1. Generate Proxy Configuration
The configuration archive of the SUSE Manager Proxy is generated by the SUSE Manager Server. Each additional Proxy requires its own configuration archive.
For the containerized SUSE Manager Proxy, you must build a new proxy configuration file and then redeploy the container for the changes to take effect. This is the process for updating settings, including the SSL certificate.
|
2 GB represents the default proxy squid cache size. This will need to be adjusted for your environment. |
|
For Podman deployment, the container host for the SUSE Manager Proxy must be registered as a client to the SUSE Manager Server prior to generating this proxy configuration. |
If a proxy FQDN is used to generate a proxy container configuration that is not a registered client (as in the Kubernetes use case), a new system entry will appear in system list.
This new entry will be shown under previously entered Proxy FQDN value and will be of Foreign system type.
1.1. Generate the Proxy Configuration with Web UI
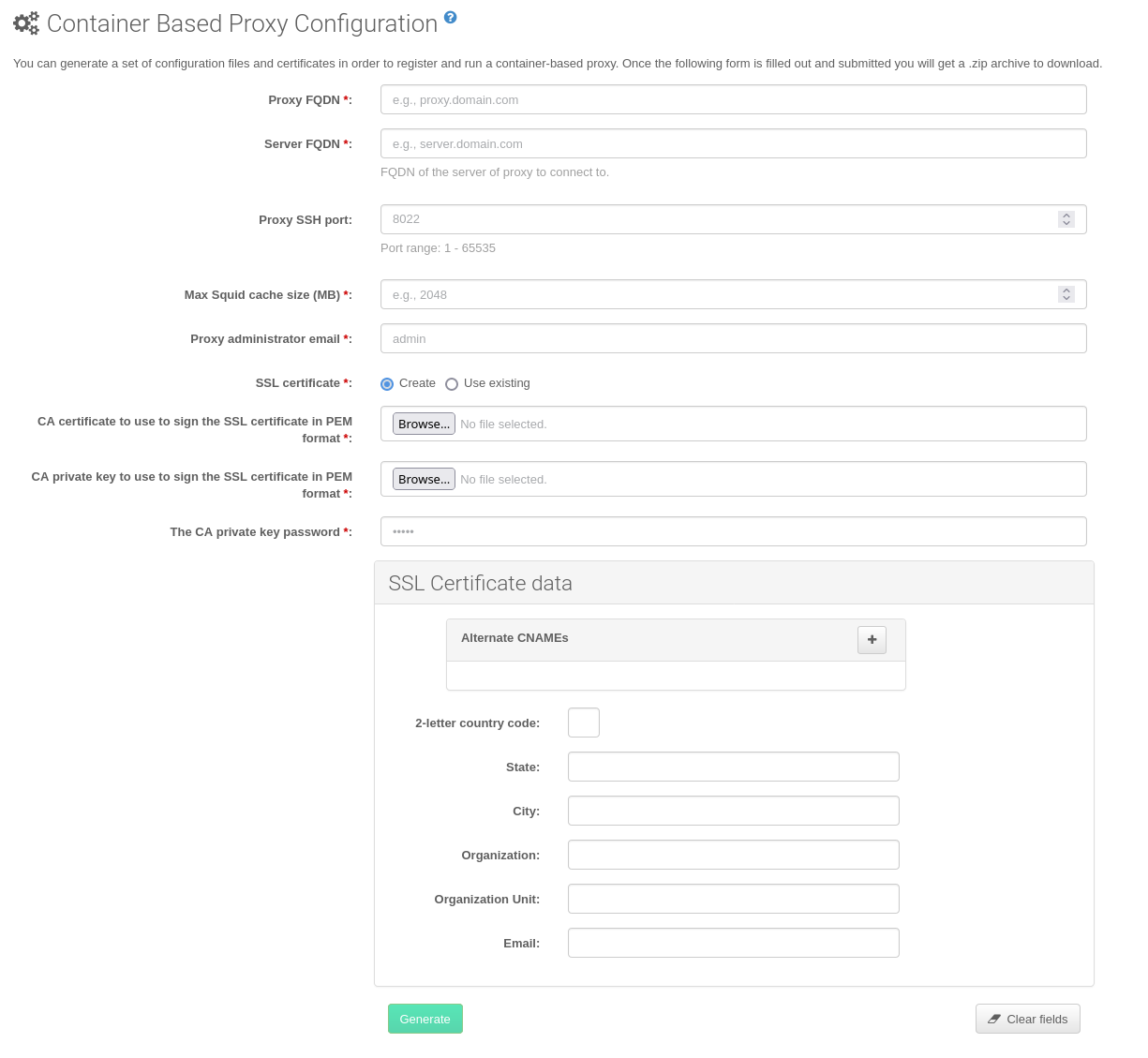
In the Web UI, navigate to and fill the required data.
In the
Proxy FQDNfield type fully qualified domain name for the proxy.In the
Parent FQDNfield type fully qualified domain name for the SUSE Manager Server or another SUSE Manager Proxy.In the
Proxy SSH portfield type SSH port on which SSH service is listening on SUSE Manager Proxy. Recommended is to keep default 8022.In the
Max Squid cache size [MB]field type maximal allowed size for Squid cache. Recommended is to use at most 80% of available storage for the containers.
2 GB represents the default proxy squid cache size. This will need to be adjusted for your environment.
In the
SSL certificateselection list choose if new server certificate should be generated for SUSE Manager Proxy or an existing one should be used. You can consider generated certificates as SUSE Manager builtin (self signed) certificates.Depending on the choice then provide either path to signing CA certificate to generate a new certificate or path to an existing certificate and its key to be used as proxy certificate.
The CA certificates generated by the server are stored in the
/var/lib/containers/storage/volumes/root/_data/ssl-builddirectory.For more information about existing or custom certificates and the concept of corporate and intermediate certificates, see Import SSL Certificates.
Click Generate to register a new proxy FQDN in the SUSE Manager Server and generate a configuration archive (
config.tar.gz) containing details for the container host.After a few moments you are presented with file to download. Save this file locally.
1.2. Generate the Proxy Configuration with spacecmd and Self-Signed Certificate
You can generate a Proxy configuration using spacecmd.
SSH into your container host.
Execute the following command replacing the Server and Proxy FQDN:
mgrctl exec -ti 'spacecmd proxy_container_config_generate_cert -- dev-pxy.example.com dev-srv.example.com 2048 email@example.com -o /tmp/config.tar.gz'Copy the generated configuration from the server container:
mgrctl cp server:/tmp/config.tar.gz .
1.3. Generate the Proxy Configuration with spacecmd and Custom Certificate
You can generate a Proxy configuration using spacecmd for a custom certificates rather than the default self-signed certificates.
SSH into your Server container host.
Execute the following command replacing the Server and Proxy FQDN:
for f in ca.crt proxy.crt proxy.key; do mgrctl cp $f server:/tmp/$f done mgrctl exec -ti 'spacecmd proxy_container_config -- -p 8022 pxy.example.com srv.example.com 2048 email@example.com /tmp/ca.crt /tmp/proxy.crt /tmp/proxy.key -o /tmp/config.tar.gz'Copy the generated configuration from the server container:
mgrctl cp server:/tmp/config.tar.gz .