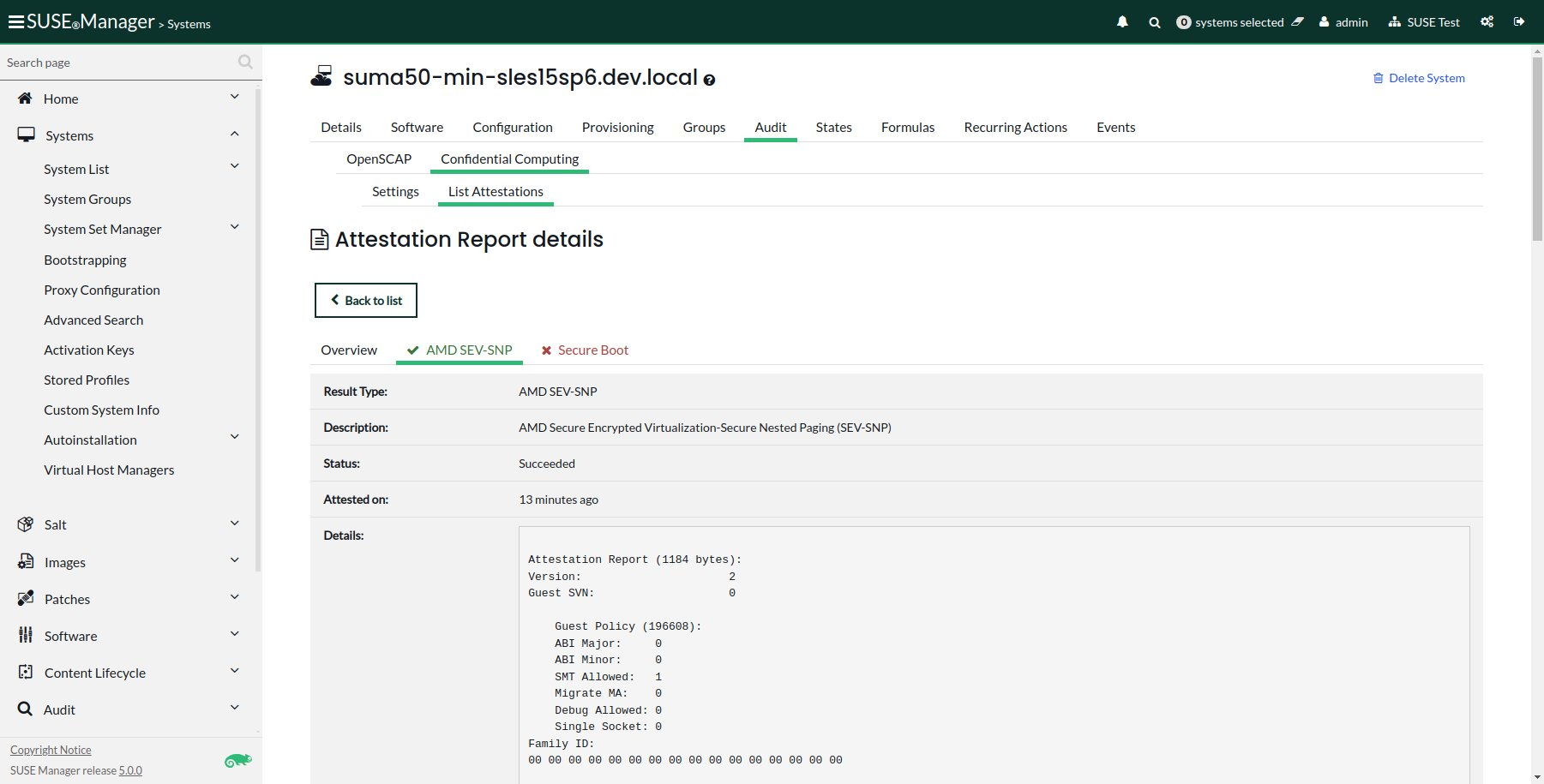
-
Finally, move to the next tab
Secure Boot.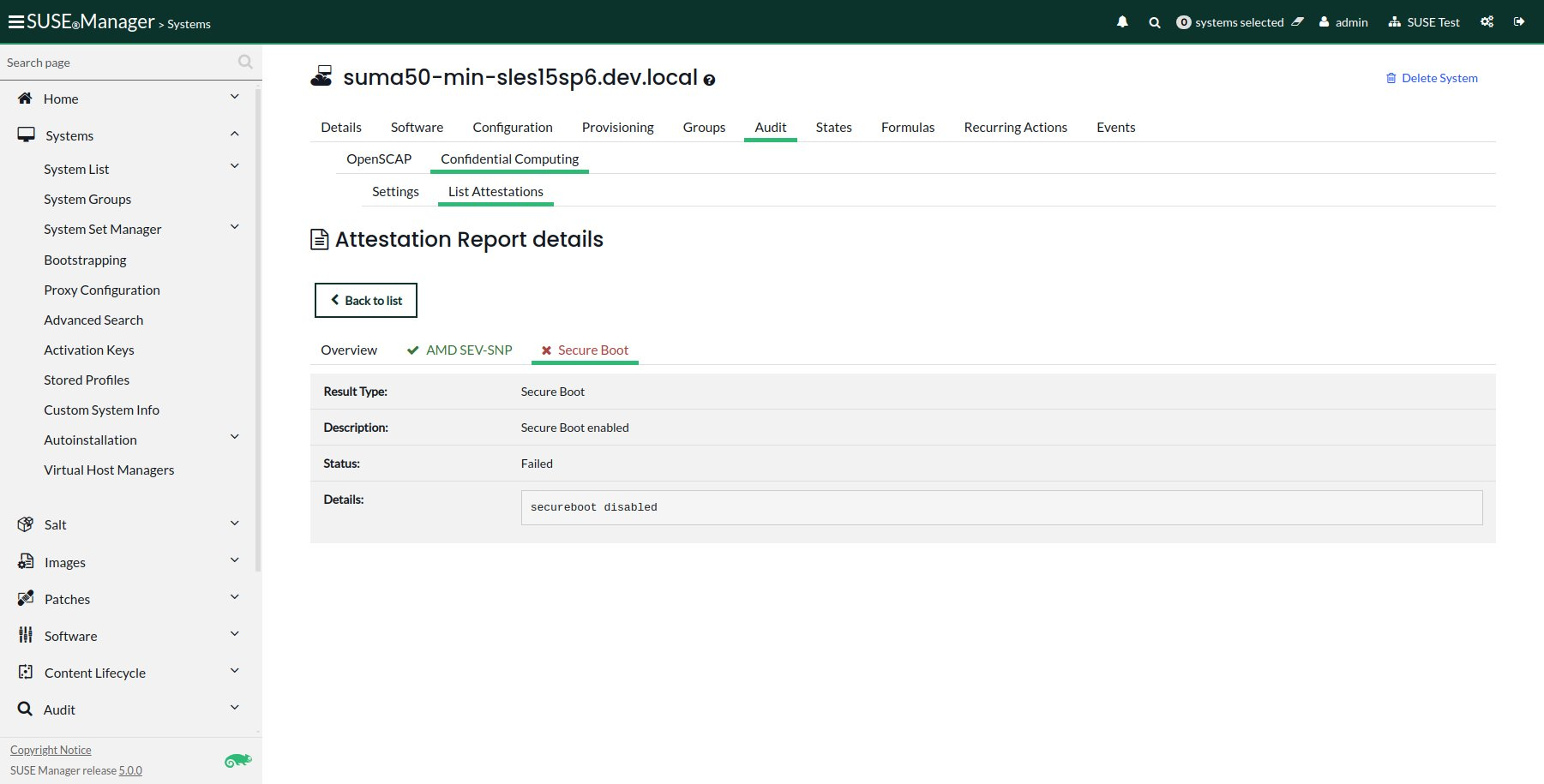
-
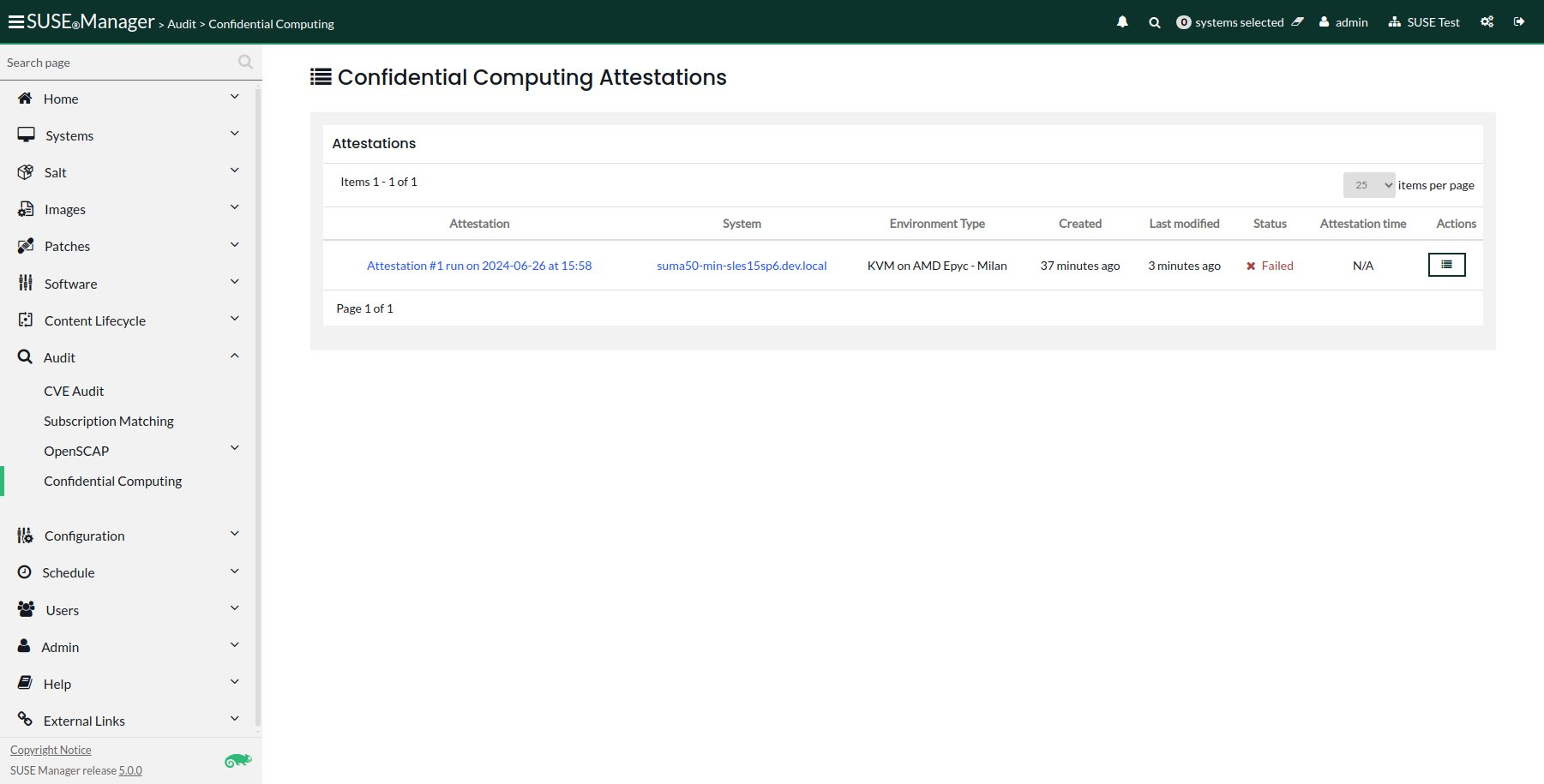
From the navigation bar, select .
-
The list of all attestations will be shown in the main panel.
-
Find and select the report you want to view.
4.1. Report Statuses
Attestation reports can have one of the following statuses:
- Pending
-
This is the default status of the scheduled attestation. The report is still not available, either because the process has not yet started or completed.
- Successful
-
When the scheduled attestation creates a report which can be viewed, the status of the process is
Successful. - Failed
-
When the scheduled fails and does not create a report as a result, the status of the process is
Failed.
5. Related Topics
-
For more information about Confidential Computing, see
https://confidentialcomputing.io(external link).