SUSE Manager 5.0 Proxy Deployment
This guide outlines the deployment process for the SUSE Manager 5.0 Proxy container on SLE Micro 5.5 or SUSE Linux Enterprise Server 15 SP6. This guide presumes you have already successfully deployed a SUSE Manager 5.0 Server.
|
SLE Micro is only supported as regular minion ( |
To successfully deploy, you will perform the following actions:
Review hardware requirements.
Synchronize the SLE Micro 5.5 or SUSE Linux Enterprise Server 15 SP6 parent channel and the proxy extension child channel on the server.
Install SLE Micro or SUSE Linux Enterprise Server on a bare-metal machine.
Create a Salt activation key with Proxy Extension.
Bootstrap the proxy as a client with the
defaultconnection method.Generate a proxy configuration.
Transfer the proxy configuration from server to proxy.
Install packages on the proxy.
Use the proxy configuration to register the client as a proxy with SUSE Manager.
|
Supported operating system for the Proxy Container Host
The supported operating system for the container host are SLE Micro 5.5 and SUSE Linux Enterprise Server 15 SP6.
|
1. Hardware Requirements for the Proxy
For more information about hardware requirements for deploying SUSE Manager Proxy, see installation-and-upgrade:hardware-requirements.adoc#proxy-hardware-requirements.
2. Synchronize the Parent and Proxy Extension Child Channels
This section presumes that you have already entered your organization credentials under the in the server’s Web UI.
Products are listed on the page.
This channel must be fully synchronized on the server, with the child channel Proxy as an extension option selected.
In the SUSE Manager Web UI select .
From the products page enter SLE Micro or SUSE Linux Enterprise Server in the filter field.
Next use the drop-down to select the required architecture. For this example x86-64.
In the
Product Descriptionfield select the SLE Micro 5.5 or SUSE Linux Enterprise Server 15 SP6 checkbox then use the drop-down to select theSUSE Manager Proxy Extension 5.0 x86_64extension.Click the Add products button.
Wait for the synchronization to complete.
3. Prepare SUSE Manager Proxy Host
In the following subsections, you either prepare the proxy host with SLE Micro or SUSE Linux Enterprise Server.
3.1. Prepare SLE Micro 5.5 Host
3.1.1. Download the installation media
Locate the SLE Micro 5.5 installation media at https://www.suse.com/download/sle-micro/.
Download
SLE-Micro-5.5-DVD-x86_64-GM-Media1.iso.Prepare a DVD or USB flash drive with the downloaded
.isoimage for installation.
3.1.2. Install SLE Micro 5.5
Insert the DVD or USB flash drive (USB disk or key) containing the installation image for SLE Micro 5.5.
Boot or reboot your system.
Use the arrow keys to select
Installation.Adjust Keyboard and language.
Click the
checkboxto accept the license agreement.Click
Nextto continue.Skip the registration. The SLE Micro 5.5 entitlement is included within the SUSE Manager entitlement.
Click Next to continue.
On the
NTP Configurationpage click Next.On the
Authentication for the Systempage enter a password for the root user. Click Next.On the
Installation Settingspage click Install.
This concludes installation of SLE Micro 5.5. For more information about preparing your machines (virtual or physical), see SLE Micro 5.5 Deployment Guide.
To continue with deployment, see Configure Custom Persistent Storage.
3.2. Prepare SUSE Linux Enterprise Server 15 SP6 Host
Alternatively, you can deploy SUSE Manager on SUSE Linux Enterprise Server 15 SP6.
The following procedure describes the main steps of the installation process.
Locate and download SUSE Linux Enterprise Server 15 SP6
.isoat https://www.suse.com/download/sles/.Make sure that you have registration codes both for the host operating system (SUSE Linux Enterprise Server 15 SP6) and extensions.
Start the installation of SUSE Linux Enterprise Server 15 SP6.
On the
Language, keyboard and product selectionselect the product to install.On the
License agreementread the agreement and checkI Agree to the License Terms.Skip the registration.
Click
Nextto continue.
Please note that for SUSE Linux Enterprise Server 15 SP6, you are required to have a valid SUSE Linux Enterprise Server subscription configured on the server.
In the screen
Extensions and Modules Selectioncheck the following:
Basesystem Module
Containers Module
Complete the installation.
When the installation completes, log in to the newly installed server as root.
To continue with deployment, see Configure Custom Persistent Storage.
4. Configure Custom Persistent Storage
Configuring persistent storage is optional, but it is the only way to avoid serious trouble with container full disk conditions.
If custom persistent storage is required for your infrastructure, use the mgr-storage-proxy tool.
-
For more information, see
mgr-storage-proxy --help. This tool simplifies creating the container storage and Squid cache volumes.
Use the command in the following manner:
mgr-storage-proxy <storage-disk-device>For example:
mgr-storage-proxy /dev/nvme1n1|
This command will create the persistent storage volumes at For more information, see |
5. Create an Activation Key for the Proxy
Navigate to , and click Create key.
Create an activation key for the proxy host with SLE Micro 5.5 or SUSE Linux Enterprise Server 15 SP6 as the parent channel. This key should include all recommended channels and the proxy as an extension child channel.
Proceed to boostrapping the proxy host as a
defaultclient.
6. Bootstrap the Proxy Host as a Client
Select .
Fill in the fields for your proxy host.
Select the activation key created in the previous step from the drop-down.
Click Bootstrap.
Wait for the bootstrap process to complete successfully. Check the Salt menu and confirm the Salt key is listed and accepted.
Reboot the proxy host if the operating system is SLE Micro.
Select the host from the System list and trigger a second reboot in case of SLE Micro after all events are finished to conclude the onboarding.
Select the host from the Systems list and apply all patches to update it.
Reboot the proxy host if the operating system is SLE Micro.
7. Generate proxy configuration
The configuration archive of the SUSE Manager Proxy is generated by the SUSE Manager Server. Each additional Proxy requires its own configuration archive.
For the containerized SUSE Manager Proxy, you must build a new proxy configuration file and then redeploy the container for the changes to take effect. This is the process for updating settings, including the SSL certificate.
|
2 GB represents the default proxy squid cache size. This will need to be adjusted for your environment. |
|
For Podman deployment, the container host for the SUSE Manager Proxy must be registered as a client to the SUSE Manager Server prior to generating this proxy configuration. |
If a proxy FQDN is used to generate a proxy container configuration that is not a registered client (as in the Kubernetes use case), a new system entry will appear in system list.
This new entry will be shown under previously entered Proxy FQDN value and will be of Foreign system type.
|
Peripheral servers are always using third-party SSL certificates. If the hub server has generated the certificates for the peripheral server, it needs to generate the certificate of each proxy too. On the hub server, run the following command. The files to use will be
|
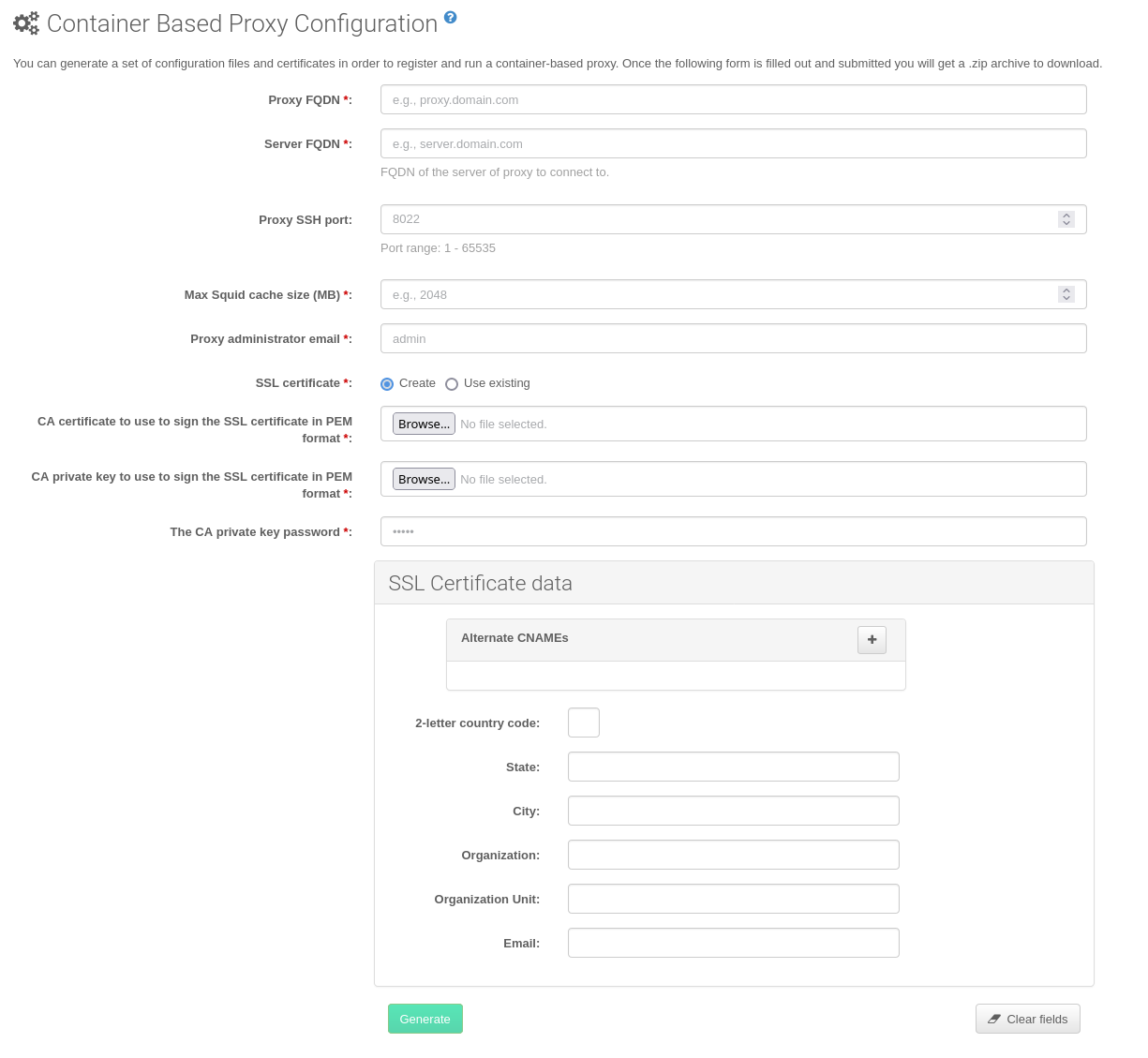
7.1. Generate proxy configuration with Web UI
In the Web UI, navigate to and fill the required data.
In the
Proxy FQDNfield type fully qualified domain name for the proxy.In the
Parent FQDNfield type fully qualified domain name for the SUSE Manager Server or another SUSE Manager Proxy.In the
Proxy SSH portfield type SSH port on which SSH service is listening on SUSE Manager Proxy. Recommended is to keep default 8022.In the
Max Squid cache size [MB]field type maximal allowed size for Squid cache. Recommended is to use at most 80% of available storage for the containers.
2 GB represents the default proxy squid cache size. This will need to be adjusted for your environment.
In the
SSL certificateselection list choose if new server certificate should be generated for SUSE Manager Proxy or an existing one should be used. You can consider generated certificates as SUSE Manager builtin (self signed) certificates.Depending on the choice then provide either path to signing CA certificate to generate a new certificate or path to an existing certificate and its key to be used as proxy certificate.
The CA certificates generated by the server are stored in the
/var/lib/containers/storage/volumes/root/_data/ssl-builddirectory.For more information about existing or custom certificates and the concept of corporate and intermediate certificates, see Import SSL Certificates.
Click Generate to register a new proxy FQDN in the SUSE Manager Server and generate a configuration archive (
config.tar.gz) containing details for the container host.After a few moments you are presented with file to download. Save this file locally.
7.2. Generate proxy configuration with spacecmd and self-signed certificate
You can generate a Proxy configuration using spacecmd.
spacecmd and self-signed certificate
SSH into your container host.
Execute the following command replacing the Server and Proxy FQDN:
mgrctl exec -ti 'spacecmd proxy_container_config_generate_cert -- dev-pxy.example.com dev-srv.example.com 2048 email@example.com -o /tmp/config.tar.gz'Copy the generated configuration from the server container:
mgrctl cp server:/tmp/config.tar.gz .
7.3. Generate proxy configuration with spacecmd and custom certificate
You can generate a Proxy configuration using spacecmd for custom certificates rather than the default self-signed certificates.
spacecmd and custom certificate
SSH into your Server container host.
Execute the following commands replacing the Server and Proxy FQDN:
for f in ca.crt proxy.crt proxy.key; do mgrctl cp $f server:/tmp/$f done mgrctl exec -ti 'spacecmd proxy_container_config -- -p 8022 pxy.example.com srv.example.com 2048 email@example.com /tmp/ca.crt /tmp/proxy.crt /tmp/proxy.key -o /tmp/config.tar.gz'If your setup uses an intermediate CA, copy it as well and include it in the command with the
-ioption (can be provided multiple times if needed) :mgrctl cp intermediateCA.pem server:/tmp/intermediateCA.pem mgrctl exec -ti 'spacecmd proxy_container_config -- -p 8022 -i /tmp/intermediateCA.pem pxy.example.com srv.example.com 2048 email@example.com /tmp/ca.crt /tmp/proxy.crt /tmp/proxy.key -o /tmp/config.tar.gz'Copy the generated configuration from the server container:
mgrctl cp server:/tmp/config.tar.gz .
8. Transfer the Proxy Configuration
The Web UI generates a configuration archive. This archive needs to be made available on the proxy container host.
If not already done, copy the configuration archive (
config.tar.gz) generated in the previous step from the server container to the server host:mgrctl cp server:/root/config.tar.gz .If not already done, copy the files from the server host to the proxy host:
scp config.tar.gz <proxy-FQDN>:/root
9. Install packages and enable podman
Before using proxy, some packages need to be present on host and podman needs to be running.
On the proxy host, ensure that the following packages are installed:
podman
mgrpxy-bash-completion
suse-manager-5.0-x86_64-proxy-salt-broker-image
suse-manager-5.0-x86_64-proxy-ssh-image
suse-manager-5.0-x86_64-proxy-tftpd-image
suse-manager-5.0-x86_64-proxy-httpd-image
suse-manager-5.0-x86_64-proxy-squid-imageStart the Podman service on the proxy host by rebooting the system, or running a command:
systemctl enable --now podman.serviceOn the proxy host, install the Proxy with:
mgrpxy install podman config.tar.gz
10. Start the SUSE Manager Proxy
Container can now be started with the mgrpxy command:
Start the proxy by calling:
mgrpxy startCheck container status by calling:
mgrpxy statusFive SUSE Manager Proxy containers should be present and should be part of the
proxy-podcontainer pod:
proxy-salt-broker
proxy-httpd
proxy-tftpd
proxy-squid
proxy-ssh
11. Use a Custom Container Image for a Service
By default, the SUSE Manager Proxy suite is configured to use the same image version and registry path for each of its services.
However, it is possible to override the default values for a specific service using the install parameters ending with -tag and -image.
For example:
mgrpxy install podman --httpd-tag 0.1.0 --httpd-image registry.opensuse.org/uyuni/proxy-httpd /path/to/config.tar.gzIt adjusts the configuration file for the httpd service, where registry.opensuse.org/uyuni/proxy-httpds is the image to use and 0.1.0 is the version tag, before restarting it.
To reset the values to defaults, run the install command again without those parameters:
mgrpxy install podman /path/to/config.tar.gzThis command first resets the configuration of all services to the global defaults and then reloads it.