SUSE Manager 5.0 Proxy Deployment on K3s
1. Installing K3s
|
SUSE Manager Proxy is supported on K3s running on top of SLE Micro in a single node cluster. If you need to deploy it in any other Kubernetes environment, please contact support for evaluation. |
On the container host machine, install K3s (replace <K3S_HOST_FQDN> with the FQDN of your K3s host):
curl -sfL https://get.k3s.io | INSTALL_K3S_EXEC="--tls-san=<K3S_HOST_FQDN>" sh -
2. Installing Tools
The installation requires the mgrpxy and helm packages.
The mgrpxy and helm packages are available in the SUSE Manager Proxy product repositories.
-
To install it run:
transactional-update pkg install helm mgrpxy
-
Reboot
2.1. Generate proxy configuration with Web UI
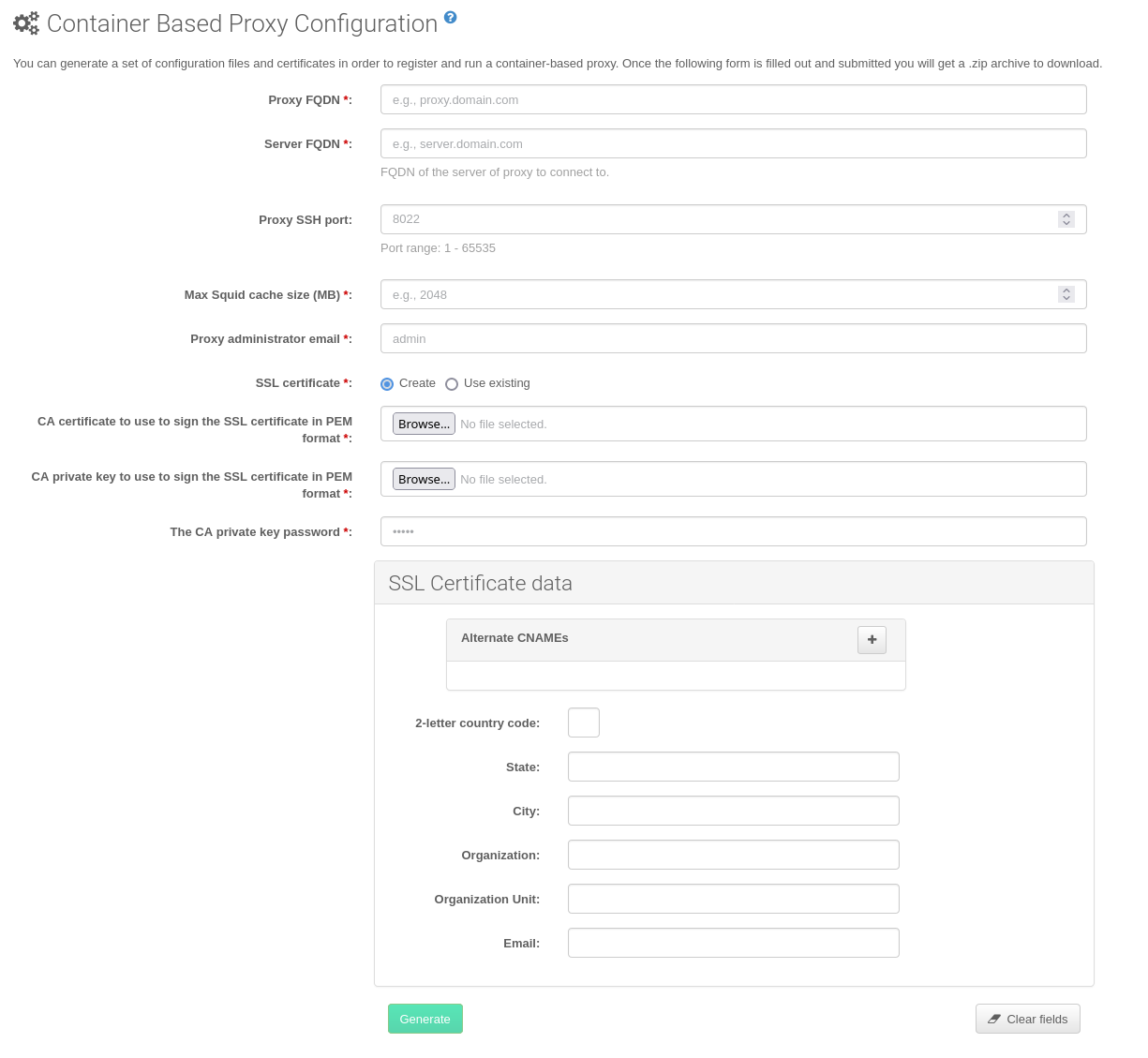
In the Web UI, navigate to and fill the required data.
In the
Proxy FQDNfield type fully qualified domain name for the proxy.In the
Parent FQDNfield type fully qualified domain name for the SUSE Manager Server or another SUSE Manager Proxy.In the
Proxy SSH portfield type SSH port on which SSH service is listening on SUSE Manager Proxy. Recommended is to keep default 8022.In the
Max Squid cache size [MB]field type maximal allowed size for Squid cache. Recommended is to use at most 80% of available storage for the containers.
2 GB represents the default proxy squid cache size. This will need to be adjusted for your environment.
In the
SSL certificateselection list choose if new server certificate should be generated for SUSE Manager Proxy or an existing one should be used. You can consider generated certificates as SUSE Manager builtin (self signed) certificates.Depending on the choice then provide either path to signing CA certificate to generate a new certificate or path to an existing certificate and its key to be used as proxy certificate.
The CA certificates generated by the server are stored in the
/var/lib/containers/storage/volumes/root/_data/ssl-builddirectory.For more information about existing or custom certificates and the concept of corporate and intermediate certificates, see Import SSL Certificates.
Click Generate to register a new proxy FQDN in the SUSE Manager Server and generate a configuration archive (
config.tar.gz) containing details for the container host.After a few moments you are presented with file to download. Save this file locally.
2.2. Generate proxy configuration with spacecmd and self-signed certificate
You can generate a Proxy configuration using spacecmd.
spacecmd and self-signed certificate
SSH into your container host.
Execute the following command replacing the Server and Proxy FQDN:
mgrctl exec -ti 'spacecmd proxy_container_config_generate_cert -- dev-pxy.example.com dev-srv.example.com 2048 email@example.com -o /tmp/config.tar.gz'Copy the generated configuration from the server container:
mgrctl cp server:/tmp/config.tar.gz .
2.3. Generate proxy configuration with spacecmd and custom certificate
You can generate a Proxy configuration using spacecmd for custom certificates rather than the default self-signed certificates.
spacecmd and custom certificate
SSH into your Server container host.
Execute the following commands replacing the Server and Proxy FQDN:
for f in ca.crt proxy.crt proxy.key; do mgrctl cp $f server:/tmp/$f done mgrctl exec -ti 'spacecmd proxy_container_config -- -p 8022 pxy.example.com srv.example.com 2048 email@example.com /tmp/ca.crt /tmp/proxy.crt /tmp/proxy.key -o /tmp/config.tar.gz'If your setup uses an intermediate CA, copy it as well and include it in the command with the
-ioption (can be provided multiple times if needed) :mgrctl cp intermediateCA.pem server:/tmp/intermediateCA.pem mgrctl exec -ti 'spacecmd proxy_container_config -- -p 8022 -i /tmp/intermediateCA.pem pxy.example.com srv.example.com 2048 email@example.com /tmp/ca.crt /tmp/proxy.crt /tmp/proxy.key -o /tmp/config.tar.gz'Copy the generated configuration from the server container:
mgrctl cp server:/tmp/config.tar.gz .
3. Deploying the SUSE Manager Proxy Helm Chart
To configure the storage of the volumes to be used by the SUSE Manager Proxy pod, define persistent volumes for the following claims. If you do not customize the storage configuration, K3s will automatically create the storage volumes for you.
The persistent volume claims are named:
-
squid-cache-pv-claim -
package-cache-pv-claim -
tftp-boot-pv-claim
Create the configuration for the SUSE Manager Proxy as documented in SUSE Manager 5.0 Proxy Deployment.
Copy the configuration tar.gz file and then install:
mgrpxy install kubernetes /path/to/config.tar.gz
For more information see https://kubernetes.io/docs/concepts/storage/persistent-volumes/ (kubernetes) or https://rancher.com/docs/k3s/latest/en/storage/ (K3s) documentation.